Organizations need to achieve multiple objectives with their security data, with perhaps the most important being:
- threat detection
- threat investigation
- regulatory compliance
Threat detection often drives data storage decisions for the other two–if not all–security objectives, with SIEM products serving as a general security data storage hub. This approach to storage leads to common and recurring frustrations, such as:
- You need to comply with annual log retention policies, but your SIEM only retains logs for three months
- Most of the logs you’re storing in your expensive SIEM do not contribute to threat detection
- Neither your team nor your security service provider can efficiently query historical data during investigations and threat hunts
Not all data sources are equally valuable, and they shouldn’t be priced that way. That is why we are excited to announce the Red Canary Security Data Lake, a centralized and scalable repository for storing your high-volume, low-detection-value security data at a reasonable rate.
How it works
Set up integrations in minutes
If you can forward your logs to an AWS S3 bucket, or a Syslog server, you can add it to the Security Data Lake. We’ve tallied 200+ supported integrations spanning security products, cloud service providers, productivity software, and more.
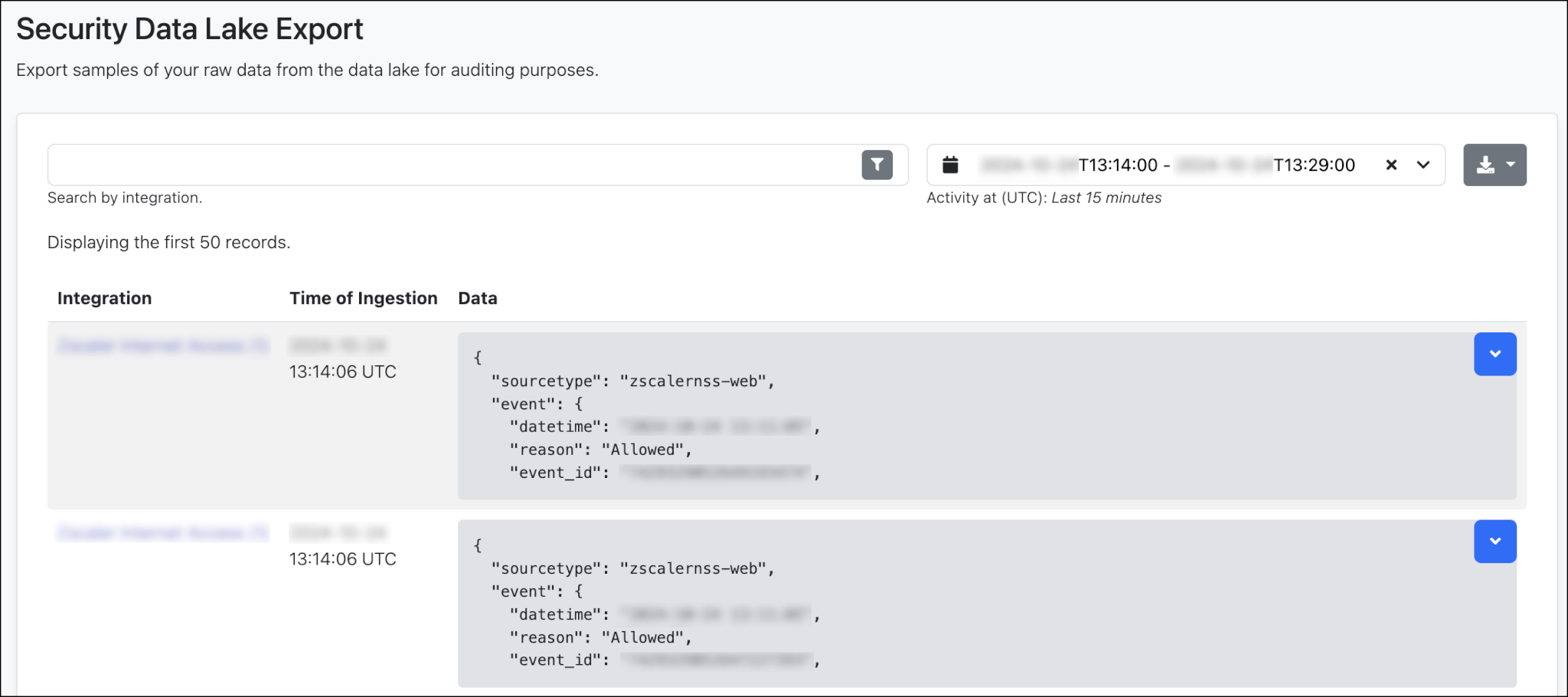
Demonstrate compliance
In many cases, just taking a screenshot is sufficient to prove certain logs are retained, but should you need to prove data retention to an auditor, we make it easy to find those logs and export.
