Detecting Snake malware may be difficult as Snake is a relatively complex framework that includes persistence, information stealing, and communications modules among other capabilities. When researchers at Fox-IT announced the porting of the Snake malware framework from Windows to the Mac platform, we had a need to look retrospectively across our customer base to identify any potential Snake malware victims. The fastest way to do this was via our Surveyor utility.
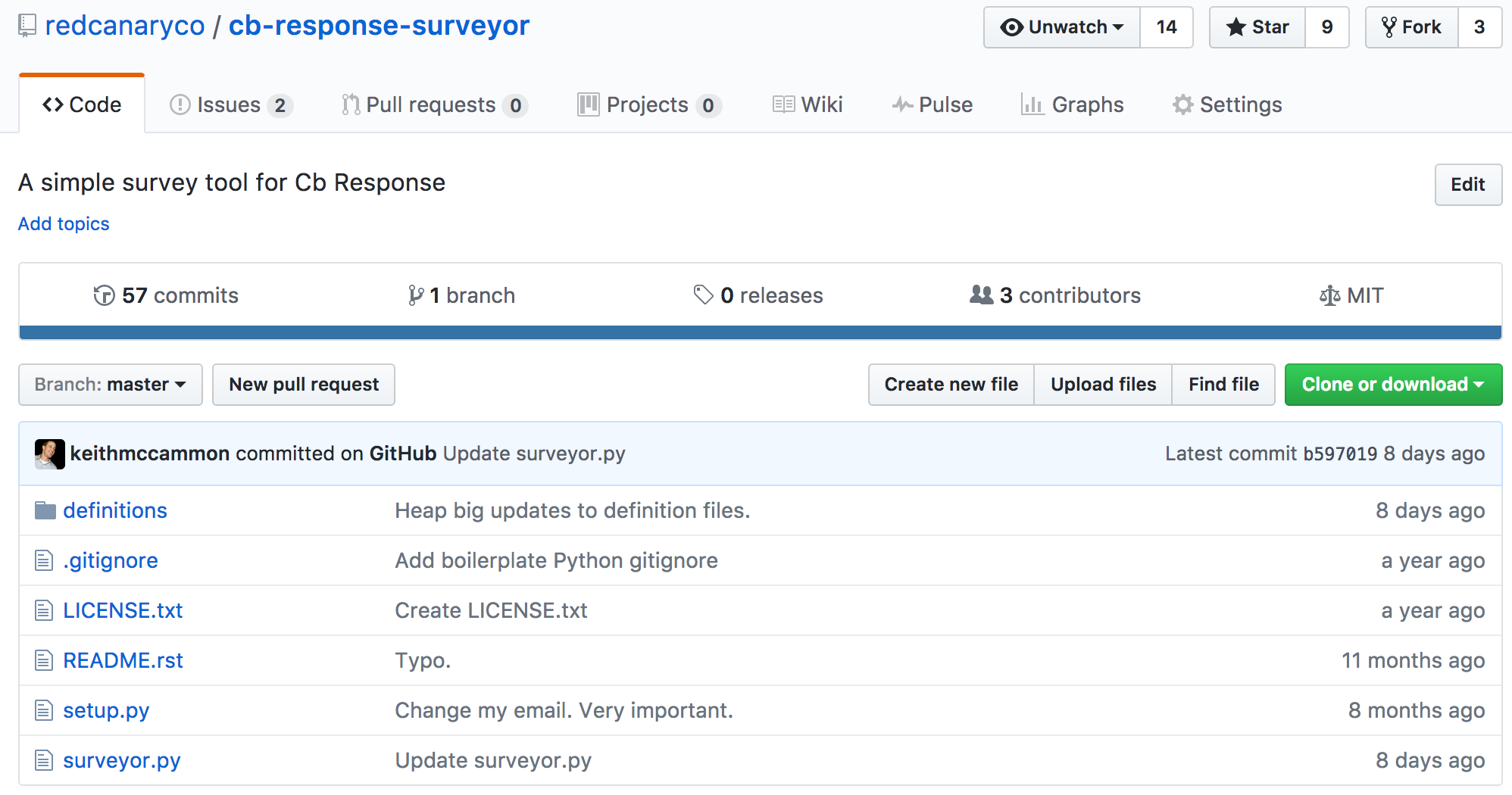
Surveyor is an open source utility maintained by Red Canary, its purpose being rapid identification of systems associated with a set of indicators or behaviors using telemetry collected from Carbon Black Response. It does not aim to enumerate hundreds or thousands of matching processes, but rather to answer the simple question “Have we seen this thing, and if so where?”
The first step in detecting Snake malware via Surveyor was to create a simple definition file based on Fox-IT’s report:
{
"Snake Files": {
"filemod": [".gdm-selinux",
".gdm-socket",
".ur-*",
"/Library/Scripts/queue",
"/Library/Scripts/installd.sh",
"/Library/LaunchDaemons/com.adobe.update.plist"]
},
"Snake Network": {
"domain": ["car-service.effers.com"]
},
"Snake IP": {
"ipaddr": ["83.229.87.11"]
},
"Snake Persistence": {
"cmdline": ["com.adobe.update.plist"]
}
}
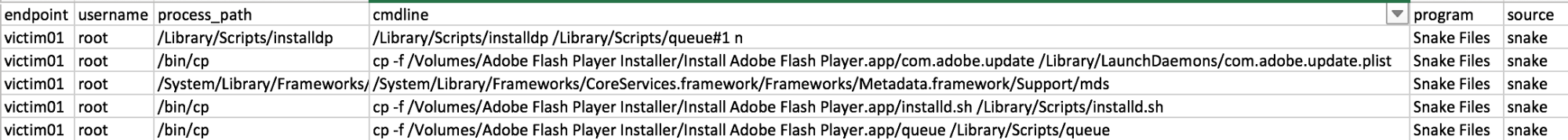
When we run this against an organization with an endpoint infected with Snake malware it will look something like this:
The cp commands are artifacts of install.sh, and the installdp process is the actual initialization routine.
Techniques for Detecting Snake Malware
This is a very crude first pass, and if you’re running Cb Response and sending data into a SIEM or other logging system then it should be possible to look for later-stage behaviors associated with persistence and even other parts of the installation and/or initialization routines. And if you’re a Cb Response shop but aren’t set up for API access, the definition file entries can be easily converted into queries and alerted on via watchlists:
filemod:".gdm-selinux" OR filemod:".gdm-socket" OR filemod:".ur-*" OR filemod:"/Library/Scripts/queue" OR filemod:"/Library/Scripts/installd.sh" OR filemod:"/Library/LaunchDaemons/com.adobe.update.plist"
As is the case with many otherwise capable malware families, they still have to execute, persist, and communicate. This is a great example of a malware framework that, once installed and its operator(s) entrenched, may be more difficult to detect. But initial installation and persistence are very detectable, and retrospective analysis can effectively find existing victims.