In Netfilx’s KPop Demon Hunters, the protagonists don’t just fight adversaries, they go into full takedown mode: unleashing synchronized precision strikes that wipe out threats in style. It’s flashy, high-energy, choreography-perfect… and honestly? It feels a lot like the last year in cybersecurity.
2025 brought some remixes to the threat landscape, with global law enforcement and private-sector teams moving in seemingly perfect formation to dismantle some of the most disruptive “as-a-service” ecosystems on the planet. Think of it as a cyber-defense dance routine—equal parts coordination, power, and rhythm—aimed at stopping the threat actors haunting the networks of global businesses.
So, let’s drop the beat and break down some of the top operations that defined this year’s cyber-takedown era.
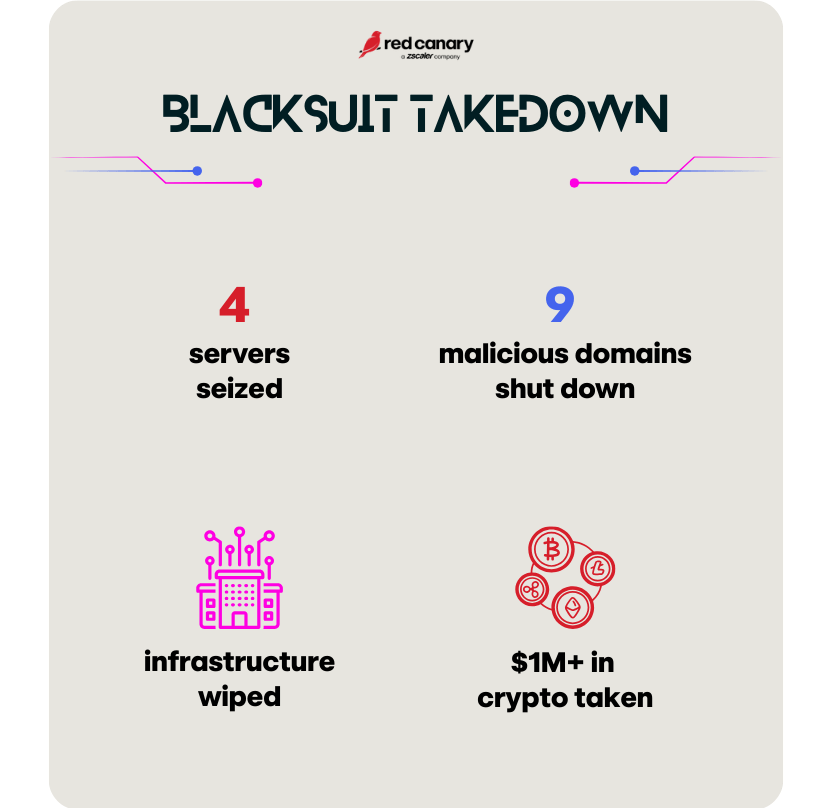
BlackSuit: The headliner finally gets knocked off the stage
If BlackSuit were a villain in Netflix’s hit movie, it’d be the masked final-boss idol: confident, relentless, and way too comfortable controlling the spotlight.
But then came the takedown. In July, U.S. and international agencies hit BlackSuit with a coordinated strike that could’ve been lifted from a music-video high point.
BlackSuit wasn’t just a ransomware crew, it was a touring production hitting healthcare, education, public services, and global commercial sectors. This takedown didn’t just silence a song. It kicked the mic stand out from under an entire criminal ecosystem. The move was surgical, stylish, and absolutely worthy of a KPop fight scene slow-motion replay.
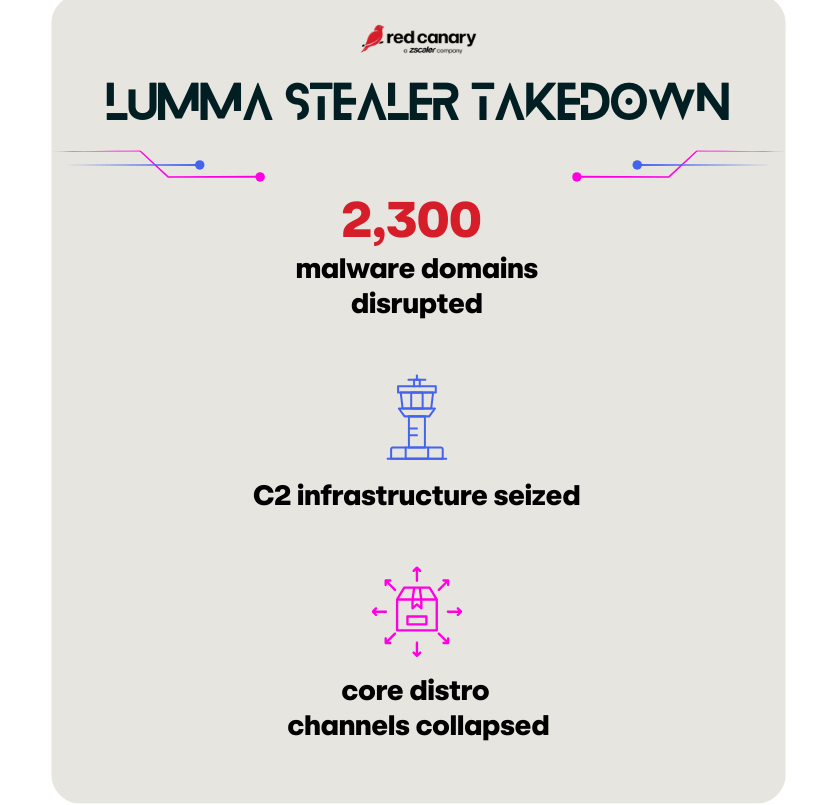
Lumma Stealer: The backstage villain whose toolkit powered the bad guys
Every demon-hunting saga has that sneaky antagonist in the background, the one whispering power to others and empowering the real chaos.
