When suspicious user or endpoint activity crops up, security analysts need to quickly determine if it indicates a genuine threat. This often means wrestling with multiple data sources, requiring tedious manual correlation and extensive pivoting between consoles. More often than not, this effort only confirms that one of your enforcement policies already neutralized the threat.
At Red Canary, we believe your time is too valuable to waste on data gathering and constant pivoting, which is why we’re thrilled to announce our new integration with Zscaler Internet Access™ (ZIA™). This integration pulls critical ZIA context directly into security investigations, empowering our team to notify you of only true positives and your team to take faster, more targeted response actions.
The challenge: assessing suspicious activity quickly without pivoting across consoles
ZIA acts as a primary gatekeeper for network traffic, generating rich web and firewall log data that reveals a lot about what’s happening across your network and user base. This data is invaluable for understanding internet activity and enforcing policies.
At Red Canary, we prioritize protecting your critical assets: endpoints, users, and cloud resources. To do this we monitor EDR, identity provider, and cloud data extensively. Network security data is vital, but traditional sources often lack the context necessary to act—e.g., which endpoint and user are associated with an IP address, what were they attempting to do at the destination—forcing tedious manual correlation.
ZIA is different. Its activity logs are natively enriched with crucial endpoint, user, and application context, making network data truly actionable for asset protection. However, when any of your existing security tools flag something suspicious (like a user clicking a questionable URL), your team still often finds itself:
- Pivoting between consoles: Jumping from your alerting system to your Zscaler environment.
- Hunting for answers: Manually searching ZIA logs for related activity from that specific user or endpoint, trying to piece together what happened before and after the initial alert.
- Wasting time on false positives: ZIA might have already blocked the activity, meaning your investigation into that specific alert could be unnecessary.
This manual correlation consumes valuable time, slows down your response, and can leave significant gaps in your understanding of an incident’s full scope.
Our solution: Red Canary and ZIA, working smarter together
Our new integration with Zscaler Internet Access addresses these challenges head-on. Red Canary taps into the powerful Zscaler Data Fabric for Security to enrich every investigation we conduct with ZIA data where applicable. Because we’re now a part of Zscaler, we can consolidate and query a tremendous amount of investigative context in near-real time, without our team or yours incurring the delay and cost of forwarding that data to a SIEM.
Our approach ensures that our platform integrates the full picture of user and endpoint activity for you before we notify you of a threat. And we provide full transparency into our investigations and ZIA data consulted so that you can take any remaining response actions necessary.
Critically, this integration involves:
- No complex data ingestion: We don’t need to pull massive amounts of ZIA data into our own systems, which saves on storage costs and avoids data duplication.
- No extra licenses: You won’t need to buy additional Zscaler features, like Nanolog Streaming Service (NSS), to get these insights.
- No pivoting to and from the ZIA console: We consolidate all relevant insights in the Red Canary portal for you to review and consult as necessary.
How investigations work with Red Canary and ZIA
When Red Canary detects suspicious activity or begins an investigation, we automatically look up relevant ZIA data from your Zscaler Data Fabric instance. This happens behind the scenes, enriching our investigations without any extra steps from your team.
That enrichment then helps determine whether suspicious activity is benign, malicious and active, or malicious but already mitigated with existing Zscaler controls. You’ll find this valuable context organized within your Red Canary investigation in two key places: related data and related data insights.
