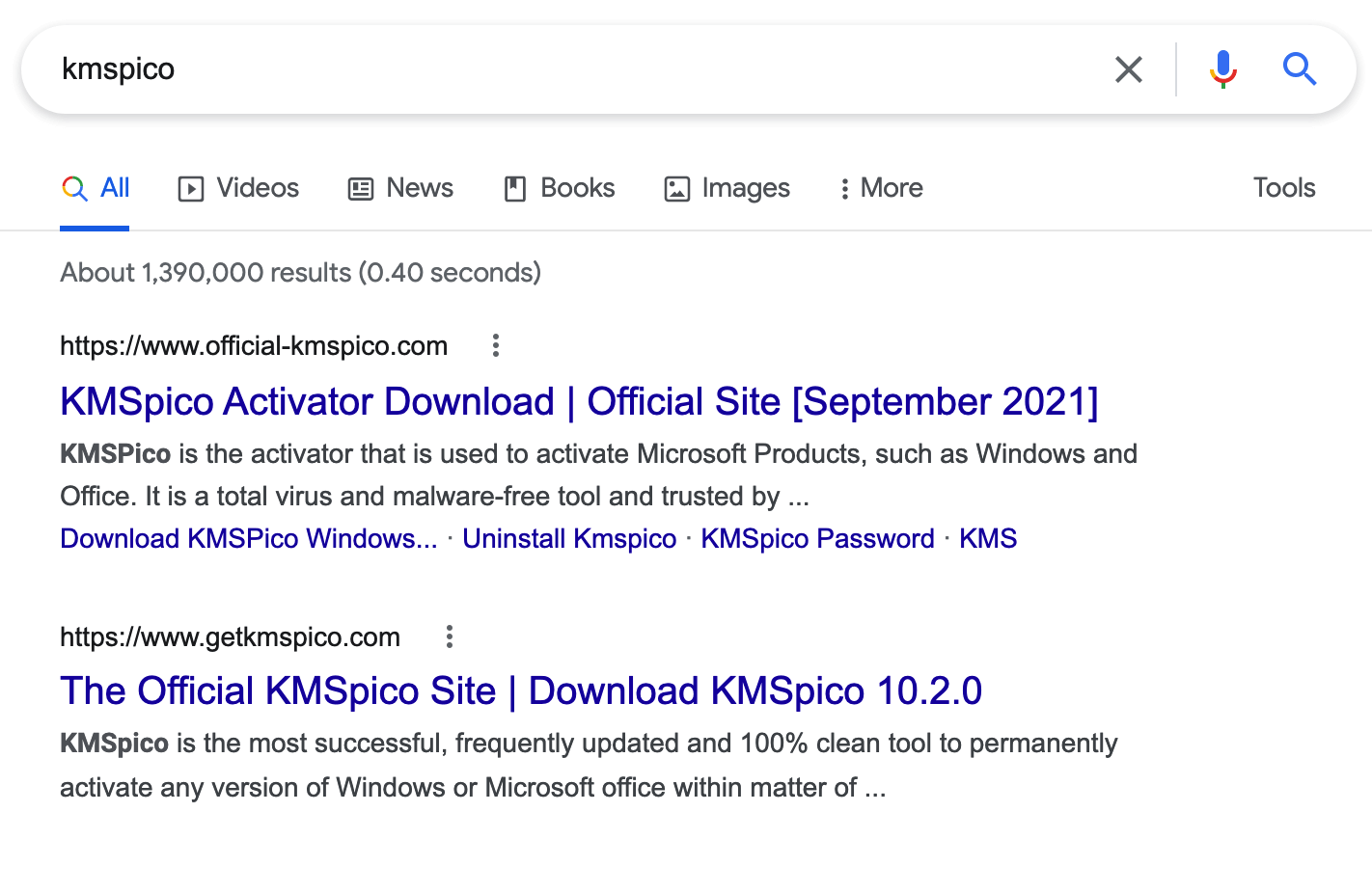
Digital piracy can be a rough lifestyle choice, due in large part to the disreputable sources for cracked software and the exploits used to activate paid features. We’ve seen lots of systems fall victim to malware infection because users installed cracked software and assumed it was just cracked software. In one recent case, we detected a system infected by Cryptbot malware designed to steal credentials and traced that infection back to a fake KMSPico installer. This article outlines what KMSPico is and how it relates to Cryptbot. We included the malware analysis of KMSPico in a seperate PDF to supplement the information outlined here.
