This week, iSight Partners and Microsoft announced CVE-2014-4114 – “Sandworm”. While Microsoft has released a patch, exploit activity has already been identified in the wild.
Red Canary customers will be pleased to know that within 24 hours of the CVE-2014-4114/Sandworm vulnerability’s announcement, we were successfully detecting the threat on their systems. Our team quickly identified the endpoint observations that indicate exploitation has occurred due to this vulnerability. This was done without code signatures, so any future exploits written to exploit the CVE-2014-4114/Sandworm vulnerability will also be detected. The Red Canary research team is always monitoring developments in the exploit market to update our detectors as needed. This ensures we can stay abreast of the changing landscape.
Although the Microsoft patch addresses the CVE-2014-4114/Sandworm vulnerability, patch application is often delayed. We always recommend applying patches as soon as possible. However, if you must delay, rest assured that any Red Canary customer experiencing a realized threat within their environment – meaning exploitation has occurred – will be alerted to the detected threat with the following:
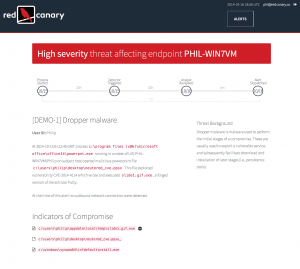
This detection alert arrives after our analysts have examined the evidence and crafted an actionable alert message containing all details necessary for our customers to perform fast and effective remediation. This generally occurs within hours of exploitation. Our methods are independent of flawed signature-based detection methods like antivirus and intrusion detection/prevention systems. Attackers can trivially change the signatures of their malware, as well as the network communication paths such as command and control servers to thwart network-based detection.
By focusing strictly on endpoint observations – the one place an attacker cannot easily conceal their behavior – Red Canary’s customers enjoy an unparalleled level of awareness when compared to other previous-generation products and services. By minimizing the time between exploitation and detection, and with actionable alerts to enable comprehensive remediation, Red Canary continues to change the game in Incident Response.