Our AI agents are transforming SecOps
Benefit from agentic AI in your security program today
99% noise reduction
3 min AI agent investigations
↓60% triage + notification time
Meet Red Canary's AI Agents
Threat hunting recommendations
Generates threat hunting recommendations based on analyzed security incidents.
Potential threat escalation analysis
Analyzes threat data to determine how highly to prioritize the alert.
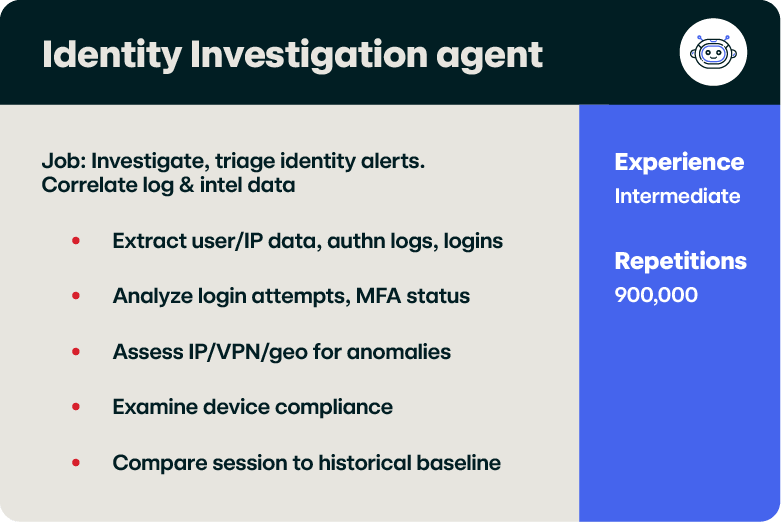
Identity - CrowdStrike Falcon Identity
Investigate and triage identity-based security alerts from the Falcon Identity Protection platform.
Identity - Microsoft Entra Identity Protection
Investigate and triage alerts from Microsoft Entra Identity Protection.
Identity - Microsoft Cloud App Security
Investigate and triage identity security alerts from Microsoft Cloud App Security.
Identity - Okta Workforce Identity
Investigate and triage security alerts from Okta Workforce Identity.
Identity - Cisco Duo
Investigate and triage security alerts from Cisco Duo Trust Monitor.
Identity - Red Canary Identity Engine
Investigate and triage identity events from Red Canary’s detection engine.
Cloud - AWS GuardDuty
Investigate and triage security alerts from AWS GuardDuty.
Endpoint - Microsoft Defender for Endpoint
Investigate and triage security alerts from Microsoft Defender for Endpoint.
Endpoint - CrowdStrike Falcon Endpoint Security
Investigates and triages CrowdStrike Falcon endpoint alerts.
Endpoint - SentinelOne
Investigate and triage security alerts from SentinelOne Singularity Platform.
Endpoint - Palo Alto Cortex XDR
Investigate and triage security alerts from Cortex XDR.
Endpoint - Red Canary Endpoint Engine
Investigate and triage EDR events from Red Canary’s detection engine.
SIEM - Microsoft Sentinel
Investigate and triage security alerts from Microsoft Sentinel.
Endpoint & identity - Wiz
Investigates and triages Wiz security alerts across both endpoint (WIZ_SENSOR) and identity-based threat detections.
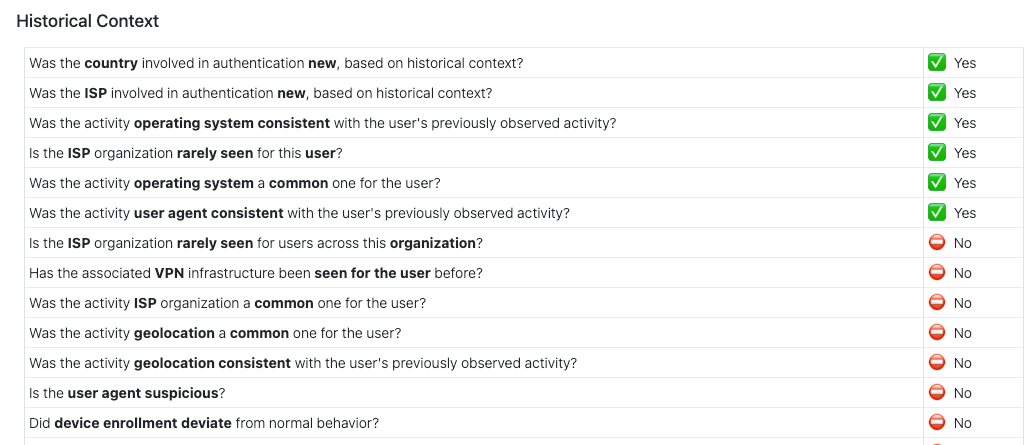
User baselining & analysis
Analyze login patterns over a 30-day period, identify anomalies, and generate concise reports.
