Security service providers play an outsized role in an organization’s defense. In a recent blog post, Forrester analyst Jeff Pollard goes as far as to suggest that security leaders should “start buying services, then products.” In a similar vein, a Red Canary customer recently noted that, “We have vendors that we buy things [from], and they’re very important and we like them quite a bit…but we don’t stress about them as much as we do an MSSP, because that’s more an ally than a vendor.”
With over 100 MDR providers as of late last year, the market needs trustworthy ways to identify top offerings. That is why we’re extremely proud that Red Canary MDR is the inaugural solution verified by Microsoft to deliver managed extended detection and response, or MXDR.
Why we’re verified
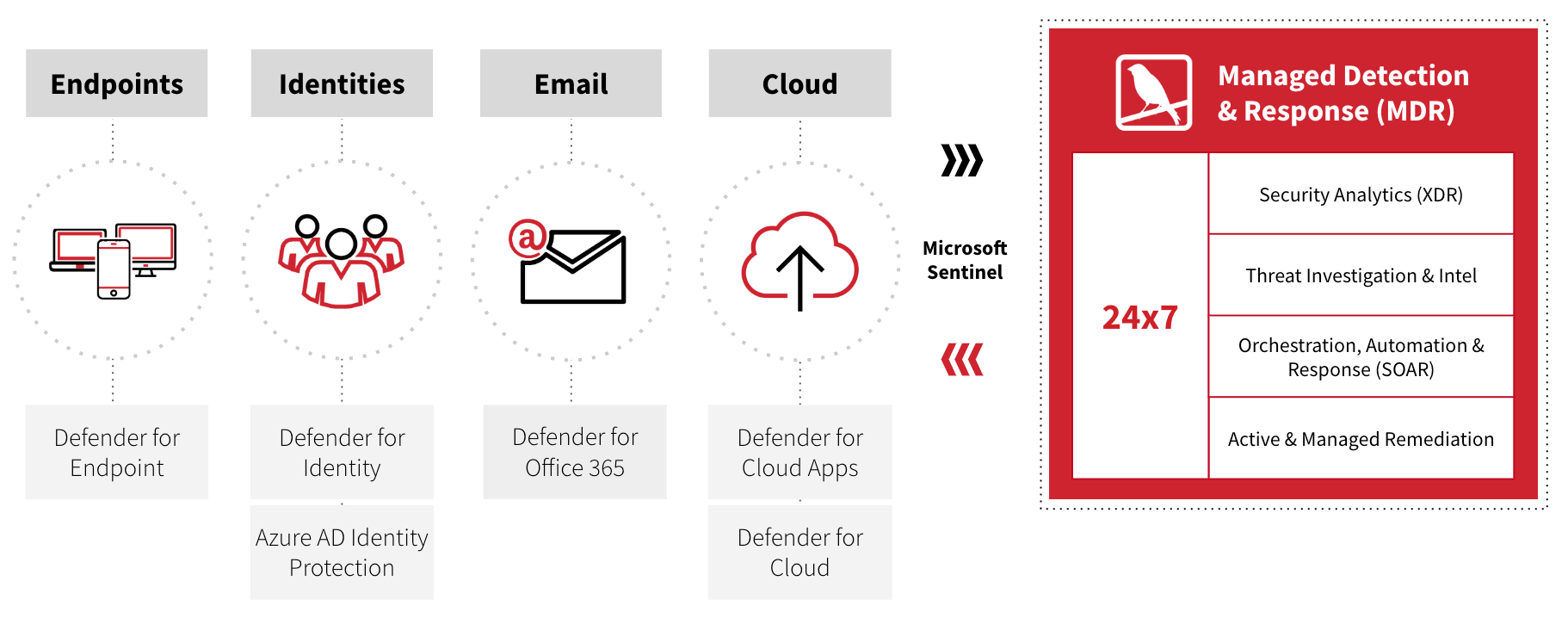
Microsoft verified Red Canary MDR for closely integrating with Microsoft 365 Defender and Microsoft Sentinel. If you’re not yet familiar with either offering, Microsoft 365 Defender is Microsoft’s XDR suite of products that includes Microsoft Defender for Endpoint, Microsoft Defender for Identity, Microsoft Defender for Office 365, and Microsoft Defender for Cloud Apps. Microsoft Sentinel is Microsoft’s information and event management, or SIEM, offering. Together they provide the foundation for integrated threat prevention, detection, and response.
Red Canary MDR ingests telemetry and alerts from Microsoft Security products. We then apply our own threat detection technology, threat intelligence, human detection and response expertise, and more to protect customers 24×7.
To learn more about Red Canary MDR for Microsoft, check out our solution page. To see Red Canary in action sign up for a Microsoft-specific demo.