The corporate headquarters of a popular fast-food chain needed better visibility on its macOS machines. The business had a number of preventive measures in place, including traditional antivirus on its Macs and application whitelisting on its Windows devices. Yet when the security team ran internal tests, they were frequently able to evade defenses and sometimes uncovered hidden threats that had established persistence on machines.
The information security engineer (we’ll call him Rick) explained: “Some people don’t believe Macs can be attacked, but we knew that we needed a better solution for detecting and stopping threats. After running internal red team exercises and phishing tests, I successfully got a Python Empire shell onto one of our Macs. Antivirus has zero chance of finding something like that at the time of infection.”
BUSINESS SNAPSHOT
5K
employees
450+
macOS devices
3.5K+
Windows devices
Testing grounds
The team began looking at Endpoint Detection and Response (EDR) solutions to gain visibility and cover the gaps. Realizing that an EDR tool would require a great deal of hands-on management, they focused on fully managed solutions to get more immediate value.
Rick recounted the team’s evaluation of Red Canary. “We ran a number of tests to put the solution through its paces. Red Canary caught them all. Aside from efficacy, another thing that stood out was the solution’s agility. We requested a new authentication header so we could send detections to our incident tracking system. Within a few hours, it was in production. Having something like that done so quickly was awesome to see.”
The team initially deployed Red Canary for macOS coverage, but they have since extended Red Canary to defend most of the business’s Windows devices as well. Having the solution across the environment gives the team confidence that advanced attacks are not being overlooked.
Key results
Rick and his security team saw a number of improvements after partnering with Red Canary.
Time saved
“We used to have to invest a lot of time combing through logs, hunting, finding bad things, and responding to them. We were always making incremental improvements, but it still felt like we were treading water. Having Red Canary as a partner has enabled us to put EDR aside and evaluate the areas where we can do better.”
Improved coverage
“We ran a multi-week engagement with a professional services firm to do a Red Team exercise with us. They sent a beautiful phish with fantastic social engineering, and one of our corporate Mac users fell for it. Very shortly after the firm dropped Empire on the Mac, Red Canary caught it. It was awesome to read the firm’s pen test report remarking how quickly they were ripped off that machine.”
Continuous research
“I remember watching a live stream of Matthew Graber from Specter Ops giving a talk at DerbyCon about subverting trust by modifying the behavior of Windows built-in code signing validation. I could see the sample code in his slides well enough to type the code and try it out. Sure enough, Red Canary detected it. Matt was still explaining how the technique worked and when I tried to emulate it, I got a Red Canary detection. I was blown away.”
Reduced stress
“With Red Canary watching our endpoints for threats, we can take our time and make wiser decisions with other security expansions. Instead of frantically trying to plug a hole while getting ransomware threats every day, we’re able to find ways to make what we have better.”
RESULTS
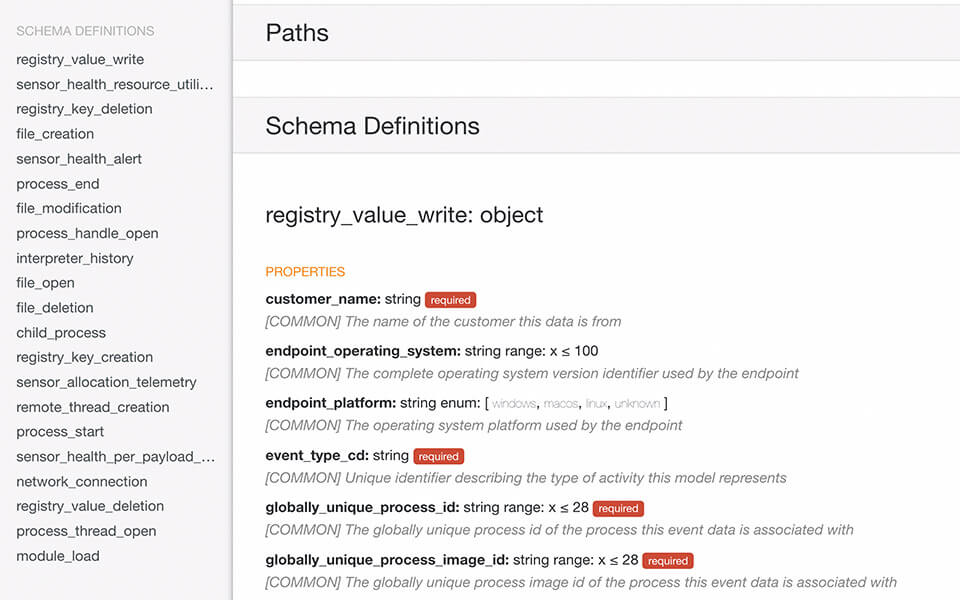
Transforming data into action
When Rick and his team begin looking at EDR solutions, they quickly realized that a managed solution would provide more immediate value. Red Canary records robust endpoint telemetry and applies multiple layers of analysis to detect threats, then arms security teams with context to quickly understand what happened and take action.
Rick explained, “Other solutions can’t provide us with the same level of reliable data collection or the depth of Red Canary’s detection library. Even if we had all the same data, we wouldn’t be able to use it as effectively.”
Detecting macOS threats
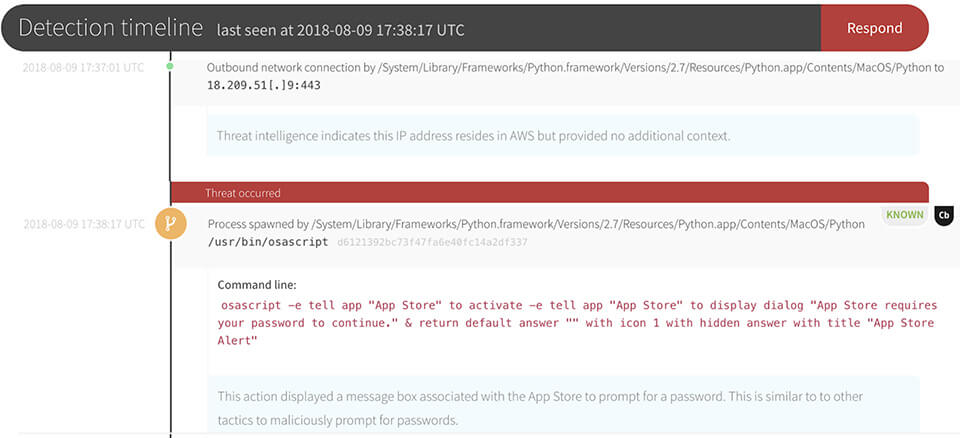
Big believers in the value of testing, Rick and his team consistently test Red Canary’s detection coverage by running adversary emulation tests in his environment, both with Atomic Red Team tests and real-world post-exploit tooling.
In this example from one of the team’s tests, Red Canary detected Python executing and attempting to initiate outbound connections, a common indicator of the Empire post-exploit framework on macOS. Red Canary’s Cyber Incident Response Team (CIRT) then provided context on observed reconnaissance and privilege escalation techniques.


Extending the team
EDR expertise is hard to find. By partnering with Red Canary, Rick and his team could gain access to a lineup of EDR experts without having to staff up internally. Red Canary’s CIRT monitors endpoint data 24×7, detects and validates threats, and quickly alerts Rick and his team when they need to take action.
Rick and his colleagues see Red Canary not as a vendor, but as a true ally in their security initiatives. He said, “Knowing that Red Canary is looking for suspicious activity around the clock gives us great peace of mind.”