What is KMSPico?
KMSPico is a tool used to activate the full features of Microsoft Windows and Office products without actually owning a license key. It takes advantage of Windows Key Management Services (KMS), a legitimate technology introduced to license Microsoft products in bulk across enterprise networks. Under normal circumstances, enterprises using legitimate KMS licensing install a KMS server in a central location and use Group Policy Objects (GPO) to configure clients to communicate with it. KMSPico, on the other hand, emulates a KMS server locally on the affected system to fraudulently activate the endpoint’s license.
Even when KMSPico isn’t tainted with malware, it’s not legitimate software either. In the best cases when someone gets the real installer, it’s only used for license circumvention. Since multiple antimalware vendors detect license circumvention software as a potentially unwanted program (PUP), KMSPico is often distributed with disclaimers and instructions to disable antimalware products before installing. Alongside the difficulty in finding a clean download, the disabling instructions prepare unwitting victims to receive malware.
We’ve observed several IT departments using KMSPico instead of legitimate Microsoft licenses to activate systems. In fact, we even experienced one ill-fated incident response engagement where our IR partner could not remediate one environment due to the organization not having a single valid Windows license in the environment. KMSPico and other non-official KMS activators circumvent Microsoft licenses and are a form of pirated software, posing a non-trivial risk to organizations. Legitimate activation on Windows is the only method supported by Microsoft.
Will the real KMSPico please stand up?
Cryptbot stealer, the stowaway
Cryptbot has a long history of deployment via various means from adversaries, and it harms organizations by stealing credentials and other sensitive information from affected systems. Lately, it has been deployed via fake “cracked” software, and in this case it’s particularly insidious by posing as KMSPico. The user becomes infected by clicking one of the malicious links and downloads either KMSPico, Cryptbot, or another malware without KMSPico. The adversaries install KMSPico also, because that is what the victim expects to happen, while simultaneously deploying Cryptbot behind the scenes.
Cryptbot is capable of collecting sensitive information from the following applications:
- Atomic cryptocurrency wallet
- Avast Secure web browser
- Brave browser
- Ledger Live cryptocurrency wallet
- Opera Web Browser
- Waves Client and Exchange cryptocurrency applications
- Coinomi cryptocurrency wallet
- Google Chrome web browser
- Jaxx Liberty cryptocurrency wallet
- Electron Cash cryptocurrency wallet
- Electrum cryptocurrency wallet
- Exodus cryptocurrency wallet
- Monero cryptocurrency wallet
- MultiBitHD cryptocurrency wallet
- Mozilla Firefox web browser
- CCleaner web browser
- Vivaldi web browser
Note: For an in-depth analysis of the malicious KMSPico installer, you can read our full malware analysis in this PDF.
Behavioral detection shores up signature-based detection
This distribution of Cryptbot continues a trend we’ve seen in recent threats, such as Yellow Cockatoo/Jupyter. Adversaries continue to use packers, crypters, and evasion methods to stymie signature-based tools such as antivirus and YARA rules. As these threats grow more complex with their obfuscation, they must exert an equal and opposite effort to remove that same obfuscation after delivery to run the malware. During this delivery and obfuscation process, behavior-based detection shines and helps close gaps on malicious activity that might otherwise get missed.
In this case, the adversary used the CypherIT AutoIT crypter to obfuscate Cryptbot, and no cleartext Cryptbot binaries existed on disk. Despite the obfuscation, we could still detect the threat by targeting behaviors that delivered and deobfuscated the malware. For this threat, the following detection strategies helped us.
Detection opportunity: CypherIT
Search for binaries containing AutoIT metadata but don’t have “AutoIT” in their file names
AutoIT processes making external network connections
findstr commands similar to findstr /V /R "^ … $
Detection opportunity: Cryptbot
PowerShell or cmd.exe commands containing rd /s /q, timeout, and del /f /q together
Conclusion
A pirate’s life is not the life for us, especially when it comes to cracked software. KMSPico is license-circumvention software that can be spoofed in a variety of ways, and in this case a malicious version led to an interesting Cryptbot infection designed to steal credentials. Save yourself the trouble and go for legitimate, supported activation methods.