The MDR customers swear by
Proven protection that never clocks out
Superior security results, 24/7 expert support, and freedom to focus. That's the Red Canary difference.

First things first
Here are the most common questions about what Red Canary does and how it works.
Is Red Canary solely endpoint focused?
No, Red Canary is not solely endpoint-focused.
We provide managed detection and response across all layers of your environment, including endpoints, identities, cloud, and beyond.
Does Red Canary replace my SOC?
No, Red Canary doesn’t replace your existing SOC.
Red Canary provides managed detection and response (MDR) services, which complement and enhance your existing SOC. Think of us as your trusted partner, offering the expertise, tools, and support needed to strengthen your overall security posture without replacing your SOC.
How is Red Canary different from an MSSP?
A managed security service provider (MSSP) provides outsourced cybersecurity monitoring, typically focusing on basic security tasks like perimeter traffic monitoring and vulnerability management. They often rely on signatures and rule-based detection, which can miss advanced threats. When incidents occur, customers are often left to manage containment themselves or pay extra for response services.
Red Canary is different. As an MDR provider, we act as a true extension of your security team, providing the expertise and technology to proactively hunt for and respond to advanced threats. We delve deeper into your security data, using a combination of cutting-edge technology and expert analysis to identify and neutralize threats before they can cause significant damage. This proactive approach, coupled with a focus on rapid response and collaboration, empowers your team to focus on strategic initiatives while ensuring comprehensive threat detection and response.
Explore a detailed comparison of MSSPs and MDR services in our MSSP vs. MDR Guide.
How does Red Canary MDR differ from the MDR offered by EDR/XDR vendors?
While many EDR and XDR vendors now offer MDR as an add-on, their approach often focuses on leveraging their own technology, which can create a siloed security view and lead to vendor lock-in. These vendor-native MDR solutions can also limit the ability to detect threats across the full attack surface, hindering proactive threat hunting, incident response, and remediation. This product-centric approach may leave your team with an incomplete security picture, unable to trace threats across multiple systems or effectively reduce overall risk exposure. Moreover, as the competitive landscape evolves, organizations may find themselves locked into outdated solutions with few options for migration or service continuity.
In contrast, Red Canary is vendor-agnostic, integrating with a wide range of security tools to provide enhanced threat detection, reduce alert fatigue, and improve your overall incident response capabilities. Our expert analysis, threat hunting, and hands-on response go beyond automation to ensure real threats are identified and stopped—no matter which tools you use. This flexibility guarantees you always have access to the best security solutions available.
How is Red Canary different from a SIEM, and does Red Canary need a SIEM to work?
While SIEMs are often central to security and compliance strategies, serving as a repository for data from various tools, they require significant effort to configure, analyze, and respond to threats—and can be cost-prohibitive. As an MDR provider, Red Canary goes beyond aggregation by continuously monitoring and investigating threats in real time, delivering high-fidelity detections, and providing expert-driven response. Instead of drowning in alerts, your team gets actionable intelligence and 24/7 support to stop threats faster.
Red Canary does not require a SIEM to work. Red Canary integrates seamlessly with various security tools, including SIEMs, but operates independently by collecting and analyzing telemetry directly from your endpoints, cloud environments, identity providers, and other integrated systems. For organizations struggling with SIEM complexity and budget constraints, the Red Canary Security Data Lake provides a flexible, cost-efficient solution for long-term security data storage and querying.
Are Red Canary and Atomic Red Team™ the same thing?
Red Canary and Atomic Red Team are not the same thing.
Red Canary is an MDR provider that offers comprehensive threat detection and response services across endpoints, networks, identities, and cloud environments. We leverage threat intelligence, behavioral analytics, and expert investigation to detect and respond to potential threats in real-time.
Atomic Red Team, on the other hand, is an open-source project developed by Red Canary that provides a collection of tests to simulate common attack techniques used by adversaries. These tests help organizations assess and improve their security posture, specifically in the area of detection capabilities. While Red Canary developed Atomic Red Team, we are distinct in terms of services: Atomic Red Team is a testing tool, while Red Canary is a security service provider.
Does Red Canary offer canary tokens, pen testing, or red teaming services?
Red Canary does not offer canary tokens, pen testing, or red teaming services.
However, we provide Red Canary Readiness Exercises, realistic scenarios and expert-led tabletops designed to help organizations assess their security posture and improve response capabilities, helping ensure they are fully prepared for real-world threats.
What tools does Red Canary integrate with?
Red Canary integrates with a wide range of security tools to provide comprehensive detection and response across your environment. Find our full list of integrations here.
