Customers consistently tell us that one of the things they find most beneficial about Red Canary is our incident handling team. Every Red Canary incident handler has real-world security experience. They act as an extension of our customers’ teams by supporting incident response efforts, answering questions about detections, and providing guidance on remediation. Best of all, they’re driven by helping make security better, not by sales metrics.

Without further ado: meet Joe Casazza, the latest addition to the Red Canary incident handling team.
Joe is an experienced security professional with a knack for problem-solving, communication, and solution delivery. He joined Red Canary from Bridgepoint Education, where he spent three years running the security program in increasingly advanced roles as an information security engineer. Prior to that he performed vulnerability assessments and remediation for Qualcomm, a Fortune 500 company that designs and manufactures digital telecom products and services. We sat down with Joe to learn more about his background, skillset, goals, and interests.
You spent several years as a security engineer, and had great success in that field. Tell us a little about your role and what led you to look at becoming an incident handler.
I previously ran the security program at Bridgepoint Education, an organization that serves tens of thousands of students. My focus was on incident response planning, investigation of security breaches, threat triage, risk mitigation, and internal and external information security compliance audits and assessments. I continually progressed into more advanced security roles and reached a point where I wanted to experience a different kind of threat landscape.
I started asking myself questions like: What are my goals in security? What do I want to accomplish? I quickly realized that I wasn’t driven by “being the best” or having a “cool job,” but by making security better.
Then I started asking questions like: How can I take what I’ve learned in security over the last ten years and use it to help other organizations? How can I make the biggest impact for the greatest amount of people?
What was it about Red Canary’s incident handler role that excited you?
I wanted to contribute to something great. I first considered a Red Canary security analyst role because I knew the analysts were of high caliber. Then I met with Mike Haag and talked about my goals and passions, and he recommended an incident handler position. It sounded like my dream job.
We ran through scenarios of working side-by-side with IT Security managers and security teams. Being an incident handler would give me the opportunity to directly help customers improve threat detection, advise them in the midst of an attack, guide technology decisions, plus do threat hunting and dive into investigations. Understanding what happens during an attack is one thing, but I was really excited about the opportunity to explain the risk to a customer and work together to find ways to improve their security.
What do you think contributes to success in the security field?
You need to always be driven by continuing to grow technically. For example, when I was doing vulnerability assessments at Qualcomm, I did research every night at home to hone my skills. Nessus was an open-sourced, reputable free tool that did vulnerability assessments, so I could stand up random things on my home network, scan things, and learn. I talked to friends about things like open lab builds and open-sourced web app testing criteria. I learned so much. Not just from a technology perspective, but also learning the terms and metrics you need to document and report. Each report got easier and I progressively got better; failure drove my progress.
Ultimately, I think you need to be perpetually curious and have a willingness to put in the time and do the work. I remember one time, someone came up to me on a Friday afternoon and said, “Sorry Joe, I don’t mean to ruin your Friday, but…”
What’s something you’re most proud of in your career?
There was one time when I was going to meet my friends in Las Vegas for the Fourth of July. I was all packed and ready to go, six-pack of Red Bulls in hand. Just before I left for the airport, I got an alert. I thought: That looks like it might be bad, I should really take a look. The alert turned into a three-day DDOS attack. I was so engrossed in mitigating issues that I forgot to tell my friends I wasn’t coming. I didn’t even care about the trip anymore. I think that’s when I thrive. When it’s a holiday or the middle of the night and you drop everything to help resolve a crisis—not because you have to, but because you love your job that much.
What advice do you have for people who want to get into cybersecurity?
Don’t focus on the experience you don’t have; focus on the skills you do have and how to keep developing them. A mentor once told me, “Success depends on aptitude and attitude.” Getting into cybersecurity or any other industry is not about getting a specific position. It’s about having the right aptitude and attitude, and putting yourself in a position to take advantage of an opportunity that presents itself. You want be a hacker? Go finish Violent Python and get back to me when you’re done. It teaches how Python works and how to apply it to breaking things. Making security better is all about understanding how attacks work so you can defend against them.
Read How to Get Into Information Security for practical advice from Red Canary’s SOC leader and hiring manager.
If you have a willingness to learn and a drive to achieve, those instincts will put you in a position to take advantage of any opportunity. You might start with the Geek Squad or doing vulnerability analysis or writing reports. It might not be what you ultimately want to do, but you need to continuously put yourself in a position to take advantage of the opportunities that present themselves, and eventually you’ll get where you want to go.
And make sure you’re getting into cybersecurity for the right reasons. I enjoy cybersecurity; I love it and do it all the time. It’s never been about anything but that. It’s not about being “cool” or about getting into a lucrative industry. Those are the wrong reasons to get into security. Sure, everyone wants to make money, but you have to enjoy it. It’s a 24/7 job. I get woken up at two in the morning and I’m not upset. I’m like, “It’s go time. Let’s do this.”
What’s one thing people might be surprised to learn about you?
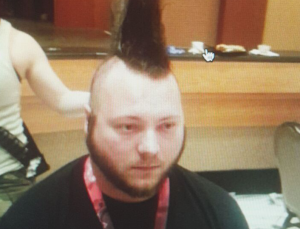
I used to have a mohawk. I originally got it at DEFCON to support the EFF and Hackers for Charity, but I ended up keeping it for a year.
I had it in all my brother’s wedding photos but he wouldn’t let me spike it, so it looked hilarious and sad at the same time.