Recently, two analysts on Red Canary’s Intelligence Team had a disagreement on Twitter. Don’t worry, it was friendly!
In a thread about Qbot, Stef Rand noted that she had been using the terms “dropper” and “loader” interchangeably. Her colleague Harrison Van Riper replied that he considered them to be two distinct terms, specifying that “all loaders are droppers, but not all droppers are loaders.”
Until today I’ve used them interchangeably! I haven’t really needed to differentiate between them with that level of specificity before now. I kind of like the way this @FlashpointIntel article defines them, but there appears to be no universal consensus.https://t.co/re2VqWjHEB
— Stef Rand (@techieStef) June 14, 2022
So who is right?
We have these friendly debates all the time at Red Canary. As Senior Editor on the Community team, my job is to make sure all of Red Canary’s educational content is compelling, clear, and consistent. I do that by scrutinizing every. single. word.
I wanted to share the rationale behind some of the style conventions we’ve adopted and encourage you to think critically about industry terminology. We don’t claim to be the ultimate authority—style is about establishing a voice of your own, not policing others.
Style is about establishing a voice of your own, not policing others’ language.
What exactly do we mean by “threat”?
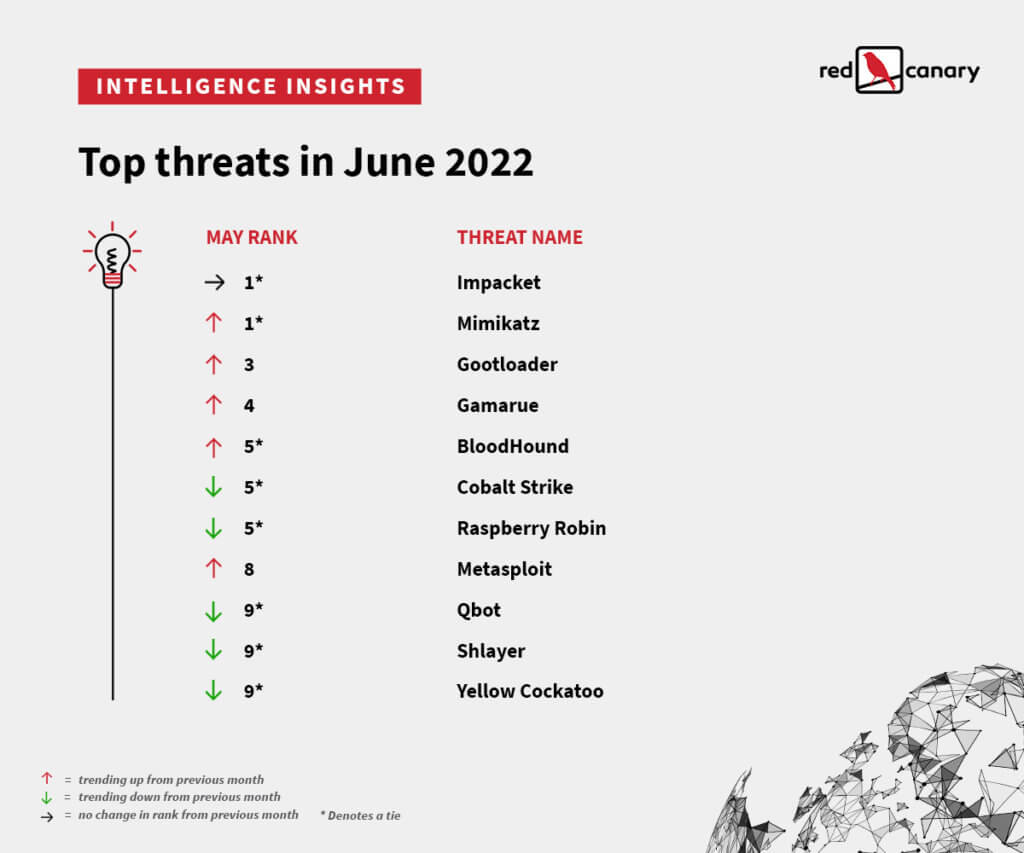
When we say that Red Canary detects threats, we mean any suspicious or malicious activity that represents a risk to you or your organization. You might have noticed that our annual Threat Detection Report, as well as our monthly Intelligence Insights, ranks clusters of activity, specific malware variants, legitimate tools being abused, and known threat actors next to each other. Even though they manifest differently, they all pose risks to your organization.
