Add an ally. Strengthen your defenses.
You don’t need time, expertise, or an army of security hires to build a 24/7 detection and response capability—you simply need Red Canary.
As CrowdStrike specialists, we ensure you get immediate return on your product investments, along with the added peace of mind of knowing an industry-respected detection and response team is watching your environment at all times.
10x
your detection coverage
24/7
detection and response
1/1000
fewer false positives
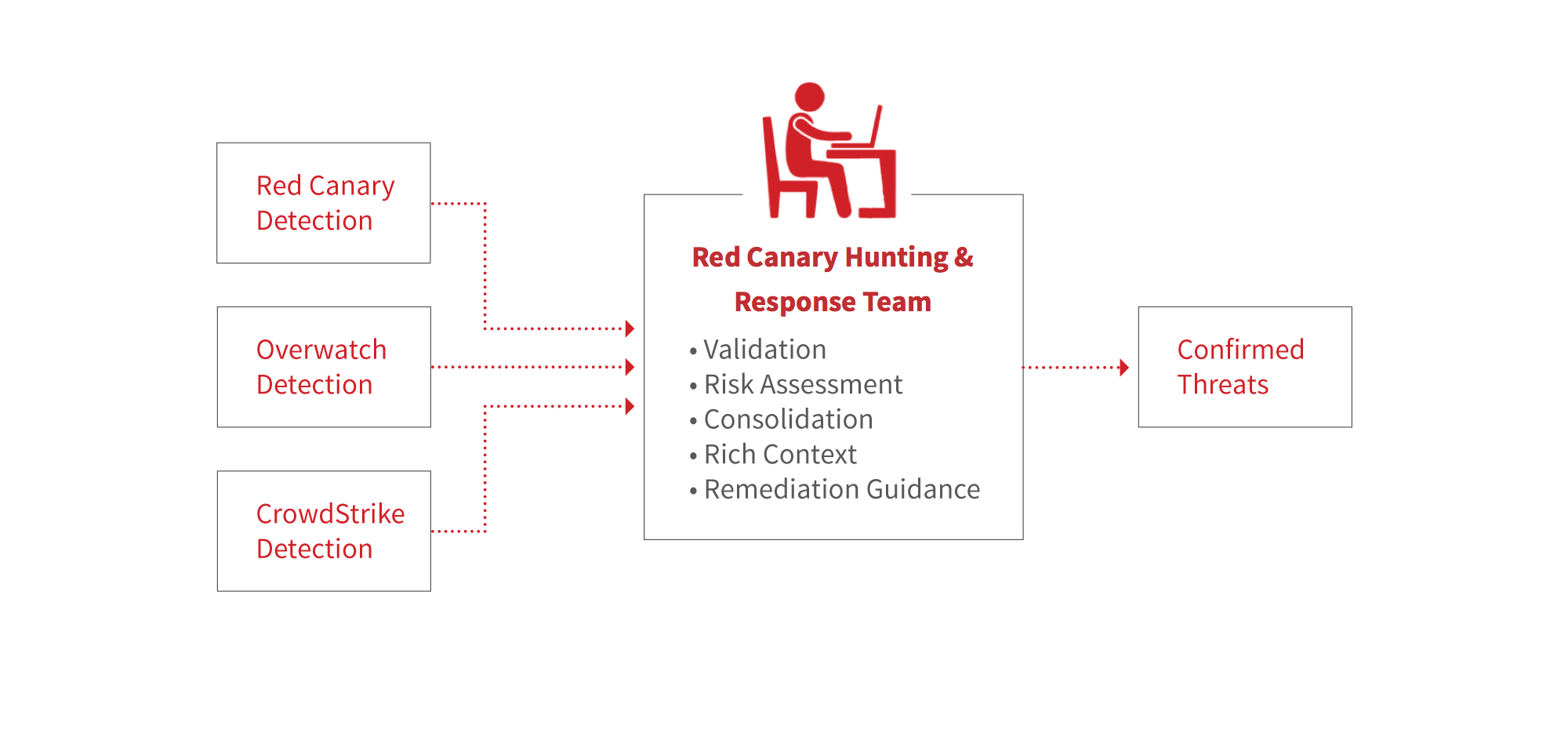
How it works
The integration is simple:
- Falcon ships all of the endpoint telemetry it collects to Red Canary.
