Amber Albatross
The most prevalent threat we detected in 2025, Amber Albatross now masquerades as various PDF utilities as well as potentially unwanted programs like PC App Store.
#1
Overall Rank
11.1%
Customers Affected
Amber Albatross is a Red Canary-named activity cluster that we have been tracking since January 2024. The activity encompasses download and installation activities that consistently lead to a Pyarmor-obfuscated PyInstaller executable with stealer-like capabilities. We have consistently observed Amber Albatross installers as a payload delivered by potentially unwanted programs (PUP), including Bit Guardian software, and PC App Store. In 2025, infections from PC App Store installers continued. We also saw additional infections from installers masquerading as PDF utilities.
The Amber Albatross intrusion chain contains multiple stages with anti-analysis techniques that make sandbox analysis difficult, and the final payload is heavily obfuscated. We assess that this activity is nefarious due to suspicious reconnaissance activity and its heavy obfuscation.
We first reported on Amber Albatross in our July 2024 Intelligence Insights.
The Amber Albatross intrusion chain contains multiple stages with anti-analysis techniques that make sandbox analysis difficult.
Intrusion chain
In 2025, installations from the potentially unwanted program PC App Store continued and we saw a small resurgence of installations through another PUP, Bit Guardian’s Win Riser. We also observed a revolving door of installer themes, mostly masquerading as PDF utilities. These installers, while signed, used a variety of different signers. The ever-changing signers and names of these utilities all performing the same reconnaissance and leading to the same Pyarmor-protected binary leads us to consider them more akin to masquerading malware than PUPs. Beyond the variable delivery mechanisms, Amber Albatross also updated some later stage TTPs—notably adding obfuscation through Base64-encoded PowerShell commands to download and execute later stage payloads, and migrating some of their second and third stage payloads from C++ to Go.
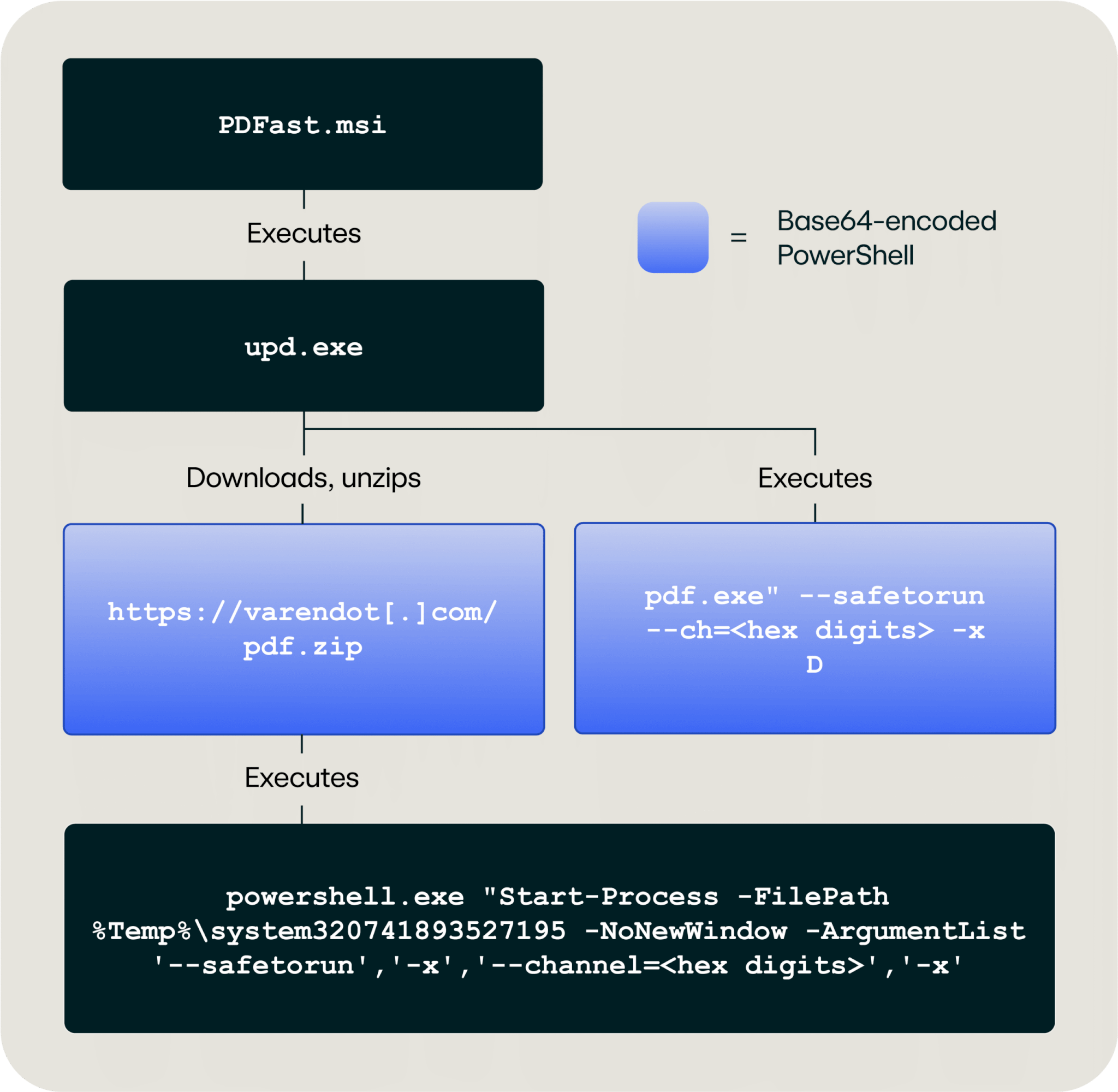
The installation activity also showed more variation this year. The installation path for the PC App Store variant, the most common initial access vector, remained the same. The PDFast lure was the second most common installation method, following a similar pattern to the “Let’s Compress” lure that began in late 2024. This variant dropped a binary named upd.exe leading to downloads and execution via Base64-encoded PowerShell commands. The charts below walk through the installation paths used to deliver Amber Albatross’s PyInstaller executable for each program.
