Disclaimer: Scenarios depicted in this blog are fictional and intended for educational purposes.
Imagine the office of a bustling healthcare supplies manufacturer with employees immersed in their work, unaware of the lurking threat that awaits them. Suddenly, a panic-inducing message flashes on the screens of everyone’s endpoints—a directive from the infamous ransomware group Black Basta warning of an attack underway. Mayhem ensues as systems crash, critical data becomes encrypted, production screeches to a halt, and the environment descends into a state of confusion. As the security team scrambles to contain the breach and get systems back online, it becomes painfully clear that the organization’s incident response plan was sorely lacking.
This scenario serves as a sobering reminder of the importance of preparedness and proactive training in a rapidly changing cyber landscape.
Training challenges
If adversaries have taught us anything, it’s that we defenders can’t afford to come in last. The mere prospect of training up on all relevant threats, techniques, and trends is similar to chasing a shape-shifting villain in the proverbial night: resource intensive and darn near impossible. In addition, traditional cybersecurity training presents several challenges that hinder its effectiveness: busy schedules and a lack of engagement due to technical complexity, as well as difficulties in measuring success and value. Overcoming these challenges—and avoiding scenarios similar to the one above—requires a more consistent, engaging, tailored, and measurable approach for security teams looking to upskill and prepare.
Enter Red Canary Readiness Exercises.
We’re introducing a first-of-its-kind learning platform designed specifically for defenders and the environments they serve, combining real-world training scenarios, tabletop exercises, and Atomic Red Team tests into one seamless experience.
What makes Readiness Exercises so special?
As someone who has worked in a Security Operations Center (SOC) and participated in several training drills myself, I can vouch that they often do not reflect the reality of “being in the trenches.” They tend to focus more so on knowledge transfer versus executing effectively, under pressure, as a team. Red Canary’s Readiness platform is made for defenders… by defenders.
What makes it even better: you don’t have to be an existing MDR customer to use it.
Practitioner benefits
Improve technical skills
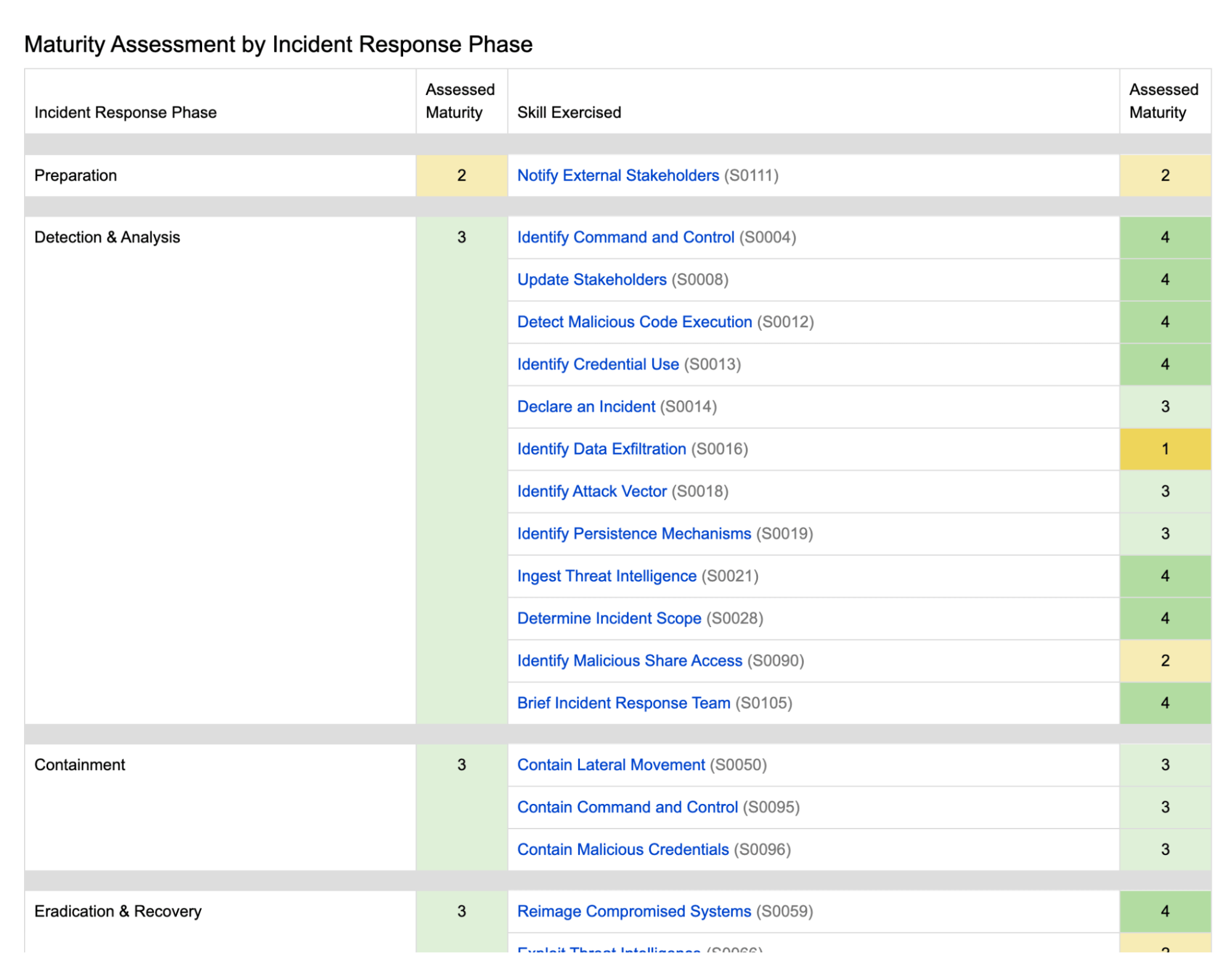