- Red Canary standardizes the telemetry into its internal format.
- The Red Canary Engine analyzes the data and surfaces potential threats.
- Red Canary analysts investigate and confirm threats and publish full-context detections to customers.
Red Canary also connects to the Falcon Streaming API to get a feed of threats surfaced by CrowdStrike’s detection capabilities, including Overwatch. Red Canary’s analysts confirm and consolidate these threats as well.
Customers seeking preventative technology can choose to take advantage of CrowdStrike’s endpoint protection offering while Red Canary works behind the scenes to hunt for and investigate advanced attacker behaviors, techniques, and tools.
FEATURES
Turnkey detection and response
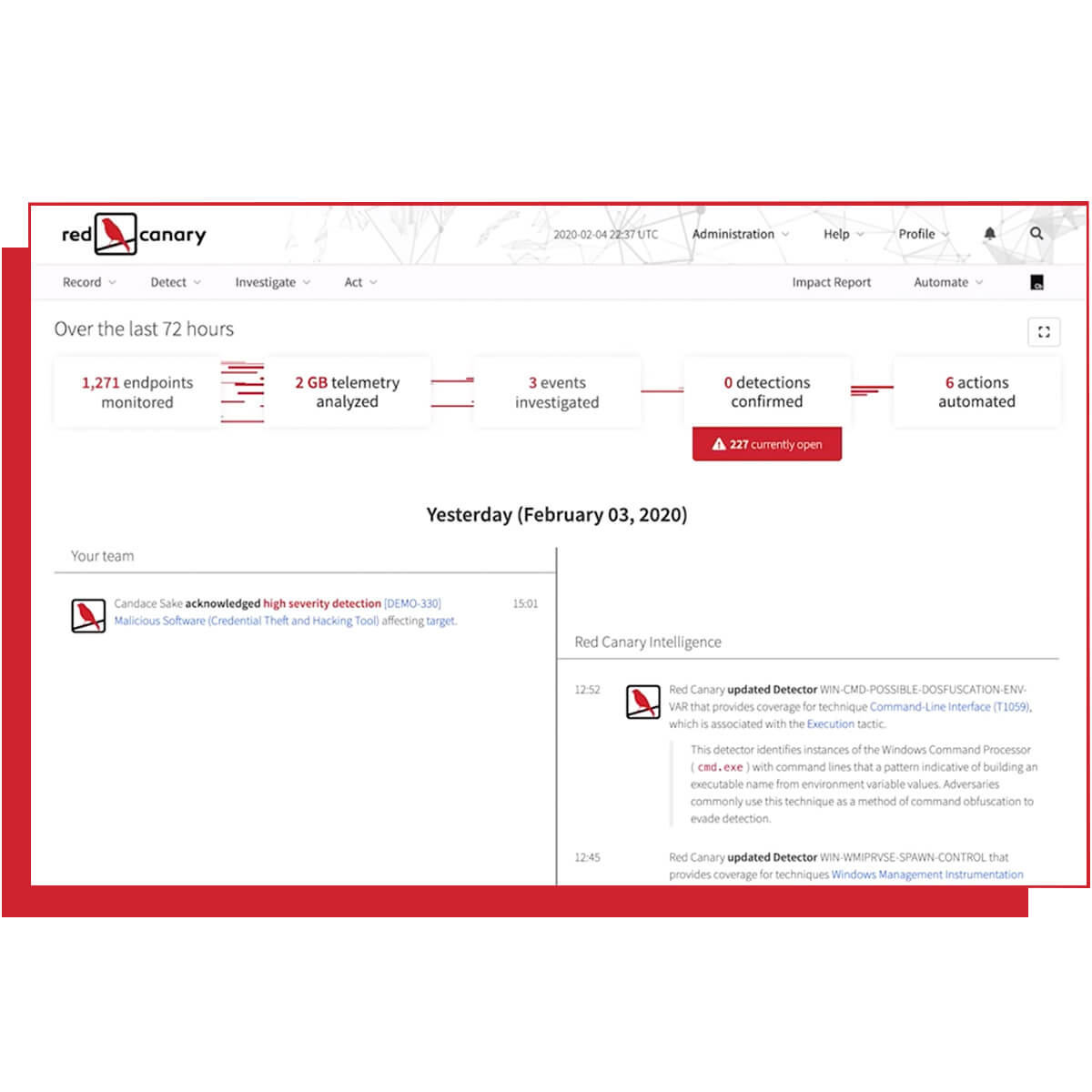
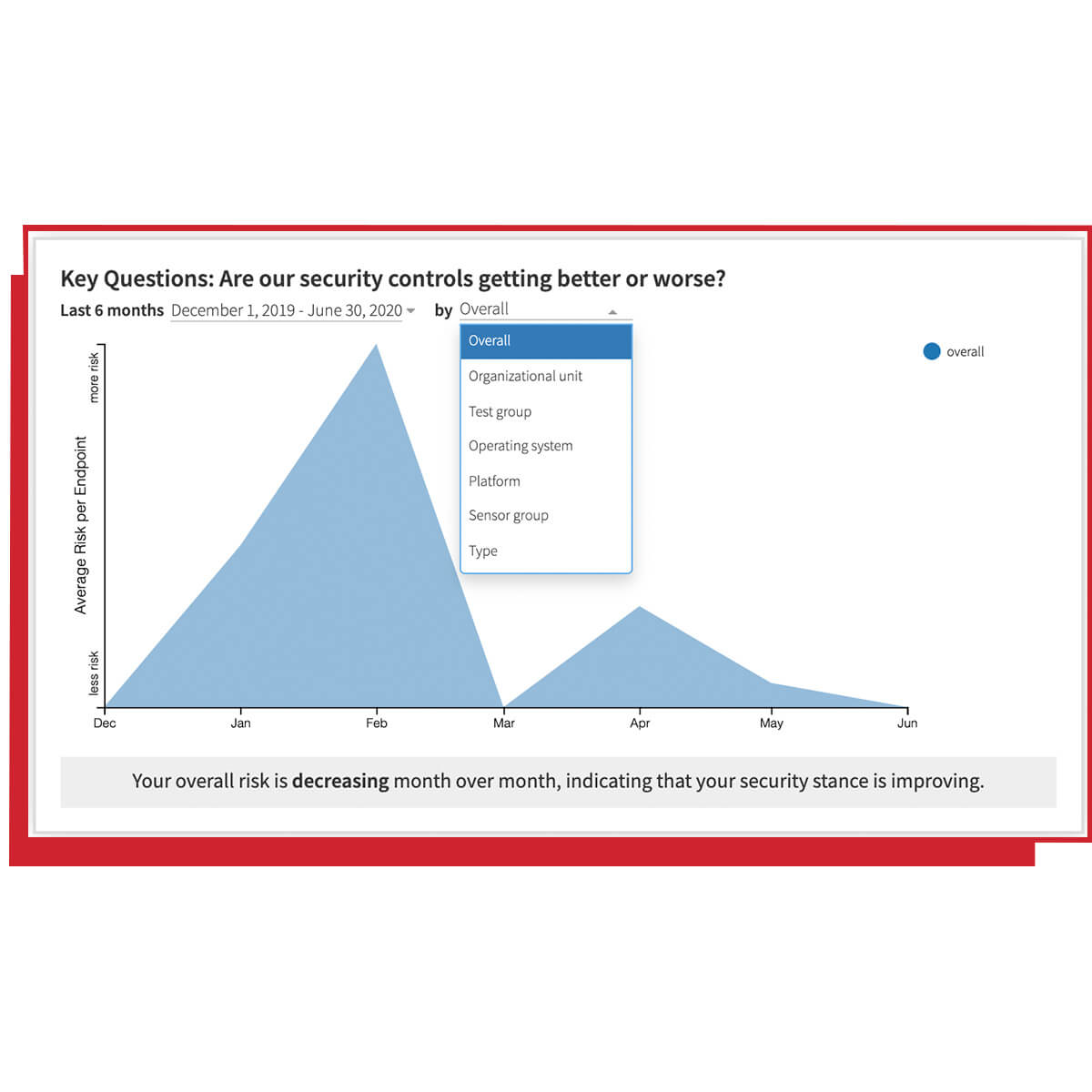
Red Canary helps you deploy, configure, and update policies for CrowdStrike sensors. We ingest your product alerts and analyze your endpoint telemetry using our cloud-based detection engine composed of thousands of behavioral analytic use cases.
