Malicious macOS installers
Malicious installers led to rotten Apples and adware, as adversaries continued to target macOS throughout 2021.
Editors’ note: While the analysis and detection opportunities remain applicable, this page has not been updated since 2022.
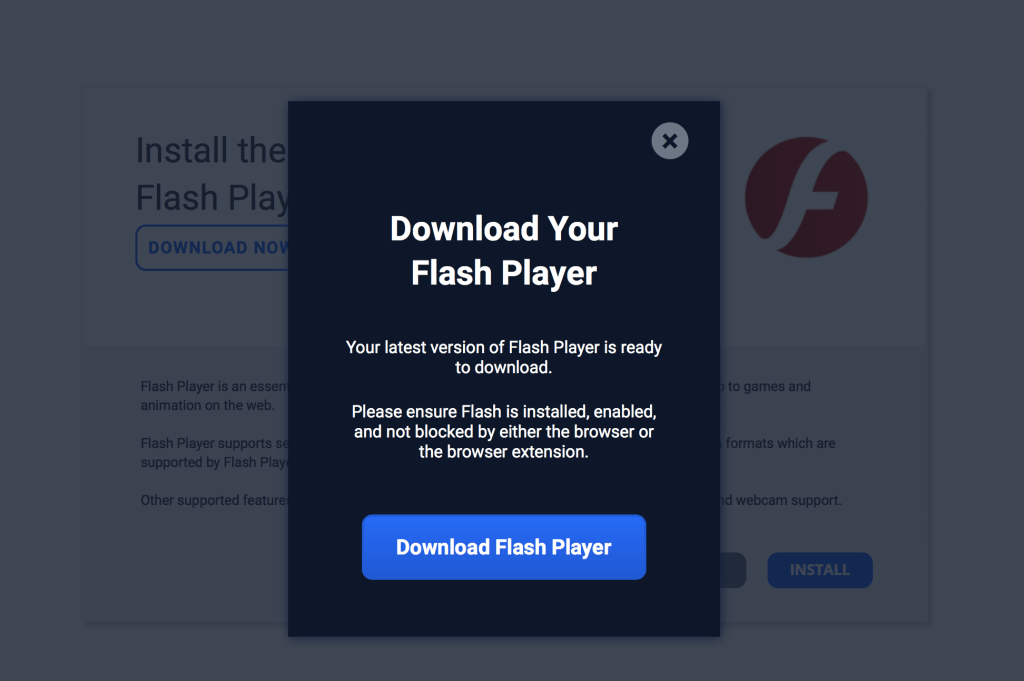
We’ve come a long way from hearing cries of “Macs don’t get viruses!,” and in 2021, the information security community saw more and more malware targeting macOS systems. In contrast to Windows systems, we observe far fewer malicious documents or email attachments on macOS systems. Instead, the majority of malware we observe on macOS stems from malicious installers that trick victims into thinking they’re downloading legitimate content. This approach is particularly insidious, as victims on macOS systems usually possess administrative privileges. Shlayer, Bundlore, and Silver Sparrow followed this malicious installer trend. Also, four of the eight macOS malware threats Objective-See covered in their review of 2021 relied on malicious installers for deployment.
Updating the operating system and applying antimalware controls are the best defenses against malicious software on macOS. Patching to the latest version possible ensures that malware exploits are less likely to succeed. Malware authors still circulate versions of installers that exploit patched vulnerabilities, knowing that not everyone can patch their macOS system. Antimalware controls help mitigate this threat. Where possible, obtain software directly from trusted sources that sign the installers and seek notarization from Apple. Malicious software has been mistakenly notarized in the past, but each case has been rapidly found and remedied.