Each of these threats corresponds to an identifiable pattern of behavior that has been detected in the telemetry we gather from customer environments (1 PB of data per day at our peak). We also detect more generic activity that we recognize as malicious or suspicious but are unable to immediately associate with a named threat or activity cluster. All threats, named or otherwise, represent activity that should be addressed, regardless of who or what is behind it. Our goal is to arm you with actionable insight to stop malicious behavior in its tracks, not speculation clouded by political context.
For more on our philosophy behind attribution, check out our Director of Threat Intelligence Katie Nickels’ blog and the Methodology section of this year’s Threat Detection Report.
Attacker vs. adversary
At Red Canary, we prefer the term “adversary” over “attacker.” “Attacker” implies a desire to cause damage or disruption to an environment, whereas the more general “adversary” encompasses threat actors motivated by espionage, spreading disinformation, and other outcomes.
Attack vs. intrusion
We haven’t banned the word “attack,” we just want to be intentional about when we use it. The word “attack” comes with a lot of legal and political baggage. We favor the more neutral term “intrusion” when referring to a specific compromise, to avoid speculation about an adversary’s intentions. This terminology allows us to take red team and pentesting activity into account as well.
A plug for active voice and descriptive verbs
Sentence structure matters just as much as word choice. Passive voice (which usually results from excessive use of “to be” verbs like is, are, and were) not only sounds clunky, it often results in incomplete or misleading information. For example:
The intrusion was discovered in November 2020.
While this sentence might be grammatically and factually correct, it is ambiguous; who discovered the intrusion? The victim? Their MDR provider? The U.S. government?
Given the amount of unknowns in cybersecurity, it can be difficult to assign an agent to every action (you can’t start every sentence with “Unidentified adversaries did x”). But if you find yourself using a lot of “was” and “were,” consider switching up your verbs for something more descriptive. Another example:
Version 1: The malware was persistent on the victim’s network.
Version 2: The malware spread across the victim’s network quickly, evading defenses.
Which sentence was more informative? Which one was more enjoyable to read?
What if there’s no rule?
Many word choices can’t be defined by a simple style rule–it depends entirely on the context of the sentence, and in the case of dropper vs. loader, it depends on the specific malware variant in question. Equally credible sources can reasonably disagree on the exact definition of technical concept. This is where you have to strike a balance between flexibility and attention to detail.
For muddy terms like these, we have two pieces of advice:
- Be as specific as possible in your phrasing
- Have multiple reviewers weigh in
Rather than blindly follow blanket guidance, consider each sentence in isolation for accuracy and clarity. Consult with your peers, and listen to their perspectives with an open mind. If the conversation is ongoing, you’re doing it right.
If your conversations about word choice are ongoing, you’re doing it right.
The most important style rule is the golden one
Our goal is to be consistent, but not to the point of rigid complacency. We want to evolve with the industry and culture in general. Most importantly, we want to treat everyone in infosec (and beyond) with compassion and respect.
Along with adopting the singular “they,” we also make a point to consult with individuals on their correct pronouns. We have also discouraged the use of “master/slave” and “blacklist/whitelist” in favor of “parent/child” and “allowlist/blocklist.” And we are still listening. Our style guide is a living document, and will always remain a work in process.
If your organization doesn’t have a style guide of its own, consider creating one! The Conscious Style Guide promotes inclusive language. For industry specifics, The Bishop Fox Cybersecurity Style Guide is a great resource to start with.
So what’s the verdict on dropper vs. loader?
We’re still talking it through, and that’s okay! If we reach a consensus, we’ll let you know, and I’ll update the style guide accordingly.