Hunt adversaries and evolve detection
Red Canary researches new attacker behavior and continually combs your environment. We maintain industry-leading detection coverage by updating our library of behavioral analytic use cases hundreds of times per week in response to new attacker behavior.
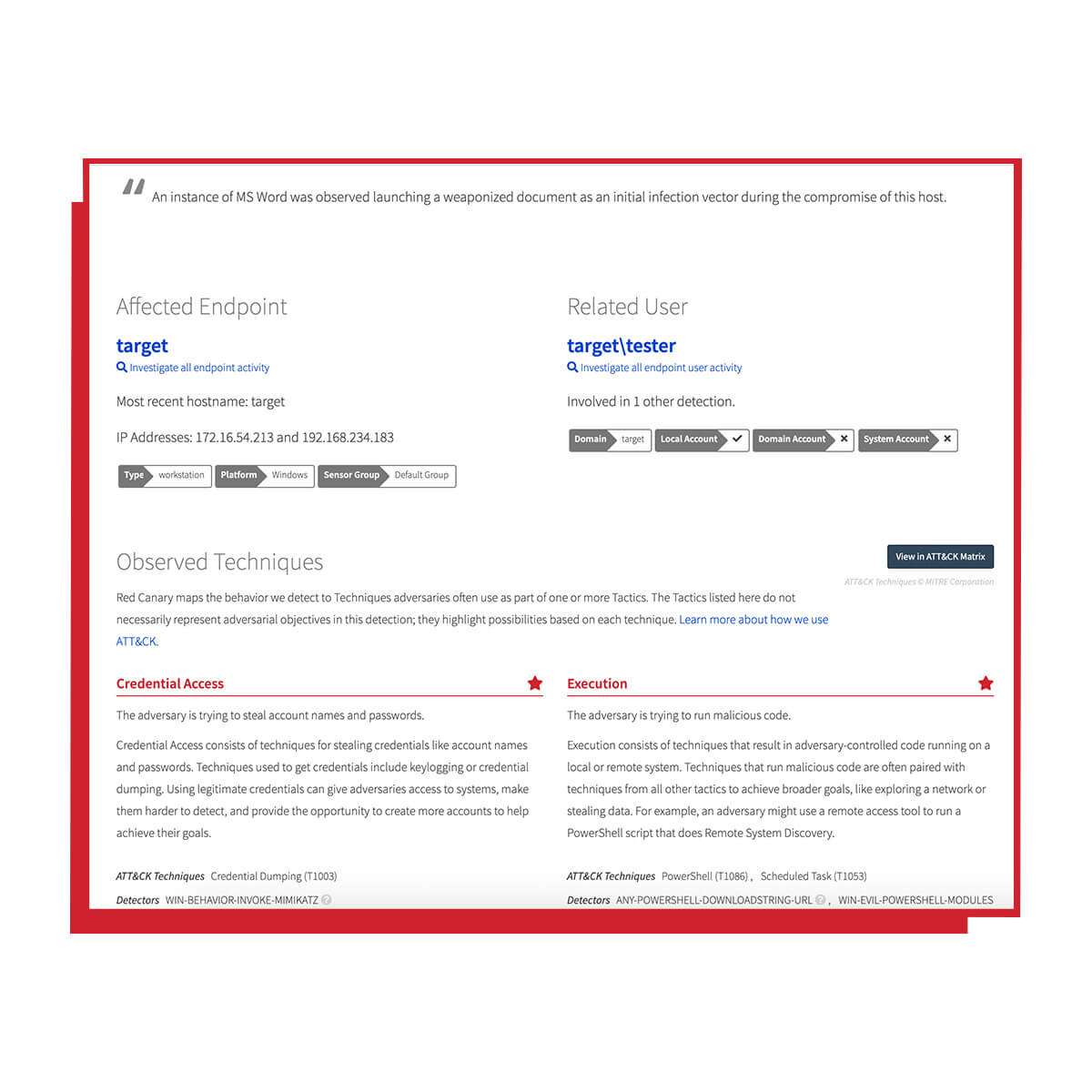
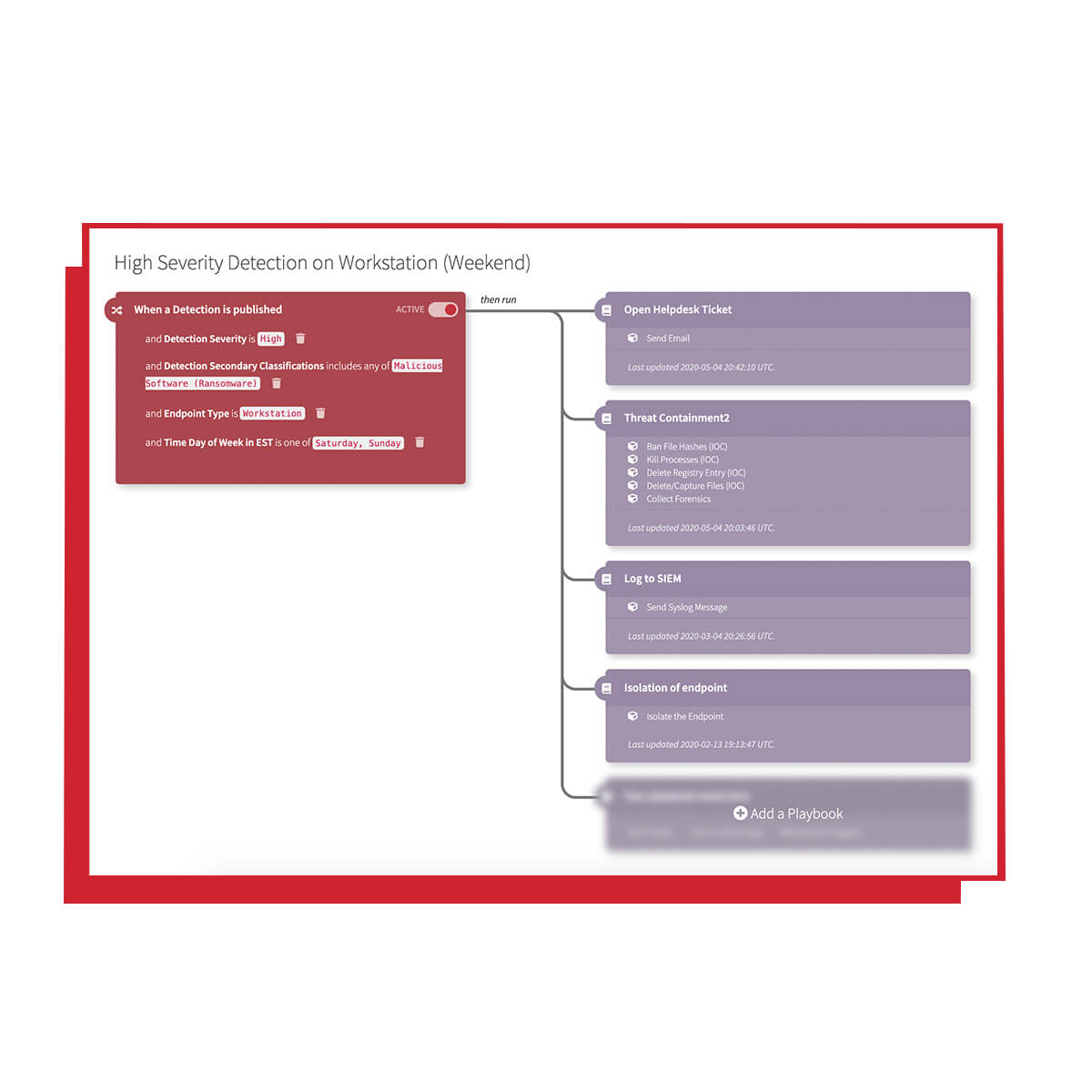
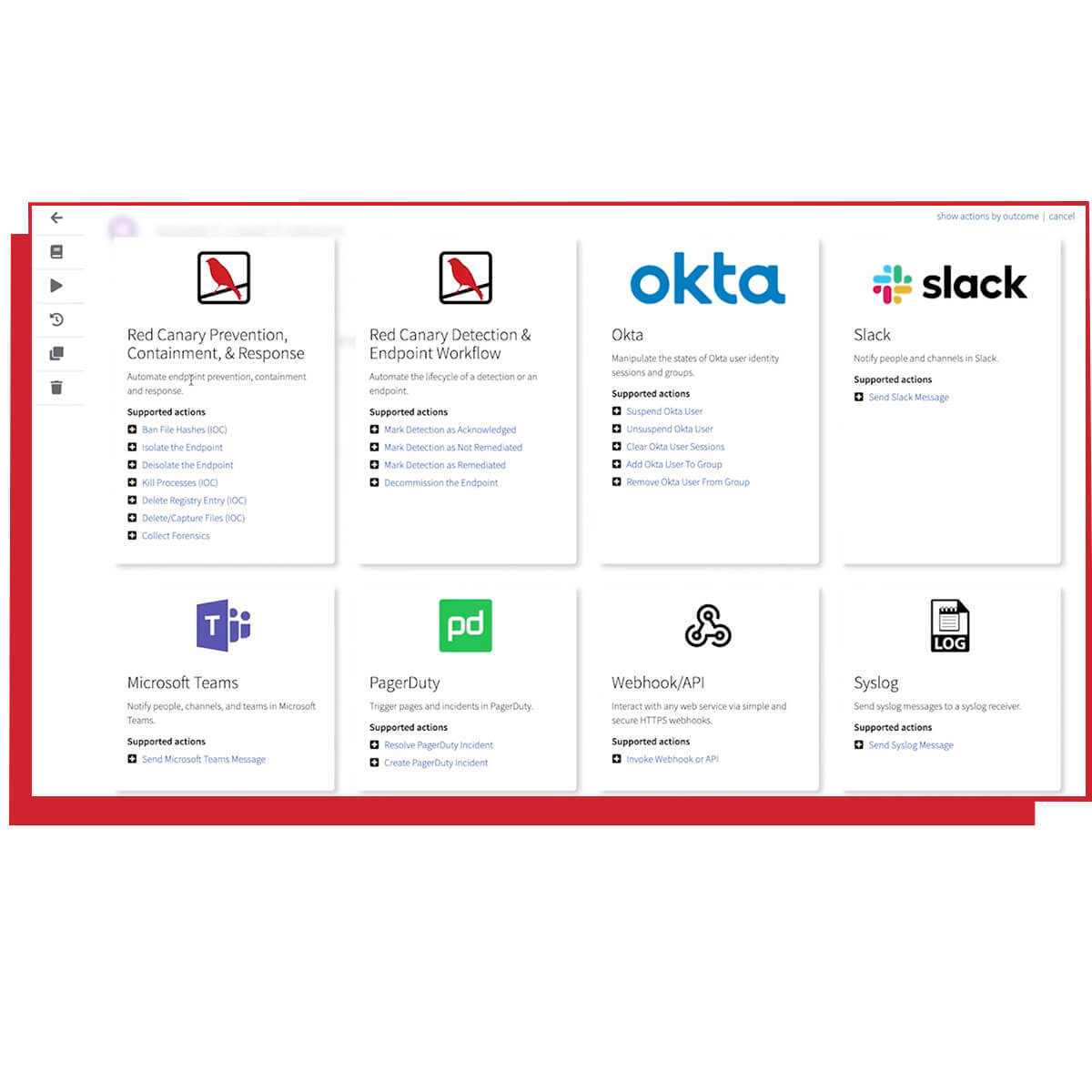
Offload investigations and add automation
We perform full investigations using our proprietary security operations platform and only alert you to confirmed threats. A detailed threat report is posted in your Red Canary portal where you can customize automated response actions and playbooks.
Managed Response for CrowdStrike
Our response engineers can perform managed or active remediation and containment within your environment.