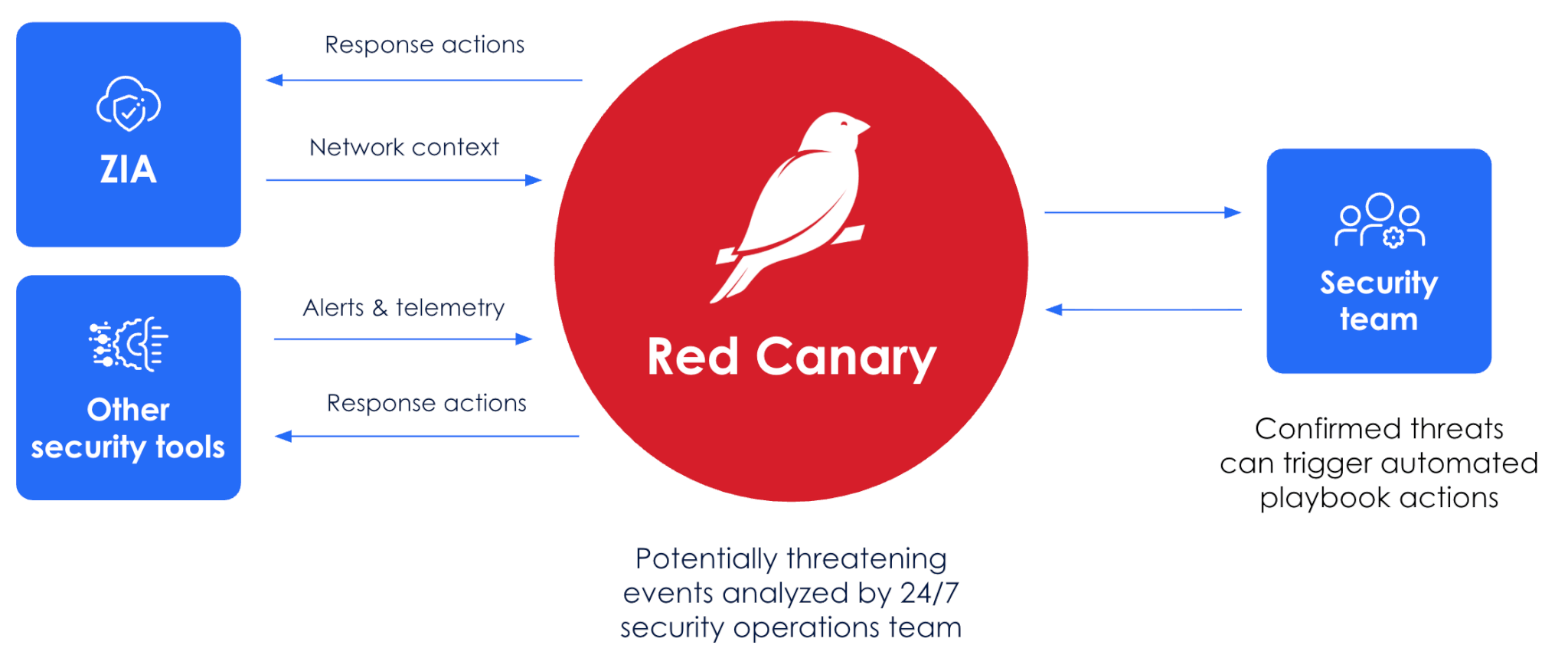
Red Canary integrates with Zscaler to accelerate investigations and give you the quickest path from detection to protection.
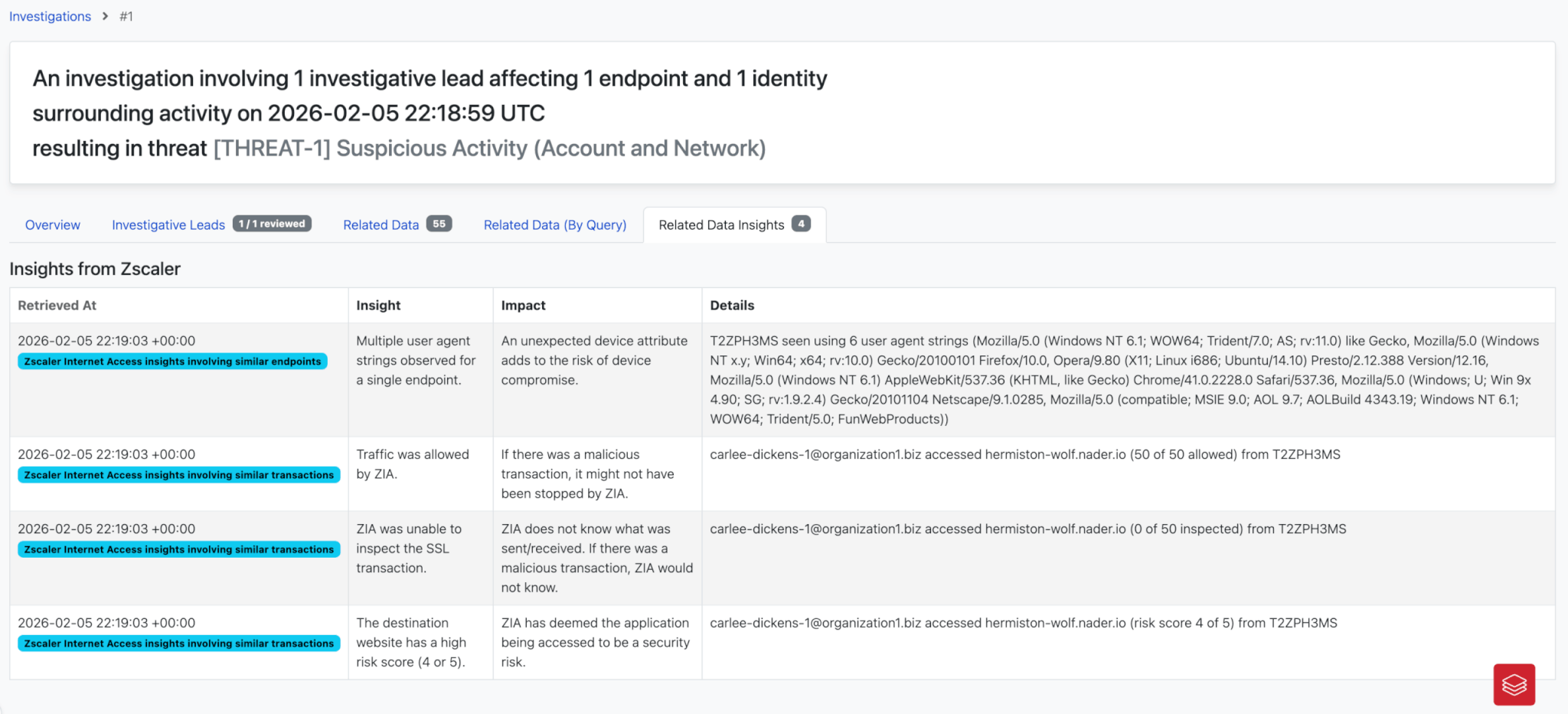
Quicker context for investigations
See relevant ZIA web logs and insights directly in Red Canary—eliminating console-hopping, filtering out activity ZIA already blocked, and giving analysts the context they need to quickly validate true threats.
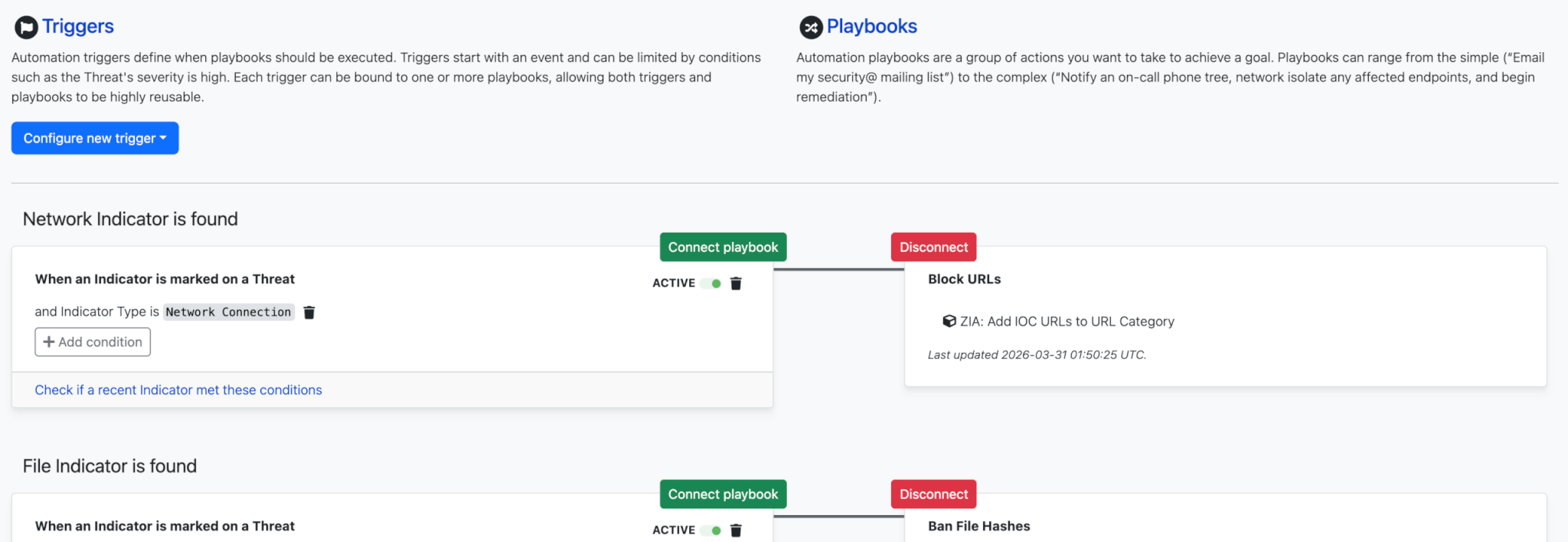
Trigger network-level protection
Initiate ZIA response actions from Red Canary or set them to trigger automatically.
- Add domains, URLs, or IPs to block lists
- Apply browser isolation or conditional access policies
- Add malicious file hashes to the ZIA Sandbox denylist
The benefits
Accelerate investigations
Make the jump from “logs” to “insights” without swiveling
Streamline response
Take the quickest path from detection to protection
Focus on true positives
Immediately see if ZIA has already blocked activity
Newly Released