Why Teams Choose Red Canary
Detections You Can Trust
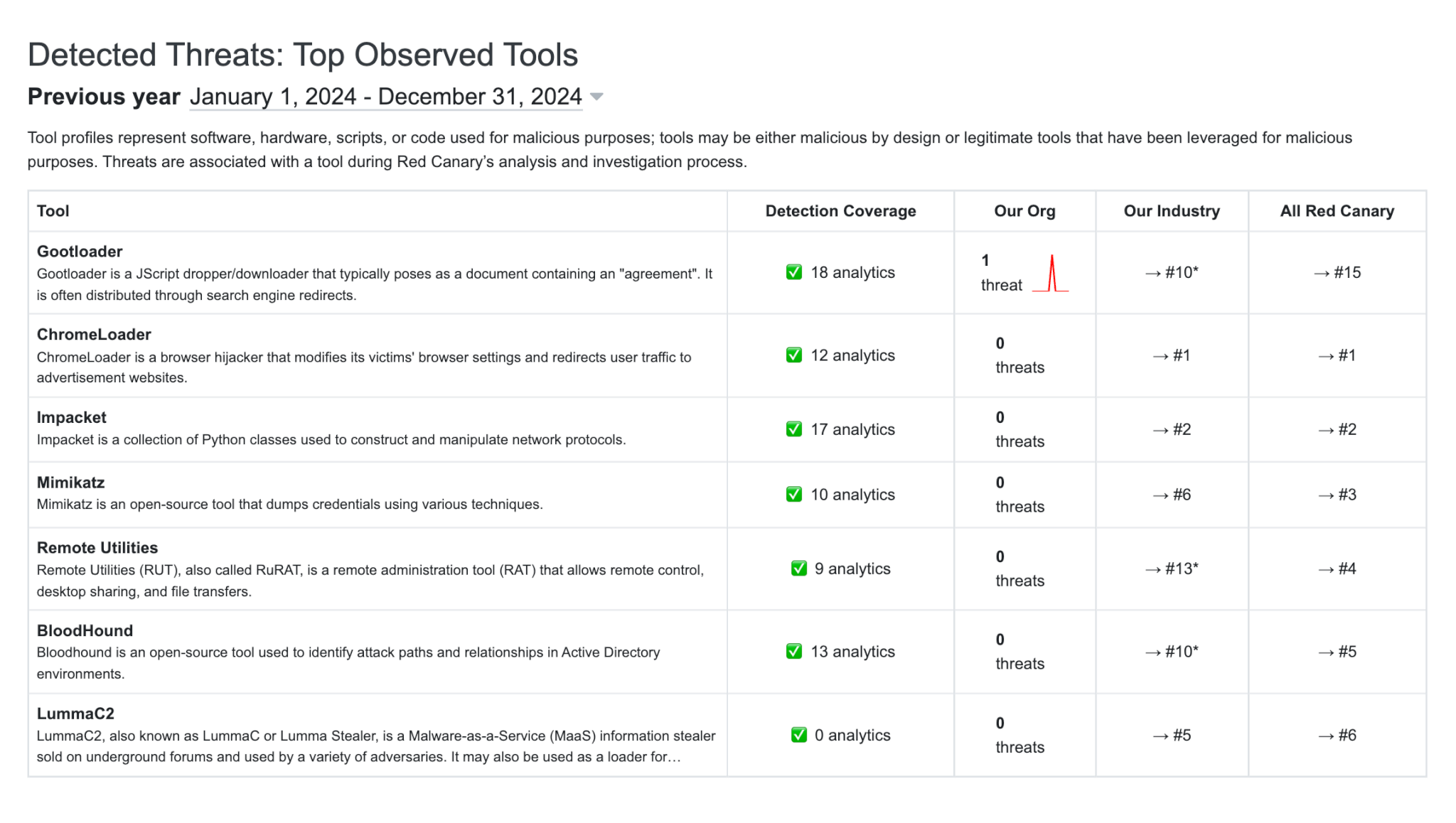
Stop chasing false positives and missing threats. Traditional security approaches that rely solely on alert triage waste precious time and leave gaps. That’s why we pioneered detection-as-code detection engineering to deliver trustworthy insights, helping you detect threats faster, minimize noise, and respond with confidence.
- Proactive defense. With thousands of behavioral analytics and counting, we catch threats others miss—enabling you to address risks before they escalate.
- Faster, more precise detection. Our detection-as-code philosophy delivers scalable, high-fidelity threat detection, with a 99.6% true positive rate, reducing manual effort and improving response times.
- Embedded expertise. Gain access to our detection engineering processes, expert insights, and real-time feedback loops to refine your own security operations.
Insights you can act on—fast
Security isn’t one-size-fits-all. Red Canary’s intelligence team provides granular, tactical insights tailored to your unique environment, helping you understand adversaries, their tactics, and how to stop them.