Threat review & agentic tuning
Consults your organizational preferences and security context to recommend whether an alert should be suppressed.
Email analysis
Analyzes emails and attachments to generate comprehensive reports and analysis.
Phish identification
Identify phishing emails and provide comprehensive reports.
Event & threat analysis
Provide summaries, recommendations, and narratives about a threat to aid understanding and response.
Threat response recommendations
Provides prioritized remediation guidance for containment, eradication, and hardening directly in the threat timeline.
Alert analysis
Analyzes security alerts, enriches them with context, and routes them to specialized platform-specific agents.
Notes & annotations
Add context to threat timelines related to user activity vs typical baseline behavior.
Intelligence insights
Provide detailed threat intelligence context for ongoing security investigations, including profiles.
Platform & tool assistance
Provide knowledge to SOC personnel regarding Red Canary products and copilot features.
Alert summary
Analyzes security alerts from various platforms and generates structured summaries and recommendations.
Customization review
Reviews user-provided tuning instructions and provides feedback on whether they need changes before being implemented.
Suppression explanation
Generates a concise explanation comment for why a security alert was considered non-malicious.
Hardening recommendations
Generates system hardening recommendations based on threat indicators.
Threat summary generation
Generates concise 1-3 sentence threat summaries from cybersecurity incident data.
Reporting coordination
Coordinates sub-agents to produce comprehensive threat reporting.
Supported Integrations
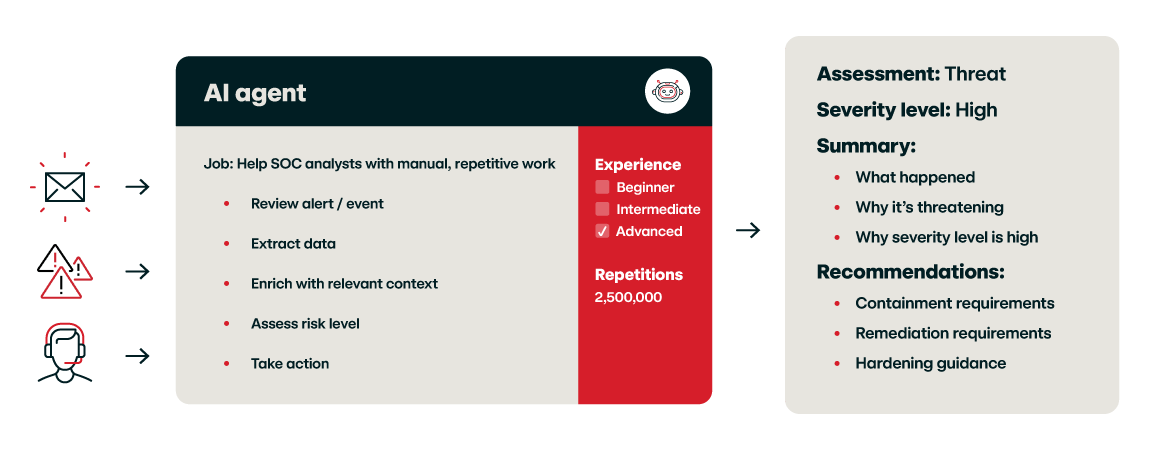
How our agents work
Red Canary AI agents dynamically interact with data and systems to execute a specific job based on real-time inputs and context.
Powered by AI models like LLM, these agents adapt their behavior based on tasking – a massive upgrade from rigid automated workflows.