In 2025, that was Lumma Stealer, a malware-as-a-service platform that helped attackers steal:
- credentials
- payment data
- crypto wallets
- cloud access
- sensitive business information
Basically, the keys to the kingdom.
So when a global coalition led by Microsoft and backed by the FBI, Europol, and a whole squadron of security vendors mobilized, the takedown felt like a zero-gravity dance break from the animated action movie.
This didn’t just stop one gang. It pulled the plug on dozens of downstream adversaries who depended on Lumma to power their attacks, similar to cutting electricity to the entire demon underworld. If the movie had a montage of gadgets exploding in bright neon shards… that would be Lumma Stealer’s takedown.
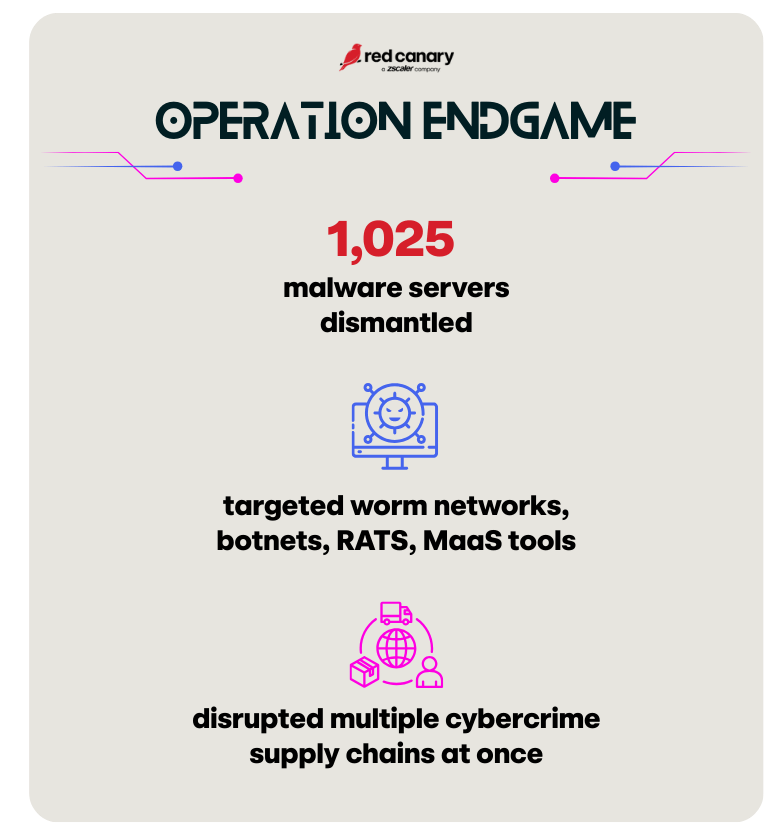
Operation Endgame: The ensemble finale that shook the entire cyber underworld
When the final act hits in the epic KPop battle story, it’s never about one hero. It’s all of them, moving as a single force, unleashing that signature synchronized knockout combo.
Operation Endgame was exactly that.
Across the U.S., Europe, and international partners, law enforcement took care of business.
This was less “take down a group” and more “wipe the stage clean.” Endgame’s brilliance wasn’t in hitting one “monster, ” it was in cutting off the ecosystem that feeds them.
Think of it like the moment all HUNTR/X members lock into formation, lights blast upward, and the villains evaporate in rippling shockwaves: that level of coordinated impact.
Why these takedowns hit like a KPop chorus drop
All three operations had something in common. They weren’t just about catching cybercriminals, they were about:
- Disrupting the infrastructure powering global cybercrime
- Eliminating the supply chains behind RaaS and MaaS
- Rewriting the cyber threat landscape (at least temporarily)
Together, they formed a global crew of defenders, finally moving in sync.
Why vigilance is the real headliner
Takedowns are powerful and necessary. They shift the landscape, weaken threat groups, and buy critical breathing room. But similar to a neon-lit demon battle, security practitioners don’t power down after a few wins.
Remember to:
- Keep tightened identity controls
- Double down on cloud visibility
- Strengthen incident response & readiness
- Monitor for rebrands, resurrections, and copycats
- Track ecosystem shifts after major disruptions
So defenders, turn up the lights. Check your gear. Sync with your crew. Because takedowns aren’t the end, they’re just part of the process. You’ll want to be ready in the event of a comeback tour.