Insights you can act on—fast
Security isn’t one-size-fits-all. Red Canary’s intelligence team provides granular, tactical insights tailored to your unique environment, helping you understand adversaries, their tactics, and how to stop them.
- Actionable insights. We translate alerts and telemetry into clear, practical insights that empower you to take swift, effective action and stay ahead of emerging threats that matter most to your business.
- Always-on threat hunting. Get expert guidance or hands-on support during incidents—at no extra cost.
Expert response you can count on
You deserve more than solely automated responses and surface-level support. Red Canary’s expert support team helps you reduce mean time to respond (MTTR) by detecting threats early, investigating with precision, and enabling rapid expert-led and automated containment.
Expert response you can count on
You deserve more than solely automated responses and surface-level support. Red Canary helps you reduce mean time to respond (MTTR) by detecting threats early, investigating with precision, and enabling rapid expert-led and automated containment.
- Faster response, faster resolution. We detect threats early and initiate remediation within minutes—our response engineers’ median time to acknowledge high-severity threats is just 2 minutes.
- Automation + expertise. Contain threats quickly with customizable response playbooks, and get 24/7 access to expert guidance for remediation, hunting, and mitigation.
- Comprehensive reports. Every detection includes a detailed summary of findings, actions taken, and next steps to strengthen your defenses.
All your data, all the protection
Take a smarter approach to security. Red Canary continuously analyzes the telemetry and alert sources that fuel threat detection. Lower-fidelity data can be cost-effectively stored in our Security Data Lake for investigation and compliance. This approach enables you to:
All your data, all the protection
Take a smarter approach to security. Red Canary continuously analyzes the telemetry and alert sources that fuel threat detection. Lower-fidelity data can be cost-effectively stored in our Security Data Lake for investigation and compliance. This approach enables you to:
- Detect and stop more threats, faster
- Get more value from your existing security stack
- Ensure compliance without the complexity
- Avoid unnecessary expenses by storing low-fidelity security data in our cost-efficient Security Data Lake

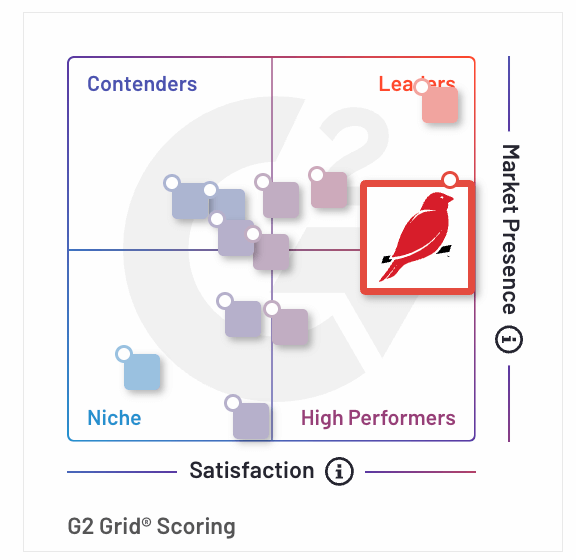
An MDR leader. Again and again.
Forrester Wave™: Managed Detection And Response, Q1 2025
Named a leader in MDR and given the highest possible scores in 10 criteria
G2 Summer 2025 Grid® Report for Managed Detection and Response (MDR)
Ranked #1 in customer satisfaction for enterprise MDR providers
Incident Response & Readiness Guide
Equip your team with the latest incident response strategies
1,000+ security teams can’t be wrong
With over a decade of experience and a 99% customer satisfaction score, Red Canary delivers exceptional security and support that thousands of organizations have relied on.

“Red Canary caught something that we would have otherwise missed. There’s a capability gap in current security solutions, and only one of our tools is capable of filling that gap. Red Canary is the only one I know of that could have detected the suspicious activity we saw.”
CIRT TEAM MEMBER,DUPONT Learn More
“Red Canary acts as a filter for us: they bubble up the most pressing things to the top, and it’s very easy to collaborate with them within their portal. We get the most pressing alerts passed to our response team, and they get actioned first.”
DAVE COUGHANOUR, CISO, ANSYS Learn More
“With the steps Red Canary took after detection, we felt safe almost immediately. We were back to normal that morning. They were following up with us all day and even proposed follow-up items to make us safer going forward. It was an awesome experience.
MIKE MARSTRELL, INFRASTRUCTURE MANAGER, SCHUMACHER HOMES Learn More

“The level of analysis and the quality of information we receive when a threat is detected empower us to respond effectively. I no longer wonder if there’s more to the story, because Red Canary provides the complete narrative.”