SecOps overview
Security operations (SecOps) encompasses the set of functions used to monitor and improve an organization’s security posture while preventing, detecting, and responding to cybersecurity incidents.
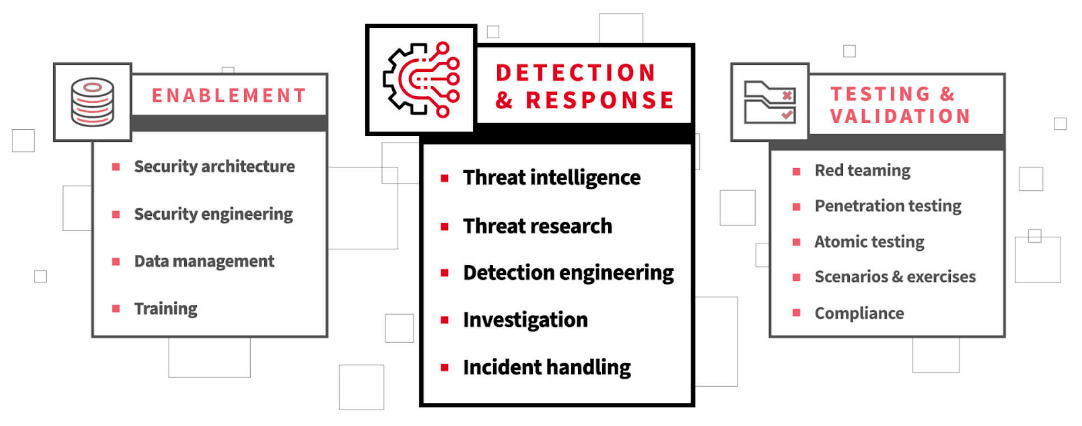
Modern security operations are comprised of three functional areas (detailed below):
Depending on the size of your organization, there may be one person or a team of hundreds officially tasked with executing security operations, but every single employee contributes to the organization’s overall security posture, underscoring the importance of user education.
Keep in mind that security operations is only one component of effective risk management—a discipline grounded in compromise. Ultimately, your order of operations—including whether you choose to engage in some of these activities at all—should be informed first by business objectives. Given clear objectives, you can focus intently and effectively on prioritization, implementation, and refinement.
SecOps benefits
SecOps offers numerous benefits that enhance an organization’s overall cybersecurity posture and resilience.
Risk mitigation
SecOps enables proactive identification and mitigation of security risks, reducing the likelihood of security breaches and data compromises, including particularly costly events such as ransomware or extortion.
Threat detection and incident response
SecOps provides a formalized mechanism for detecting and responding to cyber threats that have evaded your organization’s security controls.
Benefits to the overall business
Over time, the adoption and operationalization of SecOps principles leads to improved agility, resilience, and trustworthiness in all aspects of the business, from software development and delivery to customer-facing operations, ultimately benefiting the organization’s reputation and bottom line.
SecOps challenges
SecOps faces several significant challenges in effectively integrating security practices into the software development and operations processes.
Managing multiple domains
One key challenge is the complexity of modern IT environments, which often consist of diverse technologies, platforms, and infrastructures. SecOps teams must navigate this complexity to identify and mitigate security risks across multiple layers of the technology stack, including applications, networks, and cloud services.
The rapidly changing threat landscape
Keeping up with the rapid pace of technological change and emerging threats requires continuous learning and adaptation, placing strain on SecOps resources and expertise.
Collaboration between teams
Another challenge is the cultural shift required to promote collaboration and communication between security, development, and operations teams. Traditional organizational silos and competing priorities can hinder the adoption of SecOps practices, as security requirements may be perceived as obstacles to the speed and agility of software delivery. Overcoming these cultural barriers requires leadership support, clear communication of security objectives, and fostering a shared understanding of the importance of security across the entire organization.
Skill gap and resource restraints
Additionally, integrating security into automated DevOps workflows requires coordination and alignment between development and security teams, which may require investment in training and tools to facilitate collaboration and integration.
SecOps vs SOC
If SecOps is the set of functions that an organization uses to keep its data secure, the security operations center, or SOC, is the team responsible for those functions. Some SOCs are physically centralized and operate from a shared space, but most operate using a hybrid model or are fully remote.
The security operations center (SOC) encompasses the team or teams responsible for monitoring and improving an organization’s security posture while preventing, detecting, and responding to cybersecurity incidents.
SOC components
The components of a modern security operations center
Detection and response
The following detection and response functions are the focal point of SecOps:
- threat intelligence
- threat research
- threat hunting
- detection engineering
- investigation
- incident handling
While these functions are distinct from one another, they must be tightly integrated within an organization. Often, these functions rely on one another to a certain extent, with one function informing the actions taken in the next function. To achieve tighter alignment, or in the interest of meeting budgetary constraints, organizations often opt to combine these functions or outsource them to third parties.
