We are very excited about our new partnership with CrowdStrike®. Red Canary can now provide our industry-leading hunting and response using Falcon’s Endpoint Detection and Response (EDR) data.
We have a very simple goal at Red Canary: to make companies’ security better. From day one, we started with that single goal and asked what we could do to make the biggest difference to security teams. We found that the biggest worry for most security teams was whether they’d be able to detect a successful attack and how long it would take them to find it and recover. Most security products and services are focused on “before” an attack. We set out to deliver a solution that materially improves the “after” — finding and investigating successful attacks.
Priority #1 in building a hunting and response capability is the correct level of visibility. The best visibility data available is at the endpoint. That is where the rubber meets the road for attackers, so that is where we need to meet them. Up until now, there was only one EDR product that provided the level of data collection, export, and API access to meet our standard for visibility and give us the confidence we could perform the broadest detection in the industry.
Today there are two products that meet that standard.
For over a year, we’ve been working with the exceptional team at CrowdStrike to integrate the endpoint telemetry collected by the Falcon platform into Red Canary. Truth be told, the technical integration was fairly simple. CrowdStrike has continuously added great APIs, and the introduction of the Falcon Data Replicator last year was the final piece in our integration puzzle. We have spent the last year working with a small set of customers to ensure we could provide a product that met our standards for quality. If we don’t believe we can make security better by integrating with a product, we just don’t do it. We can with CrowdStrike.
How does it work?
The integration is relatively simple:
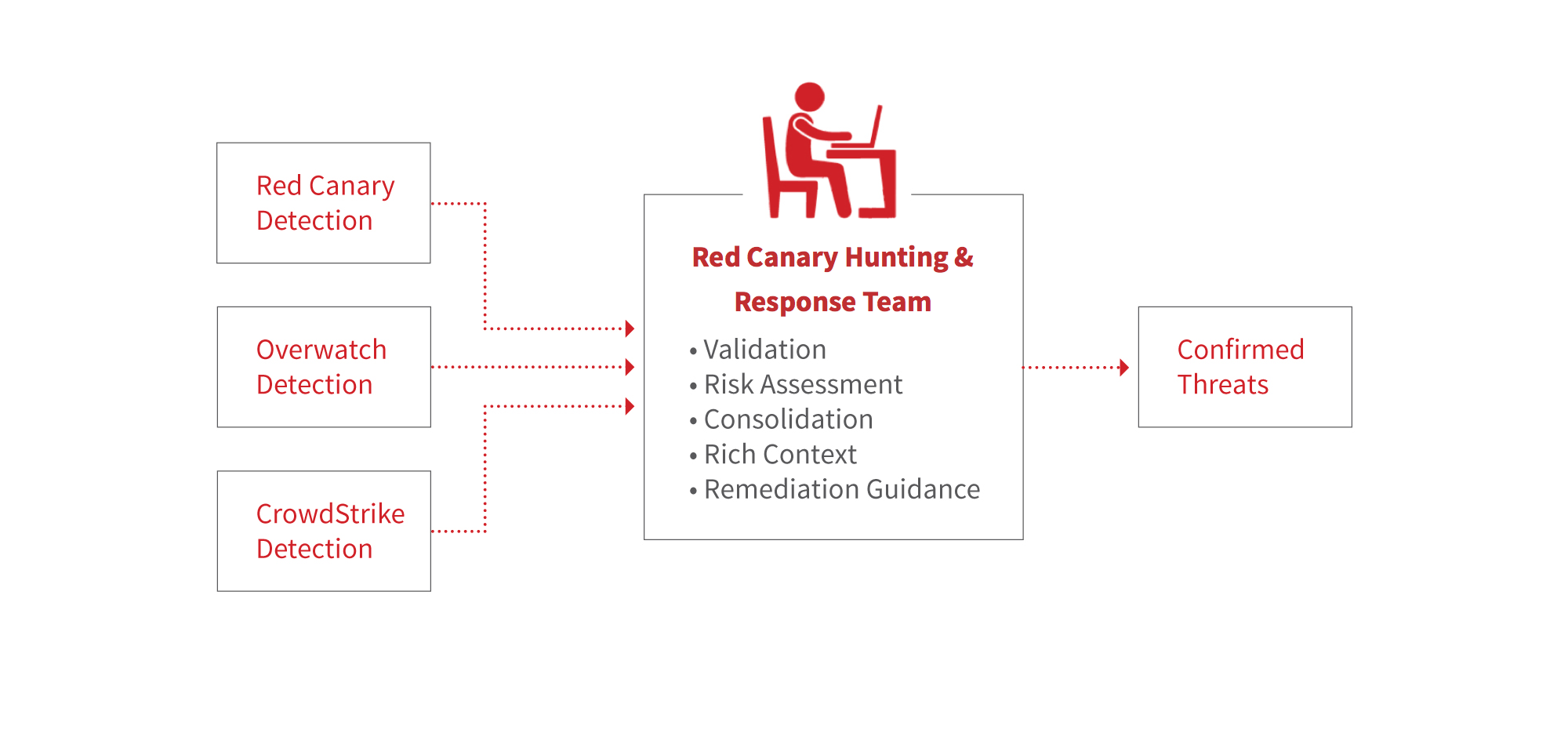
- Falcon ships all of the endpoint telemetry it collects to Red Canary.
- Red Canary standardizes the telemetry into its internal format.
- The Red Canary Engine analyzes the data and surfaces potential threats.
- Red Canary analysts investigate and confirm threats and publish full-context detections to the customer.
Red Canary also connects to the Falcon Streaming API to get a feed of threats surfaced by CrowdStrike’s detection capabilities, including Overwatch. Red Canary’s analysts confirm and consolidate these threats as well.
Red Canary with CrowdStrike is available today and we’d love to show it to you. Request a demo.