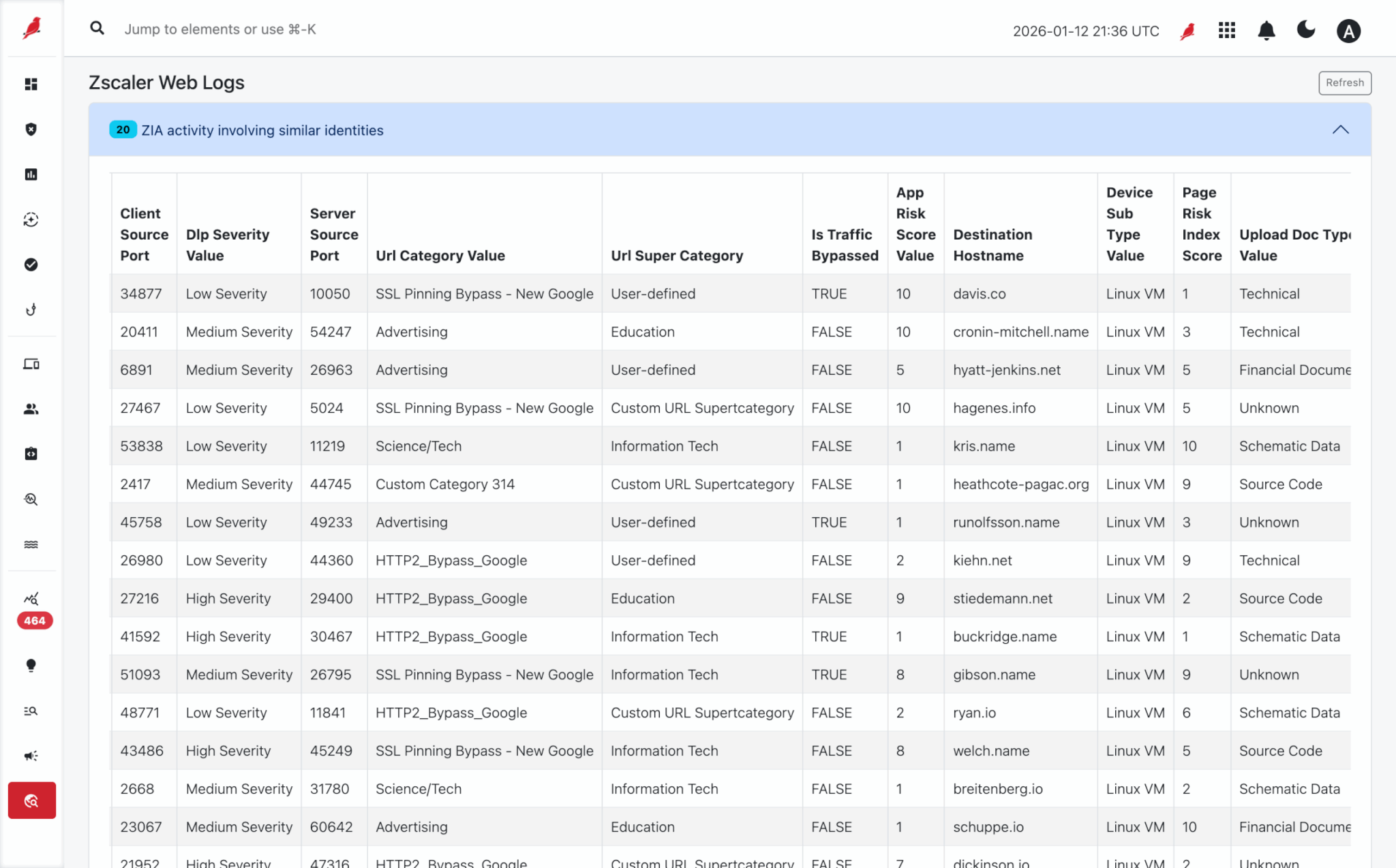
Related data
This is where you can dive into the raw ZIA web log transactions tied to specific leads in our investigation – identities, endpoints, or network activity. It gives you a detailed timeline of internet activity around the suspicious activity of interest.
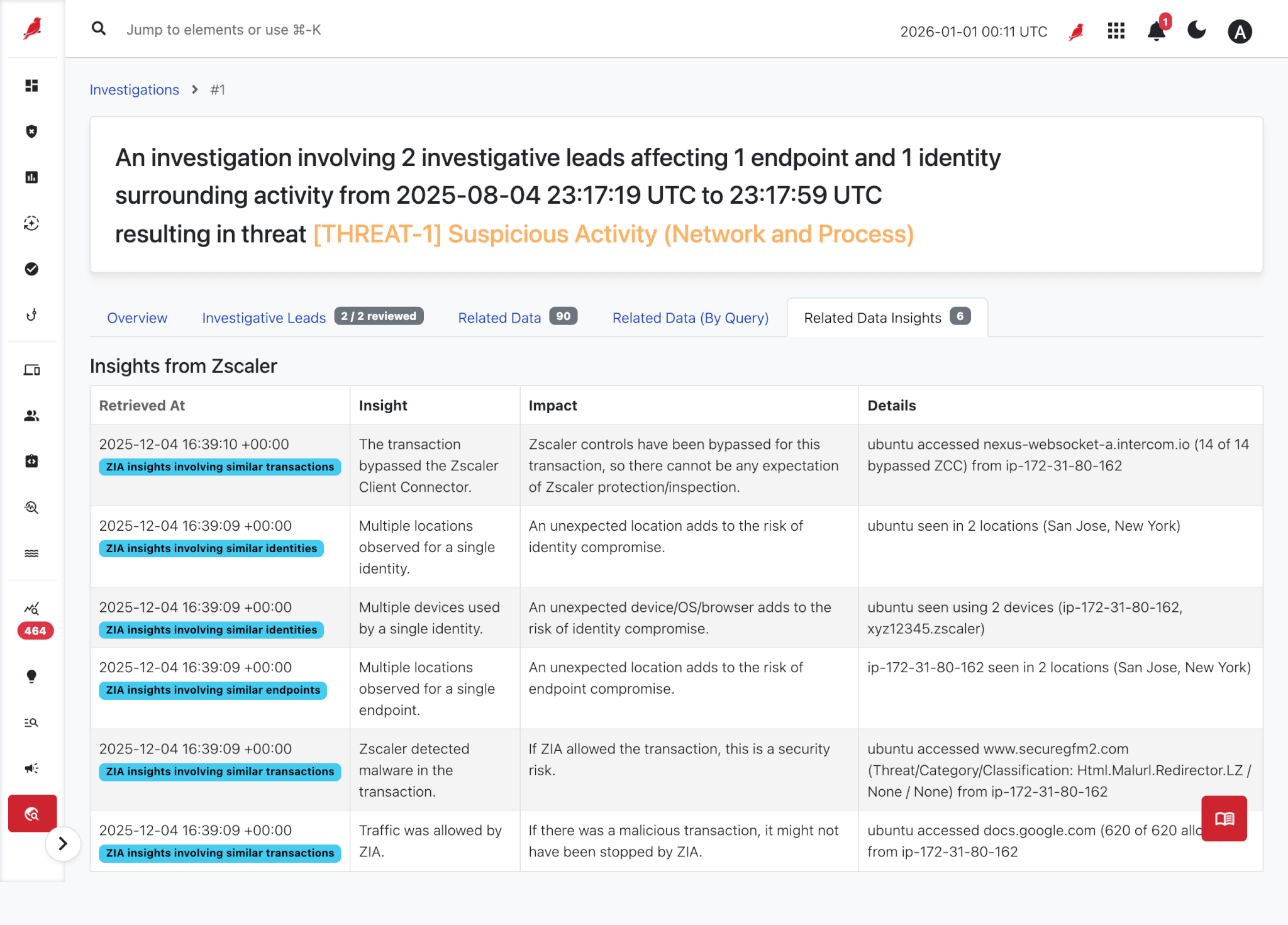
Related data insights
Here, we provide concise, high-level summaries that point out unusual or suspicious activity. Our system runs a series of predefined queries to help answer critical questions, such as:
- User activity: Was the affected user seen on multiple devices, from unexpected locations, or with unusual browser information? Were they observed connecting from a country considered risky?
- Endpoint activity: Was the affected device seen in multiple locations or using unexpected browser details? Is its observed location in a high-risk country?
- Transaction details:
- Did ZIA rate the destination website as high-risk, or categorize it as a non-business function?
- Was traffic to a suspicious destination blocked by ZIA (meaning a potential threat was stopped) or allowed (suggesting a need for further investigation)?
- Was the web traffic encrypted in a way that ZIA couldn’t inspect, potentially hiding malicious activity?
- Did Zscaler detect malware within the transaction?
- Did the transaction bypass the Zscaler Client Connector, which could indicate a gap in your security controls?
- Were there any file downloads related to the incident, especially if they triggered sandbox analysis or were unscannable by ZIA?
- Were there any file uploads related to the incident, especially if they triggered DLP detection rules or were unscannable by ZIA?
Teams gain immediate access to all critical ZIA data directly within Red Canary, eliminating disruptive pivots and dramatically accelerating investigations.
Benefits
This integration offers clear advantages for how you operate and protect your organization:
- Save time: No more manual context gathering across different consoles. Relevant ZIA data appears automatically within Red Canary, letting your team and ours focus on analysis and action, not data collection.
- Reduce noise: By seeing when ZIA has already blocked malicious activity, Red Canary can help you focus on actual threats that require your immediate attention, not activity that’s already been mitigated.
- Accelerate response: Richer context about user, endpoint, and internet activity around suspicious events leads to better decision-making and more precise, comprehensive response.
Get started today
The Red Canary + Zscaler Internet Access integration is generally available now. Get a demo to see how combining Red Canary’s powerful detection and response with Zscaler’s leading network security can transform your security operations.