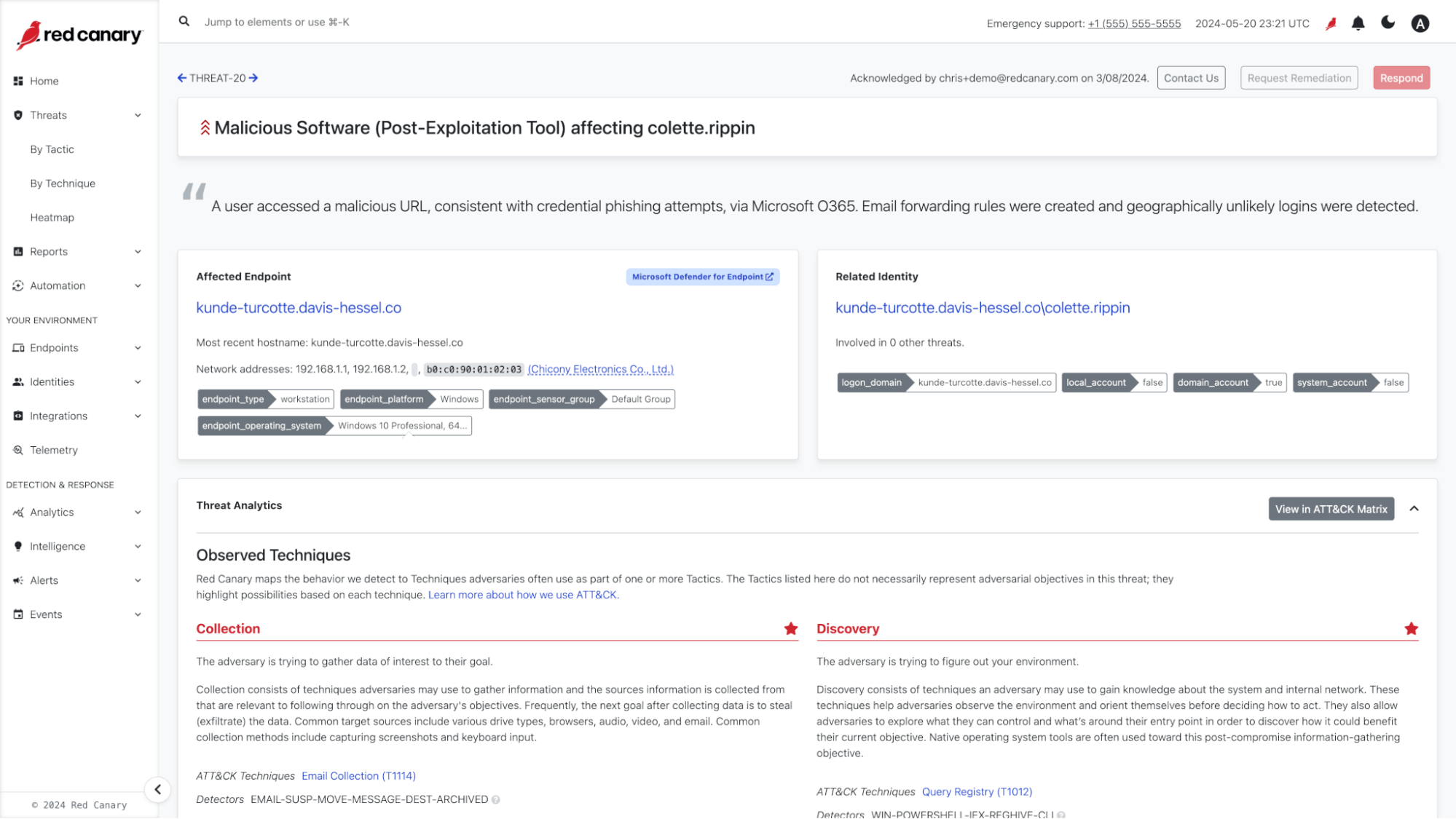
Investigate your data
You can write SQL queries directly against your supported data sources within the Red Canary platform. Search across all your logs for specific events, answer questions like “Is this normal or anomalous?”, aggregate data to identify trends, and perform complex analysis to uncover hidden threats—all with the familiar and powerful language of SQL.
Supercharge your MDR (coming soon)
Starting in Q3 in 2025, Red Canary analysts will be able to leverage your data in the Security Data Lake during MDR investigations. Over the course of this year, we will optimize our investigation workflows to leverage stored data throughout the detection and response lifecycle.
So what does this mean for you?
It means fewer dollars wasted. It means faster, more effective threat hunting and incident response. It means deeper, more actionable insights into your security posture.