PC App Store
PDFast
The final payload
Regardless of the initial infection chain, the final Amber Albatross payload–the PyInstaller file—will immediately perform reconnaissance, similar to what we typically observe from stealers. During the reconnaissance phase, the malware will use WMIC to detect if there is a hypervisor present on the endpoint as well as enumerate the manufacturer, model, and list of Windows software updates. The PyInstaller file also checks for antivirus and firewall products, and based on analyzing memory dumps looks for a wide range of browsers and their development versions, including:
- Edge
- FireFox
- Chrome
- Chromium
- Avast Browser
- Brave
Once it identifies the browsers utilized on the endpoint, the PyInstaller EXE will attempt to access browser profiles or user data folders. For Chrome, we have seen Amber Albatross check the value of the following registry key:
HKLM:\SOFTWARE\Policies\Google\Chrome\CloudManagementEnrollmentToken
This key is set during enrollment for managed browsers, allowing Amber Albatross to determine if the browser might be controlled by corporate policy. We have yet to discern how Amber Albatross uses this information or continues the intrusion chain. However, these reconnaissance activities are typical for stealers.
In 2025, some variations added an additional reconnaissance step of querying the registry for software uninstall keys and compiling a list of software and versions installed on the machine.
Anti-analysis tactics
The downloaded Amber Albatross installation and PyInstaller files require specific command-line parameters in order to fully execute. We have consistently observed the arguments --safetorun and --channel=<hex numbers>. The numbers included in the --channel= flag vary by infection.
The requirement for command-line arguments has prevented behavioral analysis from showing the last-stage PyInstaller binary. For example, the PyInstaller files are rarely found on VirusTotal. This is because when the earlier-stage files are uploaded to VirusTotal, they do not have arguments passed with them to the sandbox engines.
Additionally, we do not observe the same behavior from the PC App Store installer in sandboxes as we do in live telemetry. This indicates there is some anti-sandbox analysis happening with the initial installer, making it difficult to observe the entire infection chain in a controlled environment.
The final-stage PyInstaller file that performs the reconnaissance activities is protected by Pyarmor, which encrypts and obfuscates the Python bytecode. This makes static analysis a challenging and time consuming endeavor.