Whether an exercise is designed to test detection capabilities, containment skills, or something else altogether, understanding what to do and how to do it is foundational to maturing as a defender. Throughout each exercise, skills are measured on an individual (and team) basis, providing a direct feedback loop to identify areas for growth upon completion.
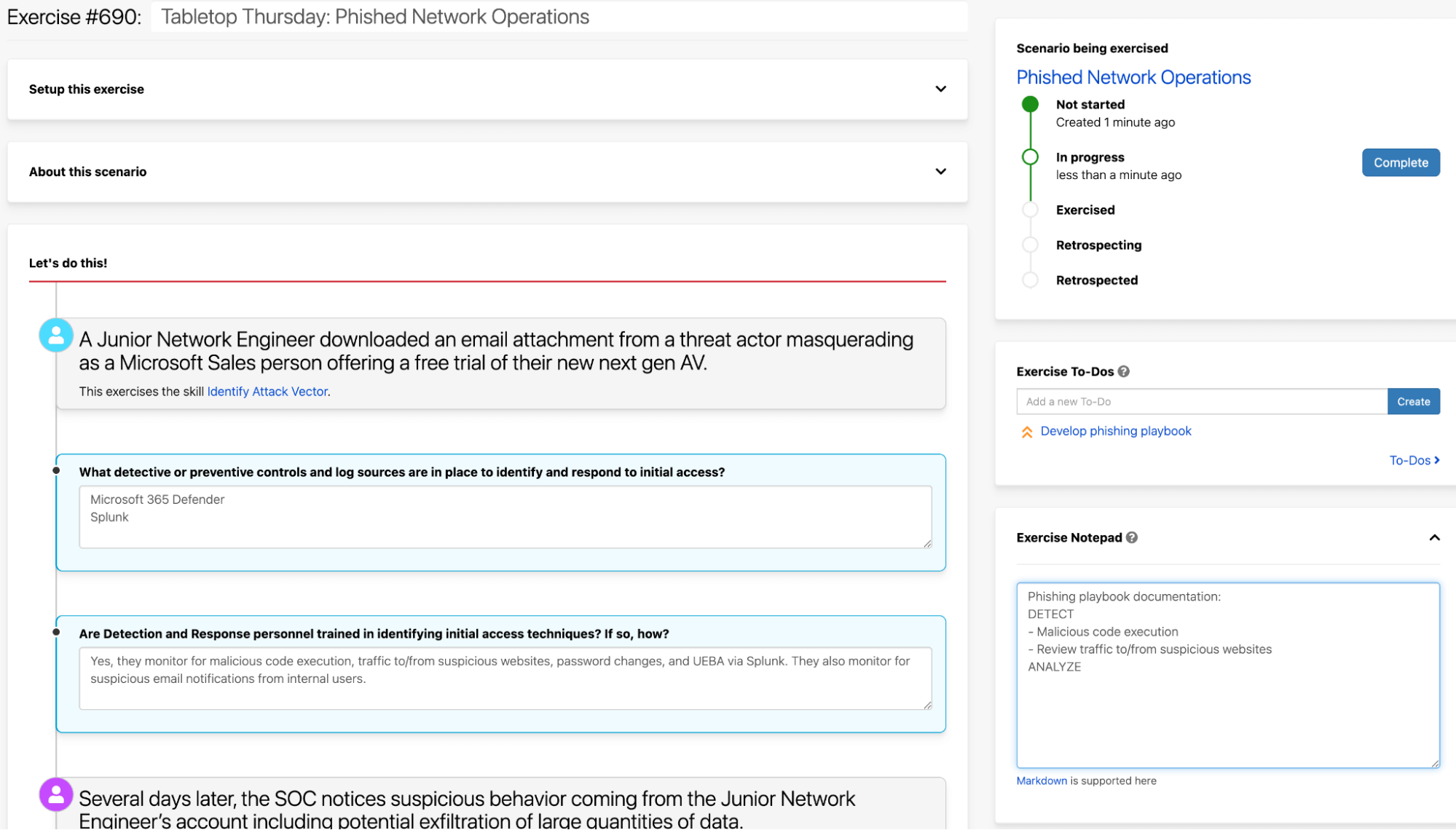
Develop playbooks
For incident handlers and analysts, playbooks are life! As such, we’ve pulled together top threats, techniques, and trends—based on the 2023 Threat Detection Report—and rolled them into real-world scenarios aimed at putting your workflows to the test. If you don’t yet have a playbook for a given scenario, workflow prompts and the timeline overview serve as guided checkpoints for drafting up blueprints with your teammates along the way.
Security leader benefits
Practice response
Sure, your team’s playbooks may offer up a solid game plan, but every team responds differently due to the uniqueness of its people, environment, and the data it protects. With this in mind, we developed Readiness Exercises to provide a safe haven of sorts, allowing you to work through technical gaps and process bottlenecks on your own terms, instead of the adversary’s. Some of the scenarios are anchored by our open source Atomic Red Team tool, so you can test relevant threat-specific techniques within your environment.
