It’s beginning to feel a lot like Christmas with 12″ of snow outside our headquarters in Denver, incessant car commercials on TV, and a brand new Star Wars movie! And as much as we hate every company in the world co-branding with Star Wars (looking at you Chrysler), we’re jumping on board long enough to highlight similarities between the movie and what every information security professional learns every day.
#1 Beware the insider threat!

This would have been have been a pretty short movie if the First Order had an insider threat detection system combined with a working security re-education program. They did a good job detecting anomalous behaviour (a Stormtrooper not shooting civilians, taking his helmet off), but their re-education failed. Security education of a malicious insider is worthless – if they don’t believe in your mission, they are a continual risk.
We’ve long espoused the power of user behavioural detection using detailed endpoint data to identify both malicious insiders and the “accidental insider threat” that endangers your business through ignorance or carelessness. Security awareness training is important, but it only works when your users care about your business.
#2 The bad guys are always upgrading
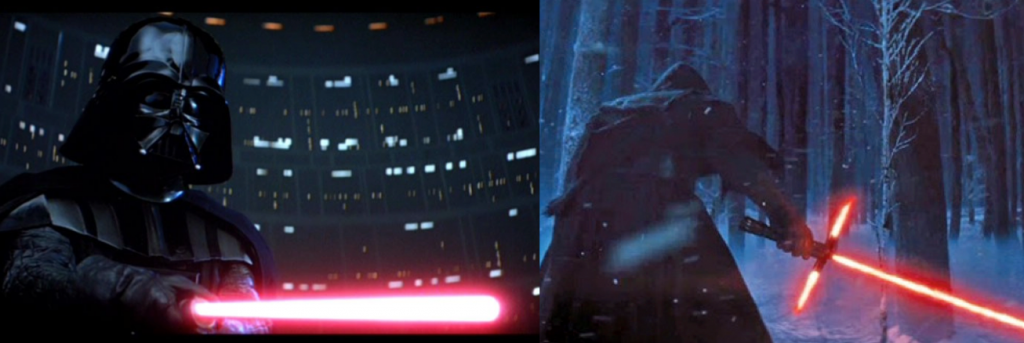
Kylo Ren’s lightsaber has a crossguard with three perpendicular blades. Darth Vader only had a single blade. The First Order’s Starkiller Base is about 30x the size of the Death Star and is powered by the sun – a big upgrade compared to a mere superlaser.
In information security, the great technology advances of the past decade have benefitted attackers as much as they have defenders. Attackers can use Ransomware-as-a-Service providers to quickly craft new attacks. Dynamic DNS and cloud computing services give the bad guys immense flexibility in continuously morphing their infrastructure to remain undetected. And oftentimes, defenders are continually pivoting to respond to the new tactics and techniques attackers are using.
#3 You are always vulnerable somewhere
You just built a great security program. Hired the best talent. Conducted monthly third-party security assessments. Built cybersecurity support at the executive and board level. And the attackers still got in. Remember – the attacker only needs to succeed once. You have to succeed every single time.
The First Order converted an entire planet into a sun eating, star-system decimating, weapon of mass destruction. And all it took was one set of compromised user credentials entered into the system to drop the shields faster than you can shout “Han shot first!”. Talk about a much needed security re-education program.

#4 There are never enough good guys
The Rebel’s small force with dozens of pilots and less than 30 X-wings is no match for a direct confrontation with the First Order’s army of hundreds of thousands of soldiers. Even worse, the Rebels have what we call a “scalability problem” in that they don’t simply kidnap and brainwash young children from around the galaxy.
We all know there is a massive Infosec security skills shortage right now – and it is projected to get significantly worse (to the tune of 1.5M open positions by 2020). This means that most organizations do not have enough human capital to build a successful security posture that can defend against attackers.

#5 Innate ability often outweighs training
No matter who your Jedi master was or how many SANS courses you attended, the best security teams have individuals with innate excellence at their craft (“metachlorians” in Star Wars speak). They love hunting through data looking for the potentially threatening events, always improving their technique, and tearing apart new attackers to better defend against them.

Well done to the Force Awakens team on a great movie that gets us all excited for the coming sequels. As we head into the holidays, beware the increasing threats from attackers, and (wait for it….)
may the force be with you!