Enablement
Enablement functions exist to put the core detection and response functions in a position to do what they need to do—detect and respond to threats. And if detection and response is expected to maintain quality at scale, enablement functions are a necessity. Key enablement functions are:
- security architecture
- security engineering
- data management
- training
Testing and validation
Maintaining modern security operations calls for consistent testing and regular refinement. As you implement any system or process, and particularly as it scales, you need to be able to validate the results. In the context of security operations, practitioners engage in a number of activities aimed at achieving some level of validation. Some of these activities are forms of testing performed by internal or external teams. Other activities are focused first on validation—through the review of evidence—often in the form of the various outputs that security operations produce.
This is to say that there are a wide range of approaches to testing and validating security operations. And this list is not intended to be exhaustive, but rather, captures some of the most common methods:
- red teaming
- penetration testing
- atomic testing
- scenarios and exercises
- compliance
SecOps technology and services
Technology and tools commonly leveraged as part of your organization’s security stack may include:
- security information and event management (SIEM) tools
- vulnerability management tools
- network security tools, including firewalls, proxy servers, network detection and response (NDR), and network admission control (NAC)
- endpoint security tools, including endpoint detection and response (EDR), or endpoint protection (EPP)
- identity security tools, including identity and access management (IAM) and privileged access management (PAM)
- threat intelligence platforms
- cloud security tools, including posture management (CSPM) and runtime or workload monitoring
- emulation and testing tools such as Atomic Red Team
Managed detection and response (MDR) is by far the most comprehensive solution or service for operationalizing your security operations functions. MDR providers monitor, detect, and respond to threats identified using the technologies listed above.
SecOps vs. DevOps vs. DevSecOps
SecOps, DevOps, and SecDevOps are all methodologies aimed at improving collaboration and integration between software development (Dev) and IT operations (Ops) teams. Each approach has its own focus and objectives, though they share common goals of enhancing efficiency, agility, and security in software development and deployment processes.
DevOps, short for development and operations, is a software development methodology that emphasizes collaboration and communication between software developers and IT operations professionals. The primary goal of DevOps is to automate and streamline the processes of software delivery and infrastructure changes, enabling faster and more reliable software releases. DevOps practices typically involve continuous integration (CI), continuous delivery (CD), automated testing, and infrastructure as code (IaC).
SecOps, or security operations, extends the principles of DevOps to include security considerations throughout the software development lifecycle. In SecOps, security is integrated into every stage of development and operations processes, from design and development to deployment and monitoring. The focus is on proactively identifying and addressing security risks and vulnerabilities, rather than treating security as an afterthought. SecOps practices often involve threat modeling, security testing, vulnerability scanning, and security automation.
SecDevOps, also known as DevSecOps or Security DevOps, is an extension of DevOps that places a specific emphasis on integrating security practices into the DevOps workflow. SecDevOps combines the principles of DevOps with a security-first mindset, ensuring that security is prioritized throughout the software development lifecycle. Unlike SecOps, which focuses primarily on operational security, SecDevOps emphasizes embedding security controls directly into the development process. This approach aims to minimize security vulnerabilities and risks by integrating security measures into the CI/CD pipeline, automating security testing, and fostering a culture of shared responsibility for security among developers and operations teams.
In short, while DevOps focuses on streamlining software delivery and operations, SecOps emphasizes operational security, and SecDevOps integrates security practices directly into the DevOps workflow to enhance both agility and security.
SecOps in the cloud
The cloud has significantly impacted information technology (IT) and security organizations, streamlining many processes, and introducing the concept of shared responsibility to both IT and SecOps. There are two prevailing cloud technology adoption models:
- Hybrid cloud, combining public and private cloud resources (to include on-premise or traditional resources), offers organizations a means of transitioning into the cloud from their existing infrastructure. While providing some obvious benefits, including the ability to migrate existing technology and systems at the organization’s desired pace, it also poses challenges in maintaining consistent visibility and control across diverse environments.
- Multicloud, in contrast, offers flexibility and avoids vendor lock-in by leveraging multiple cloud providers. Securing multicloud environments demands rigorous IAM policies, data encryption, and regular security assessments to mitigate risks effectively.
Despite their differences, both hybrid and multicloud environments necessitate unified security policies, centralized management, and continuous monitoring to safeguard against evolving threats and ensure compliance. In particular, operationalizing security in cloud environments requires an understanding of each cloud provider’s security concepts, controls, and their unique approaches to shared responsibility for securing resources within their platform. To help customers standardize their approach to cloud security, and to provide features that individual cloud providers do not or cannot, cloud detection and response (CDR) offerings have emerged.
How Red Canary can help with your SecOps
Red Canary MDR combines trailblazing security technology and human expertise to detect threats earlier and stop them faster across your IT environment. Instead of relying solely on alerts, we leverage the power of human expertise and threat intelligence to provide deeper context and analysis. Our dedicated team of security experts actively hunts for threats across your endpoints, network, cloud, identities, and SaaS applications, 24/7. This proactive approach ensures fast responses, reduces false positives and alert fatigue, and detects threats other tools miss.
Learn More
Red Canary detects threats no one else does, and we do it 24/7 across your endpoints, network, cloud workloads, identities, and SaaS apps.