One of the best ways to prevent threats like Amber Albatross from executing in your environment is to restrict third-party app stores like PC App Store. Red Canary classifies PC App Store as a PUP and detects it as such. While PUPs are a lower priority for many teams, restricting their use can prevent possible credential theft and the leaking of sensitive company data.
Amber Albatross uses a variety of certificates to sign the first and second-stage installer files, which can be used for detection.
Certificates used by Amber Albatross in 2025
| Name | Issuer | Valid From | Valid To | Thumbprint |
| AL STARE LLC | GlobalSign GCC R45 EV CodeSigning CA 2020 | 2024/04/09 | 2025/04/10 | 2defd4d6cbb10b7afd9b5a3dbd61e756549ee3cb |
| IBRAHIM MANNAN LLC | GlobalSign GCC R45 EV CodeSigning CA 2020 | 2024/04/16 | 2025/04/17 | 5ad122b091c21eb546dfd20086d266e0e8429abf |
| UTILITY ACCESS (SMC-PRIVATE) LIMITED | GlobalSign GCC R45 EV CodeSigning CA 2020 | 2024/04/18 | 2025/04/19 | e6454be52b74dec4a3c5048a2398bc73d3e38176 |
| UTILITY ACCESS (SMC-PRIVATE) LIMITED | GlobalSign GCC R45 EV CodeSigning CA 2020 | 2024/09/26 | 2025/09/27 | 24097fb790d82fe390b9dcb3456675f96cef4b2b |
| THE-SHOP STOP LLC | GlobalSign GCC R45 EV CodeSigning CA 2020 | 2024/10/02 | 2025/10/03 | 3acf161dc680cb52bdcf3227248e933de361bd48 |
| SEELIV (SMC-PRIVATE) LIMITED | GlobalSign GCC R45 EV CodeSigning CA 2020 | 2024/10/09 | 2025/10/10 | 77e3b1710323f25812a7af8d2a6a5c6a743dc25f |
| Called Sparkline LLC | GlobalSign GCC R45 EV CodeSigning CA 2020 | 2024/12/20 | 2025/12/21 | b30f77a8bc06aada08b76e9176c3c15e7c9c49ff |
| VALUELYTIC AGRO PRIVATE LIMITED | GlobalSign GCC R45 CodeSigning CA 2020 | 2025/02/13 | 2026/02/14 | bc529da04d69ef981c4b1d3baba73177348e7ee4 |
| DREAMVESSELS TECHNOLOGY PRIVATE LIMITED | GlobalSign GCC R45 CodeSigning CA 2020 | 2025/02/20 | 2026/02/21 | 499e0e8f6d3c5c233a06d94fd476efda36248f50 |
| KRZADROPSHIP PRIVATE LIMITED | GlobalSign GCC R45 CodeSigning CA 2020 | 2025/02/20 | 2026/02/21 | 6f62a79fa9d18994cbb569dbf9e4d87ee04e26f8 |
| Fahad Malik | SSL.com Code Signing Intermediate CA RSA R1 | 2025/04/09 | 2026/04/09 | 632f7439652e088c95967b21ce88ede6e453899a |
Amber Albatross’s command and control uses a variety of domains. Some are consistent across years while others are quickly rotated out. These occasionally relate to one of the delivery lures, but more often do not.
10 most recently observed domains contacted by Amber Albatross
field-for-ever[.]comuser[.]flypdfy[.]comsearcherfest[.]comwellsearching[.]comgoaroundrio[.]comdotspoint[.]comsearchresultfind[.]comconf-file[.]comsearcherzone[.]comsearcherspot[.]com
Testing
Start testing your defenses against Amber Albatross using Atomic Red Team—an open source testing framework of small, highly portable detection tests mapped to MITRE ATT&CK.
Getting started
Amber Albatross exhibits behaviors represented by the following Atomic Red Team tests:
- T1027 #2 – Execute Base64-encoded PowerShell
- T1497.001 #5 – Detect virtualization environment via WMI Manufacturer/Model Listing (Windows)
Review and repeat
Now that you have executed one or several common tests and checked for the expected results, it’s useful to answer some immediate questions:
- Were any of your actions detected?
- Were any of your actions blocked or prevented?
- Were your actions visible in logs or other defensive telemetry?
Repeat this process, performing additional tests related to this technique. You can also create and contribute tests of your own.