Our Approach
Red Canary’s AI agents and experts deliver SecOps excellence at machine speed
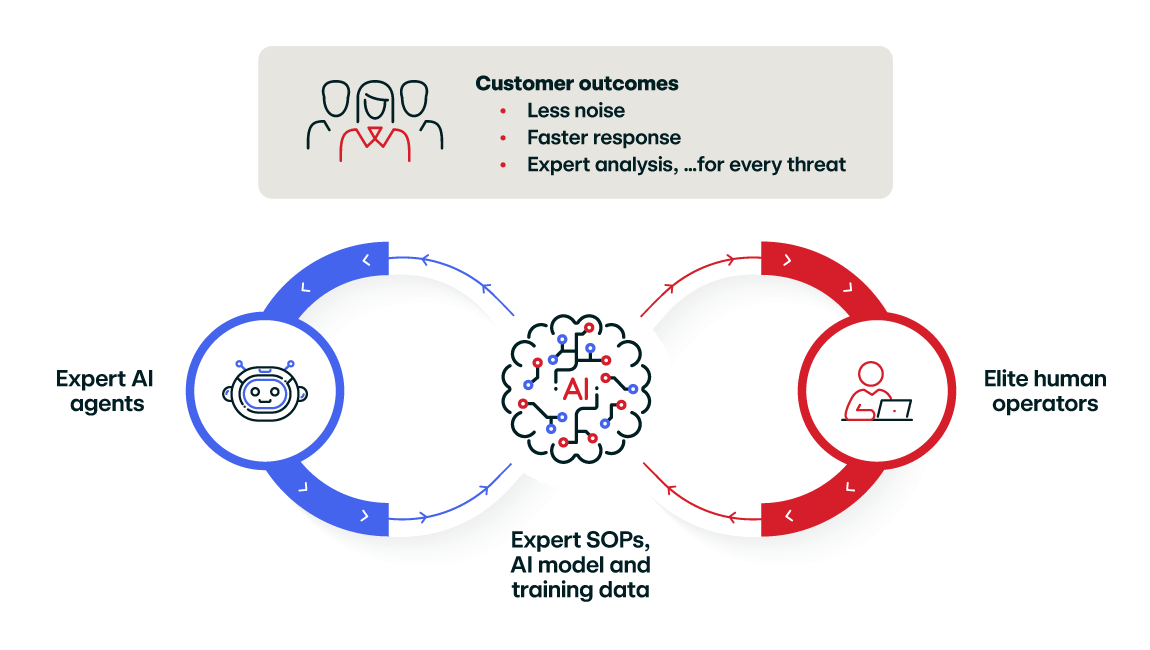
Red Canary AI agents are different:
Most AI agents chase breadth at the expense of reliability. Red Canary’s AI agents are specialized, focusing on a narrow set of tasks that they perform flawlessly.
- Imbued with a decade+ of real-world security operations experience
- Guided by narrowly-scoped, expert-crafted standard operating procedures
- Managed and tuned by elite human operators
- Continuously optimized with feedback and new intelligence
Agentic Tuning
Filter out highly specific and difficult-to-tune alerts with a few plain-language sentences.