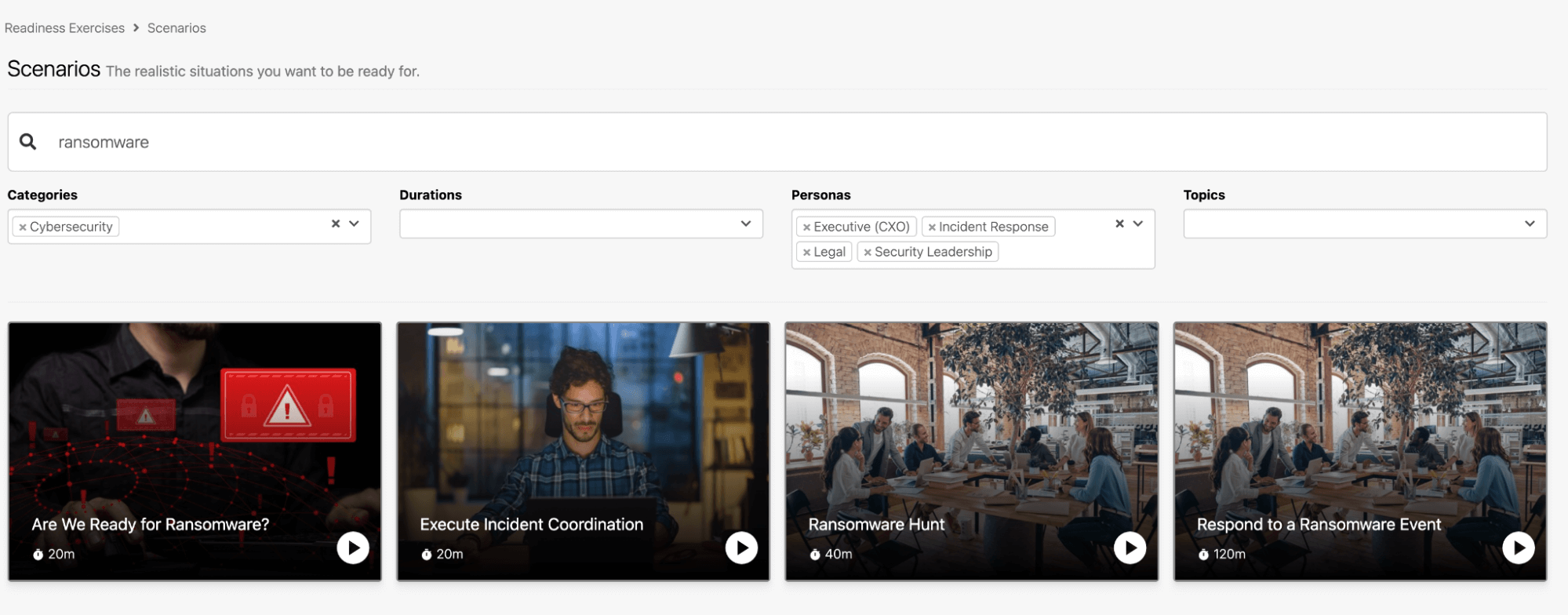
Continuous training
Security leaders are tasked with making sure their team is always ready for the fight. Given time and budgetary constraints, this is often a tall order. This platform provides interactive year-round drills that can be tailored to your team and the threats you face. And—since we know your time is valuable—we’ve categorized scenarios by duration, personas, and topic so you can align training to your team’s needs and availability, incentivizing the whole team to conduct training exercises more frequently.
CXO benefits
Framework mapping
If it’s compliance and structure you’re worried about, we’ve got you covered. The platform is built on the following industry-leading frameworks:
- Response skills: NIST Incident Response Life Cycle
- Adversary tactics and techniques: MITRE ATT&CK
- Reporting: COBIT-2019
Each framework focuses on different aspects of cybersecurity, providing a more comprehensive approach when used together. NIST offers a holistic framework for managing and mitigating risks, focusing more so on areas such as risk assessment, incident response, and security controls. ATT&CK provides detailed insights into adversary tactics, techniques, and procedures, enabling organizations to better understand and defend against real-world threats. COBIT-19 emphasizes governance and control objectives for IT systems, ensuring effective management and compliance overall. Having all three frameworks baked into one platform means that you can feel confident in knowing your organization is addressing a broader range of cybersecurity concerns that is directly aligned with your business goals.
Automated reports
What normally takes weeks now takes seconds. With this feature, leaders and CXOs have the ability to create audit-ready reports on the fly, for internal and external purposes. Whether it’s an individual skills or company-wide cybersecurity maturity assessment, details can be generated in real time post-exercise. Gone are the days of paying thousands of dollars per drill to gather such details; the future of cyber assessments is here.
Is this right for my team?
Do you even data, bro? Yes! If you are part of a security shop tasked with protecting and defending a network, this platform is right for you. Not only is it right for you, it’s made for you. Upleveling your team’s skill set and preparedness is a surefire way to ensure your team is as ready as ever to take on the inevitable.