It was a great year for the Red Canary blog. We added new contributors to our blogging roster and explored a wide and diverse array of topics, ranging from our tactical threat detector series to our more strategic write-ups on career advancement.
Whether you missed out on one of our articles the first time around or you’re coming back for seconds, here are our seven best blogs of 2018 (plus an honorable mention):
7. Building a Mature Threat Hunting Program with MITRE ATT&CK
By Red Canary Staff
In the final part of our Threat Hunting with ATT&CK webinar series, we provided an inside look at how sophisticated security teams build mature threat hunting programs.
However, before we went live, the panelists answered some questions, describing how the incorporation of concepts like automation and rigorous data analysis can help you and your team become threat hunting leaders.
6. Three Areas to Consider When Looking for a Managed Detection and Response Partner
By Michael Haag
Gartner estimates that 15 percent of organizations will be using managed detection and response (MDR) services by 2020, up from less than 5 percent today. For many buyers, past bad experiences can make it difficult to consider outsourcing critical components of your security program. Whether the experience was caused by poor service, an ineffective product, or a vendor who did not innovate post-purchase, it sets the stage for not wanting to consider outsourcing again.
So how do we ensure we select the best vendor? How do we know we’re getting a best-in-class, “11 star” experience compared to a 1 to 5 star experience? When I was a security architect evaluating partners, I often looked at three primary areas of consideration: people, technology, and innovation.
5. Cryptocurrency Trends: Will Ransomware Be Overtaken by Miners?
By Joe Moles
You couldn’t turn on the TV, look at social media, or visit your favorite internet news source in 2017 without being faced with another story of a ransomware compromise. These attacks are highly destructive and largely driven by financial gain. Threat trends and methods to “make a quick buck” will continue, while new methodologies rise to the forefront. Based on recent observations, I believe the new trend to watch for could be cryptocurrency.
I have seen a notable uptick in cryptocurrency miners being delivered via various attack techniques, to various targets. These observations are both directly from attacks my team has observed in the wild, as well as research by other security teams. Even highly public breaches have resulted in the delivery of a miner as the final payload. This trend leads me to believe that the focus of financially motivated adversaries and botnets will move away from ransomware as the primary payload. I am not hypothesizing that ransomware is going away, but that miners will become a more frequently observed payload.
4. Threat Detection #7017: When Web Servers Go Cryptocurrency Mining
By Tony Lambert
Miners and canaries have had a long and storied history, but Red Canaries aren’t too fond of miners. Cryptocurrency miners, that is. Recent booms in cryptocurrency values have made cryptocurrency mining an attractive way for anyone with a computer to earn some extra money. The trouble is, the average user would spend more money performing mining activities and paying for power than they would earn through the mining. It is this dilemma that drives adversaries to take a step ahead.
There have been numerous, well-documented campaigns where adversaries have exploited systems and phished users en masse to install mining tools and generate currency for themselves. Our detection engineers have begun seeing an uptick in cryptocurrency miners, as highlighted in the number five blog on this list. Adversaries usually do not need administrative or root access to a system; they only need the ability to execute code. In this post, we’ll look at one example where the detection of a cryptocurrency miner led to a more insidious discovery.
3. Why a SIEM Won’t Solve All Your Problems: 5 Common SIEM Issues
By Justin Henderson
Today’s organizations suffer from a gap in detection capabilities. Research such as the Mandiant M-Trends report show that the median time to detect an adversary is 99 days. Even if you interpret this with a grain of salt, there’s no doubt that the ability to catch an adversary is far from where it should be. Many organizations look to implement a solution that addresses the gap in detection capabilities and turn to a SIEM. Unfortunately, they often find that it creates more issues than it solves.
As the author of the SANS class SIEM with Tactical Analytics, you might assume I’m a SIEM hugging advocate (and I am). I believe that a SIEM is one of the most capable detection solutions available. However, “most capable” does not necessarily mean “best.” While I would love to say a SIEM is the answer to all things, that is simply not the case. Let me clarify this seemingly contradictory position…
2. Threat Hunting for PsExec, Open-Source Clones, and Other Lateral Movement Tools
By Tony Lambert
Adversaries in post-compromise security incidents are like shoppers in a grocery store. It’s rare that they head straight to a single place to get what they need. Instead, they enter the building and move around the aisles, gathering pieces along the way before they check out. In the same way, adversaries won’t hit a single place on your network that contains all the data they’re trying to steal. They have to move laterally from system to system (or aisle to aisle) to gather the information that they came for.
To move around freely without attracting too much attention, attackers often use reliable software that looks normal in an enterprise environment. One of the favorites among adversaries is an old friend of many IT administrators: SysInternals PsExec.
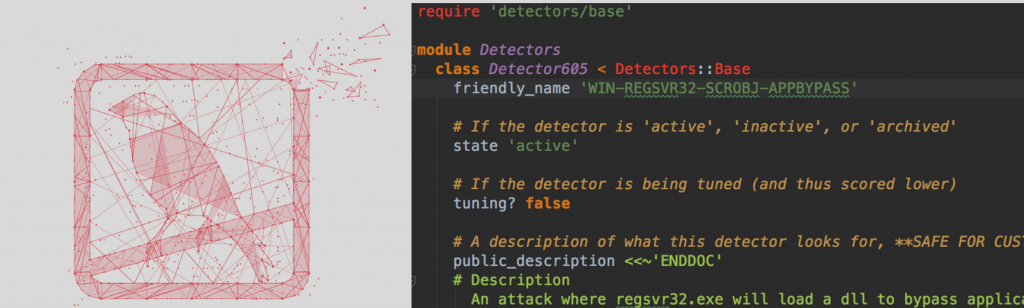
1. Behind the Scenes with Red Canary’s Detection Engineering Team
By Kyle Rainey
At Red Canary, we are huge believers in sharing methodologies of how and why we do things. It provides opportunities for others to learn and pushes the community forward. In this article, we pulled back the curtains on Red Canary’s detection engineering team.
Our team’s mission is simple: hunt and find threats. Rather than analyzing and triaging alerts like a traditional Security Operations Center (SOC), we apply engineering concepts to develop detectors, tools, and systems that enable us to quickly and efficiently identify threats in massive amounts of data.
Honorable Mention: Lateral Movement Using WinRM and WMI
By Tony Lambert
Published in 2017, this one was technically disqualified from consideration among our best blogs of 2018. Despite this, it was still Red Canary’s most popular blog of 2018.
Many organizations invest millions of dollars to bolster their systems and prevent attackers from gaining entry. Much less attention is given to the concept of lateral movement within an organization. Yet we’ve seen time and time again that once an adversary breaks through the crunchy outer layer of the network, the gooey center quickly becomes trivial to move about.
Stopping lateral movement is just as important as preventing a breach. Attackers frequently move laterally with tools included in Windows, and this tactic has also been observed within commodity malware samples. This article will outline a threat detection in which Windows Remote Management (WinRM) spawned a process via Windows Management Instrumentation (WMI).
Conclusion
So there it is… Red Canary’s seven most popular blog posts of 2018, with an additional hat-tip to a piece from late 2017 that performed well throughout the year. Moving into the coming year, we already have a long list of topics we’re hoping to address, starting with a dive into the Red Canary CIRT, some philosophical musings on the importance of suppression, a look at how security teams can detect bad things with limited data, and much, much more.
We hope you enjoy the holidays, and we look forward to having you all back in 2019!