Learn More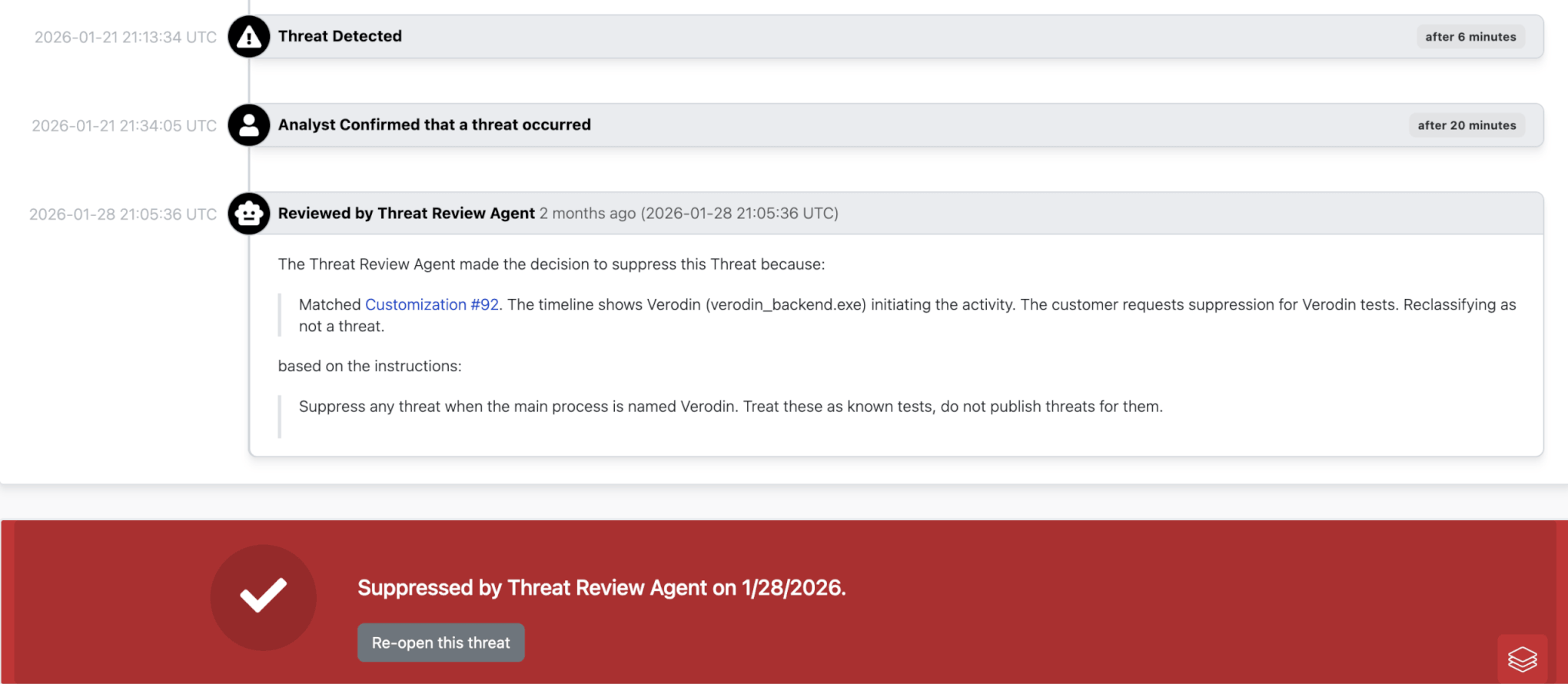
Agent visibility
See exactly what your AI agents are doing and why.
Coming Soon
FAQs
How can I access these AI agents?
Red Canary MDR customers already have expert AI agents working on their behalf. We are actively exploring pricing and packaging models, alongside MCP server options, for future customers looking to access these AI agents directly.
What data was used to train these AI agents?
Our AI agents are trained on 11+ years and counting of high-fidelity threat detection, investigation, and incident response data and industry-leading security operations workflows. The richness and reliability of the training data is what contributes to a 99.7% threat accuracy rating and rapid responses times when they collaborate with our human experts.
How do you ensure the privacy of my data?
Data utilized by our AI agents never leaves Red Canary controlled infrastructure for processing, storage, training or any other reason. Your data is (1) not available to other customers, (2) not available to third parties, (3) not used to train external AI models, and (4) not used to improve any third-party products or services. The underlying AI models do not interact with other external services, such as ChatGPT.
How does Red Canary get feedback on AI agent performance?
We solicit customer feedback–’thumbs up, thumbs down’ on outputs–in our product and manually review all off-target feedback. We also continuously measure the impact of AI agents on our accuracy, completeness, and timeliness of threat notifications. We only use AI agents to the extent that they benefit our overall performance for our customers.
How do you ensure the outputs of your AI agents can be trusted?
We validate trustworthiness of AI agent performance via extensive functional testing in which all outputs that vary beyond 10% of our ideal output are manually inspected. And as mentioned in the prior question, we continuously measure the impact of AI agents on our accuracy, completeness, and timeliness of threat notifications. We only use AI agents to the extent that they benefit our overall performance for our customers.